Caché Installation Guide - InterSystems Documentation
Caché Installation Guide - InterSystems Documentation
Caché Installation Guide - InterSystems Documentation
Create successful ePaper yourself
Turn your PDF publications into a flip-book with our unique Google optimized e-Paper software.
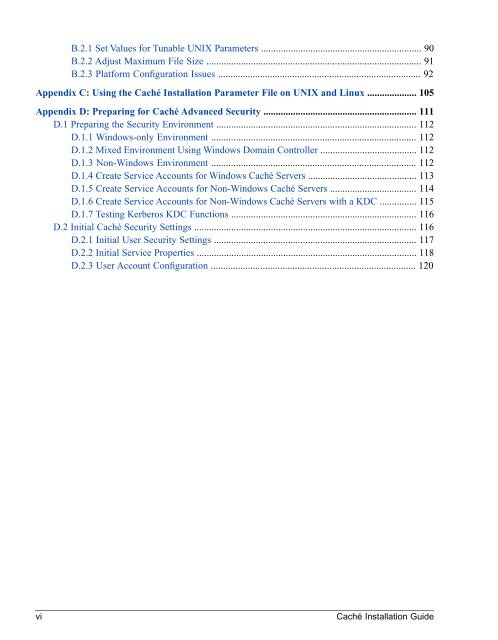
B.2.1 Set Values for Tunable UNIX Parameters ................................................................. 90<br />
B.2.2 Adjust Maximum File Size ....................................................................................... 91<br />
B.2.3 Platform Configuration Issues .................................................................................. 92<br />
Appendix C: Using the <strong>Caché</strong> <strong>Installation</strong> Parameter File on UNIX and Linux .................... 105<br />
Appendix D: Preparing for <strong>Caché</strong> Advanced Security .............................................................. 111<br />
D.1 Preparing the Security Environment ................................................................................. 112<br />
D.1.1 Windows-only Environment ................................................................................... 112<br />
D.1.2 Mixed Environment Using Windows Domain Controller ....................................... 112<br />
D.1.3 Non-Windows Environment ................................................................................... 112<br />
D.1.4 Create Service Accounts for Windows <strong>Caché</strong> Servers ............................................ 113<br />
D.1.5 Create Service Accounts for Non-Windows <strong>Caché</strong> Servers ................................... 114<br />
D.1.6 Create Service Accounts for Non-Windows <strong>Caché</strong> Servers with a KDC ............... 115<br />
D.1.7 Testing Kerberos KDC Functions ........................................................................... 116<br />
D.2 Initial <strong>Caché</strong> Security Settings .......................................................................................... 116<br />
D.2.1 Initial User Security Settings .................................................................................. 117<br />
D.2.2 Initial Service Properties ......................................................................................... 118<br />
D.2.3 User Account Configuration ................................................................................... 120<br />
vi<br />
<strong>Caché</strong> <strong>Installation</strong> <strong>Guide</strong>