- Page 1 and 2:
UNIVERSITY OF ATHENS DEPARTMENT OF
- Page 3 and 4:
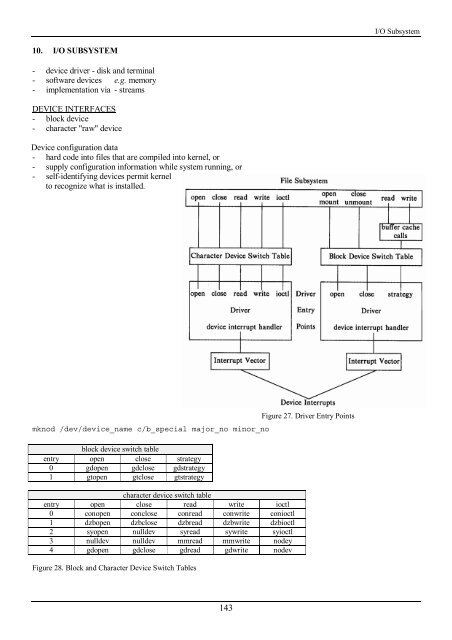
Figure 27. Driver Entry Points.....
- Page 5 and 6:
Introduction to Unix ! Execution ma
- Page 7 and 8:
Introduction to Unix It works in th
- Page 9 and 10:
Introduction to Unix * matches 0 or
- Page 11 and 12:
Introduction to Unix vi file-name s
- Page 13 and 14:
Introduction to Unix 1,$s/^/>>/ 1,$
- Page 15 and 16:
Introduction to Unix ! Special Devi
- Page 17 and 18:
Introduction to Unix Working with F
- Page 19 and 20:
Introduction to Unix ! Communicatio
- Page 21 and 22:
Unix Shells 2. UNIX SHELLS Back Quo
- Page 23 and 24:
Unix Shells ! CASE Statement case t
- Page 25 and 26:
Unix Shells two lines !Y@Y@Z@Z@ZY c
- Page 27 and 28:
Unix Shells if $append then tee -a
- Page 29 and 30:
C Programming - Basics main() { int
- Page 31 and 32:
C Programming - Basics e.g. i += 2
- Page 33 and 34:
External Variables A C program cons
- Page 35 and 36:
C Programming - Basics main.c #incl
- Page 37 and 38:
C Programming - Basics default: pri
- Page 39 and 40:
C Programming - Basics struct tnode
- Page 41 and 42:
Unix Tools 4. UNIX TOOLS Tools of t
- Page 43 and 44:
Unix Tools Korn shell ! .profile HI
- Page 45 and 46:
Unix Tools grep "$name" $PHONEBOOK
- Page 47 and 48:
Unix Tools awk '$3 > 0 { print $1,
- Page 49 and 50:
Unix Tools END { print max, maxline
- Page 51 and 52:
Unix Tools Let an example input fil
- Page 53 and 54:
Unix Tools Brown eqn 1 # output Jon
- Page 55 and 56:
Development Tools Make looks at the
- Page 57 and 58:
Development Tools /* compute size o
- Page 59 and 60:
Development Tools #endif #line cons
- Page 61 and 62:
Development Tools 1.1 5 lines Retri
- Page 63 and 64:
Development Tools In Emacs, you may
- Page 65 and 66:
Development Tools */ %{ #define YYS
- Page 67 and 68:
C Libraries 6. C LIBRARIES Input an
- Page 69 and 70:
C Libraries } while (!feof(fp1)) pu
- Page 71 and 72:
C Libraries } free(p); /* what is w
- Page 73 and 74:
C Libraries } if ((fp->flag&( _READ
- Page 75 and 76:
C Libraries /* dirwalk: apply fcn t
- Page 77 and 78:
C Libraries } switch (pid=fork()){
- Page 79 and 80:
C Libraries What is curses? - libra
- Page 81 and 82:
C Libraries } if ((fd=fopen(argv[1]
- Page 83 and 84:
Introduction to kernel 7. INTRODUCT
- Page 85 and 86:
82 Introduction to kernel Programs
- Page 87 and 88:
Introduction to kernel } { printf("
- Page 89 and 90:
Introduction to kernel The kernel r
- Page 91 and 92:
Introduction to kernel UNIX Interna
- Page 93 and 94:
Introduction to kernel File System
- Page 95 and 96: Introduction to kernel Every proces
- Page 97 and 98: Processes I Process States 1. Execu
- Page 99 and 100: Processes I } printf("%d %s\n", cnt
- Page 101 and 102: Processes I dup (and other similar
- Page 103 and 104: Processes I The u area contains - p
- Page 105 and 106: Processes I The Context of a Proces
