Smart Industry 1/2016
Smart Industry 1/2016 - The IoT Business Magazine - powered by Avnet Silica
Smart Industry 1/2016 - The IoT Business Magazine - powered by Avnet Silica
You also want an ePaper? Increase the reach of your titles
YUMPU automatically turns print PDFs into web optimized ePapers that Google loves.
a word of warning from the fBI<br />
A public service announcement by<br />
the Federal Bureau of Investigation<br />
released last September details a<br />
number of specific IoT risks, and it<br />
warns companies and the general<br />
public to be aware of new vulnerabilities<br />
that cybercriminals could<br />
exploit. Specifically, the FBI worries<br />
that exploiting the Universal Plug<br />
and Play protocol (UPnP) widely used<br />
in many modern IoT devices will be<br />
a pathway of choice for many cybercriminals.<br />
UPnP is a set of networking<br />
protocols that permits networked<br />
devices to seamlessly discover each<br />
other’s presence on the network and<br />
establish functional network services<br />
for data sharing, communications,<br />
and entertainment. Unfortunately,<br />
UPnP was originally intended only<br />
for residential networks and not<br />
for enterprise-class devices. Crooks<br />
could also exploit default passwords<br />
to send malicious code and spam<br />
mails or to steal personally identifiable<br />
or credit card information. Other<br />
scenarios to Feds worry about are<br />
the possibility of compromising IoT<br />
device to cause physical harm, to<br />
overload them, thus rendering them<br />
inoperable, and to intercept and interfere<br />
with business transactions.<br />
On the other hand security leaks<br />
could be used by intelligence services<br />
to get access to areas of interest.<br />
James R. Clapper Director of US<br />
National Intelligence has made an<br />
according statement in the report<br />
“Worldwide Threat Assessment of<br />
the US Intelligence Community”,<br />
published in February <strong>2016</strong>: “<strong>Smart</strong><br />
devices incorporated into the electric<br />
grid, vehicles – including autonomous<br />
vehicles – and household appliances<br />
are improving efficiency, energy<br />
conservation, and convenience.<br />
However, security industry analysts<br />
have demonstrated that many of<br />
these new systems can threaten data<br />
privacy, data integrity, or continuity<br />
of services. In the future, intelligence<br />
services might use the IoT for identification,<br />
surveillance, monitoring,<br />
location tracking, and targeting for<br />
recruitment, or to gain access to networks<br />
or user credentials.”<br />
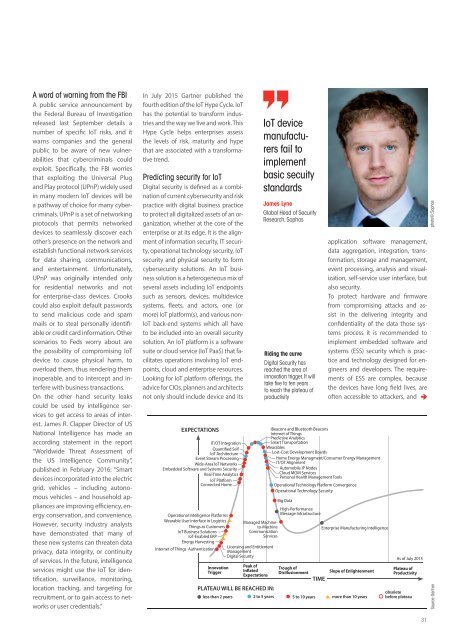
In July 2015 Gartner published the<br />
fourth edition of the IoT Hype Cycle. IoT<br />
has the potential to transform industries<br />
and the way we live and work. This<br />
Hype Cycle helps enterprises assess<br />
the levels of risk, maturity and hype<br />
that are associated with a transformative<br />
trend.<br />
Predicting security for Iot<br />
Digital security is defined as a combination<br />
of current cybersecurity and risk<br />
practice with digital business practice<br />
to protect all digitalized assets of an organization,<br />
whether at the core of the<br />
enterprise or at its edge. It is the alignment<br />
of information security, IT security,<br />
operational technology security, IoT<br />
security and physical security to form<br />
cybersecurity solutions. An IoT business<br />
solution is a heterogeneous mix of<br />
several assets including IoT endpoints<br />
such as sensors, devices, multidevice<br />
systems, fleets, and actors, one (or<br />
more) IoT platform(s), and various non-<br />
IoT back-end systems which all have<br />
to be included into an overall security<br />
solution. An IoT platform is a software<br />
suite or cloud service (IoT PaaS) that facilitates<br />
operations involving IoT endpoints,<br />
cloud and enterprise resources.<br />
Looking for IoT platform offerings, the<br />
advice for CIOs, planners and architects<br />
not only should include device and its<br />
EXPECTATIONS<br />
IT/OT Integration<br />
Quantified Self<br />
IoT Architecture<br />
Event Stream Processing<br />
Wide-Area IoT Networks<br />
Embedded Software and Systems Security<br />
Real-Time Analytics<br />
IoT Platform<br />
Connected Home<br />
Operational Intelligence Platforms<br />
Wearable User Interface in Logistics<br />
Things as Customers<br />
IoT Business Solutions<br />
IoT-Enabled ERP<br />
Energy Harvesting<br />
Internet of Things Authentication<br />
Innovation<br />
Trigger<br />
Managed Machineto-Machine<br />
Communication<br />
Services<br />
Licensing and Entitlement<br />
Management<br />
Digital Security<br />
Peak of<br />
Inflated<br />
Expectations<br />
Iot device<br />
manufacturers<br />
fail to<br />
implement<br />
basic secuity<br />
standards<br />
James Lyne<br />
Global Head of Security<br />
Research, Sophos<br />
Riding the curve<br />
Digital Security has<br />
reached the area of<br />
innovation trigger. It will<br />
take fi ve to ten years<br />
to reach the plateau of<br />
productivity<br />
iBeacons and Bluetooth Beacons<br />
Internet of Things<br />
Predictive Analytics<br />
<strong>Smart</strong> Transportation<br />
Wearables<br />
Lost-Cost Development Boards<br />
Home Energy Managment/Consumer Energy Management<br />
IT/OT Alignment<br />
Automobile IP Nodes<br />
Cloud MOM Services<br />
Personal Health Management Tools<br />
Operational Technology Platform Convergence<br />
Operational Technology Security<br />
Big Data<br />
High-Performance<br />
Message Infrastructure<br />
Trough of<br />
Disillusionment<br />
Enterprise Manufacturing Intelligence<br />
Slope of Enlightenment<br />
TIME<br />
PLATEAU WILL BE REACHED IN:<br />
less than 2 years 2 to 5 years 5 to 10 years more than 10 years<br />
application software management,<br />
data aggregation, integration, transformation,<br />
storage and management,<br />
event processing, analysis and visualization,<br />
self-service user interface, but<br />
also security.<br />
To protect hardware and firmware<br />
from compromising attacks and assist<br />
in the delivering integrity and<br />
confidentiality of the data those systems<br />
process it is recommended to<br />
implement embedded software and<br />
systems (ESS) security which is practice<br />
and technology designed for engineers<br />
and developers. The requirements<br />
of ESS are complex, because<br />
the devices have long field lives, are<br />
often accessible to attackers, and<br />
As of July 2015<br />
Plateau of<br />
Productivity<br />
obsolete<br />
before plateau<br />
photo©: Sophos<br />
Source: Gartner<br />
31