Security Protocols I - Information Security
Security Protocols I - Information Security
Security Protocols I - Information Security
You also want an ePaper? Increase the reach of your titles
YUMPU automatically turns print PDFs into web optimized ePapers that Google loves.
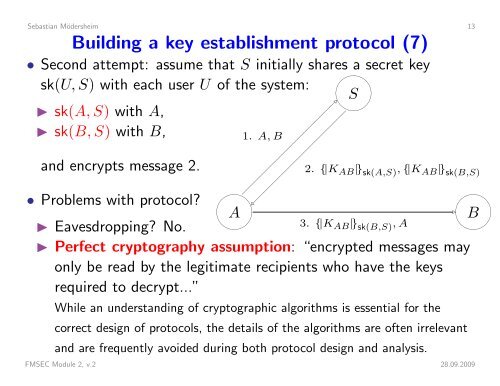
Sebastian Mödersheim 13Building a key establishment protocol (7)• Second attempt: assume that S initially shares a secret keysk(U, S) with each user U of the system: S◮ sk(A, S) with A,◮ sk(B, S) with B,1. A, Band encrypts message 2.2. {|K AB |} sk(A,S) , {|K AB |} sk(B,S)• Problems with protocol? A◮ Eavesdropping? No.3. {|K AB |} sk(B,S) , A◮ Perfect cryptography assumption: “encrypted messages mayonly be read by the legitimate recipients who have the keysrequired to decrypt...”While an understanding of cryptographic algorithms is essential for thecorrect design of protocols, the details of the algorithms are often irrelevantand are frequently avoided during both protocol design and analysis. BFMSEC Module 2, v.2 28.09.2009