New Statistical Algorithms for the Analysis of Mass - FU Berlin, FB MI ...
New Statistical Algorithms for the Analysis of Mass - FU Berlin, FB MI ...
New Statistical Algorithms for the Analysis of Mass - FU Berlin, FB MI ...
You also want an ePaper? Increase the reach of your titles
YUMPU automatically turns print PDFs into web optimized ePapers that Google loves.
118 CHAPTER 5. COMPUTER SCIENCE GRID STRATEGIES<br />
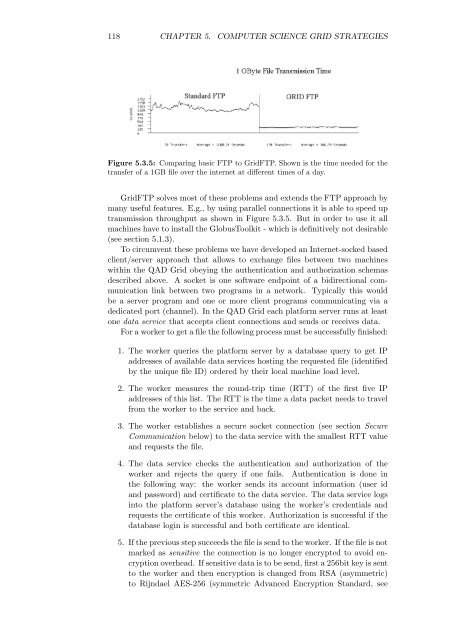
Figure 5.3.5: Comparing basic FTP to GridFTP. Shown is <strong>the</strong> time needed <strong>for</strong> <strong>the</strong><br />
transfer <strong>of</strong> a 1GB file over <strong>the</strong> internet at different times <strong>of</strong> a day.<br />
GridFTP solves most <strong>of</strong> <strong>the</strong>se problems and extends <strong>the</strong> FTP approach by<br />
many useful features. E.g., by using parallel connections it is able to speed up<br />
transmission throughput as shown in Figure 5.3.5. But in order to use it all<br />
machines have to install <strong>the</strong> GlobusToolkit - which is definitively not desirable<br />
(see section 5.1.3).<br />
To circumvent <strong>the</strong>se problems we have developed an Internet-socked based<br />
client/server approach that allows to exchange files between two machines<br />
within <strong>the</strong> QAD Grid obeying <strong>the</strong> au<strong>the</strong>ntication and authorization schemas<br />
described above. A socket is one s<strong>of</strong>tware endpoint <strong>of</strong> a bidirectional communication<br />
link between two programs in a network. Typically this would<br />
be a server program and one or more client programs communicating via a<br />
dedicated port (channel). In <strong>the</strong> QAD Grid each plat<strong>for</strong>m server runs at least<br />
one data service that accepts client connections and sends or receives data.<br />
For a worker to get a file <strong>the</strong> following process must be successfully finished:<br />
1. The worker queries <strong>the</strong> plat<strong>for</strong>m server by a database query to get IP<br />
addresses <strong>of</strong> available data services hosting <strong>the</strong> requested file (identified<br />
by <strong>the</strong> unique file ID) ordered by <strong>the</strong>ir local machine load level.<br />
2. The worker measures <strong>the</strong> round-trip time (RTT) <strong>of</strong> <strong>the</strong> first five IP<br />
addresses <strong>of</strong> this list. The RTT is <strong>the</strong> time a data packet needs to travel<br />
from <strong>the</strong> worker to <strong>the</strong> service and back.<br />
3. The worker establishes a secure socket connection (see section Secure<br />
Communication below) to <strong>the</strong> data service with <strong>the</strong> smallest RTT value<br />
and requests <strong>the</strong> file.<br />
4. The data service checks <strong>the</strong> au<strong>the</strong>ntication and authorization <strong>of</strong> <strong>the</strong><br />
worker and rejects <strong>the</strong> query if one fails. Au<strong>the</strong>ntication is done in<br />
<strong>the</strong> following way: <strong>the</strong> worker sends its account in<strong>for</strong>mation (user id<br />
and password) and certificate to <strong>the</strong> data service. The data service logs<br />
into <strong>the</strong> plat<strong>for</strong>m server’s database using <strong>the</strong> worker’s credentials and<br />
requests <strong>the</strong> certificate <strong>of</strong> this worker. Authorization is successful if <strong>the</strong><br />
database login is successful and both certificate are identical.<br />
5. If <strong>the</strong> previous step succeeds <strong>the</strong> file is send to <strong>the</strong> worker. If <strong>the</strong> file is not<br />
marked as sensitive <strong>the</strong> connection is no longer encrypted to avoid encryption<br />
overhead. If sensitive data is to be send, first a 256bit key is sent<br />
to <strong>the</strong> worker and <strong>the</strong>n encryption is changed from RSA (asymmetric)<br />
to Rijndael AES-256 (symmetric Advanced Encryption Standard, see