- Page 107 and 108: Processes I Process Control use and
- Page 109 and 110: Processes I Although the processes
- Page 111 and 112: Processes I Handling Signals - proc
- Page 113 and 114: Processes I USER=neville PATH=/user
- Page 115 and 116: Processes I ! Shadow Password /etc/
- Page 117 and 118: struct timeval { long tv_sec; /* se
- Page 119 and 120: Processes I F_SETFL set status flag
- Page 121 and 122: Processes I process is the child pr
- Page 123 and 124: Processes I Rules about sharing of
- Page 125 and 126: Processes II 9. PROCESSES (II) FORK
- Page 127 and 128: Processes II /* background.c */ #in
- Page 129 and 130: Processes II } while (1){ printf("p
- Page 131 and 132: Processes II } /* child */ signal (
- Page 133 and 134: Processes II int readline(int fd, c
- Page 135 and 136: Processes II { } char process_name[
- Page 137 and 138: Processes II - Pipe in a single pro
- Page 139 and 140: Processes II System V IPC - message
- Page 141 and 142: Processes II int msgctl(int msqid,
- Page 143 and 144: Processes II For every semop operat
- Page 145: Processes II /* client loop */ mesg
- Page 149 and 150: I/O Subsystem Terminal Drivers - In
- Page 151 and 152: I/O Subsystem Canonical Mode algori
- Page 153 and 154: I/O Subsystem Raw Mode Raw mode is
- Page 155 and 156: Figure 43. Pushing a Module onto a
- Page 157 and 158: Interprocess Communication } { ptra
- Page 159 and 160: Interprocess Communication T ID KEY
- Page 161 and 162: Interprocess Communication }; int m
- Page 163 and 164: Interprocess Communication for (i=0
- Page 165 and 166: Interprocess Communication /* struc
- Page 167 and 168: Interprocess Communication ! Compar
- Page 169 and 170: … connect(sockfd,(struct sockaddr
- Page 171 and 172: Interprocess Communication Address
- Page 173 and 174: Process Scheduling Page Tables and
- Page 176 and 177: Figure 49. Tie breaker rule Process
- Page 178 and 179: Process Scheduling Clock - restart
- Page 180 and 181: Process Scheduling Figure 57. Mappi
- Page 182 and 183: Figure 62. Sequence of Swapping Ope
- Page 184 and 185: Buffer Cache The kernel takes buffe
- Page 186 and 187: Buffer Cache The kernel places the
- Page 188 and 189: Buffer Cache Process B will find th
- Page 190 and 191: Unix Administration 14. UNIX ADMINI
- Page 192 and 193: Unix Administration Example output
- Page 194 and 195: Unix Administration *) IN=-mtime -2
- Page 196 and 197:
Unix Administration Load /Unix kern
- Page 198 and 199:
Unix Administration for (i=0; i&i d
- Page 200 and 201:
Unix Administration fi done echo $s
- Page 202 and 203:
Unix Administration New Software !
- Page 204 and 205:
Unix Security Example: group name:g
- Page 206 and 207:
Unix Security $ crypt < exam320.Z >
- Page 208 and 209:
Unix Security - exported filesystem
- Page 210 and 211:
Unix Security system(cmdstr); $ ech
- Page 212:
Unix Security - repairs damaged use