Security Protocols I - Information Security
Security Protocols I - Information Security
Security Protocols I - Information Security
You also want an ePaper? Increase the reach of your titles
YUMPU automatically turns print PDFs into web optimized ePapers that Google loves.
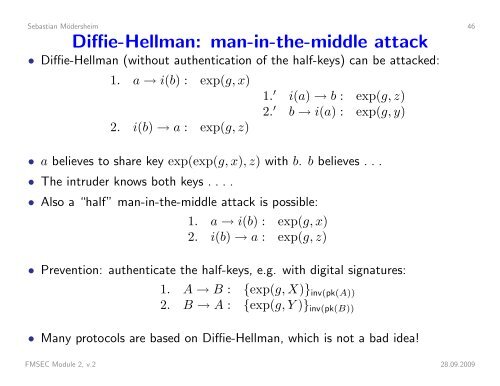
Sebastian Mödersheim 46Diffie-Hellman: man-in-the-middle attack• Diffie-Hellman (without authentication of the half-keys) can be attacked:1. a → i(b) : exp(g, x)2. i(b) → a : exp(g, z)1. ′ i(a) → b : exp(g, z)2. ′ b → i(a) : exp(g, y)• a believes to share key exp(exp(g, x), z) with b. b believes . . .• The intruder knows both keys . . . .• Also a “half” man-in-the-middle attack is possible:1. a → i(b) : exp(g, x)2. i(b) → a : exp(g, z)• Prevention: authenticate the half-keys, e.g. with digital signatures:1. A → B : {exp(g, X)} inv(pk(A))2. B → A : {exp(g, Y )} inv(pk(B))• Many protocols are based on Diffie-Hellman, which is not a bad idea!FMSEC Module 2, v.2 28.09.2009