Create successful ePaper yourself
Turn your PDF publications into a flip-book with our unique Google optimized e-Paper software.
<strong>Unix</strong> Security<br />
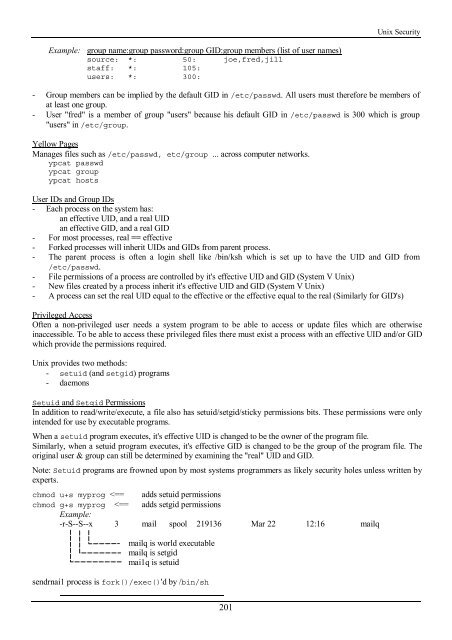
Example: group name:group password:group GID:group members (list of user names)<br />
source: *: 50: joe,fred,jill<br />
staff: *: 105:<br />
users: *: 300:<br />
- Group members can be implied by <strong>the</strong> default GID in /etc/passwd. All users must <strong>the</strong>refore be members of<br />
at least one group.<br />
- User "fred" is a member of group "users" because his default GID in /etc/passwd is 300 which is group<br />
"users" in /etc/group.<br />
Yellow Pages<br />
Manages files such as /etc/passwd, etc/group ... across computer networks.<br />
ypcat passwd<br />
ypcat group<br />
ypcat hosts<br />
User IDs and Group IDs<br />
- Each process on <strong>the</strong> system has:<br />
an effective UID, and a real UID<br />
an effective GID, and a real GID<br />
- For most processes, real == effective<br />
- Forked processes will inherit UIDs and GIDs from parent process.<br />
- The parent process is often a login shell like /bin/ksh which is set up to have <strong>the</strong> UID and GID from<br />
/etc/passwd.<br />
- File permissions of a process are controlled by it's effective UID and GID (System V <strong>Unix</strong>)<br />
- New files created by a process inherit it's effective UID and GID (System V <strong>Unix</strong>)<br />
- A process can set <strong>the</strong> real UID equal to <strong>the</strong> effective or <strong>the</strong> effective equal to <strong>the</strong> real (Similarly for GID's)<br />
Privileged Access<br />
Often a non-privileged user needs a system program to be able to access or update files which are o<strong>the</strong>rwise<br />
inaccessible. To be able to access <strong>the</strong>se privileged files <strong>the</strong>re must exist a process <strong>with</strong> an effective UID and/or GID<br />
which provide <strong>the</strong> permissions required.<br />
<strong>Unix</strong> provides two methods:<br />
- setuid (and setgid) programs<br />
- daemons<br />
Setuid and Setgid Permissions<br />
In addition to read/write/execute, a file also has setuid/setgid/sticky permissions bits. These permissions were only<br />
intended for use by executable programs.<br />
When a setuid program executes, it's effective UID is changed to be <strong>the</strong> owner of <strong>the</strong> program file.<br />
Similarly, when a setuid program executes, it's effective GID is changed to be <strong>the</strong> group of <strong>the</strong> program file. The<br />
original user & group can still be determined by examining <strong>the</strong> "real" UID and GID.<br />
Note: Setuid programs are frowned upon by most systems programmers as likely security holes unless written by<br />
experts.<br />
chmod u+s myprog