You also want an ePaper? Increase the reach of your titles
YUMPU automatically turns print PDFs into web optimized ePapers that Google loves.
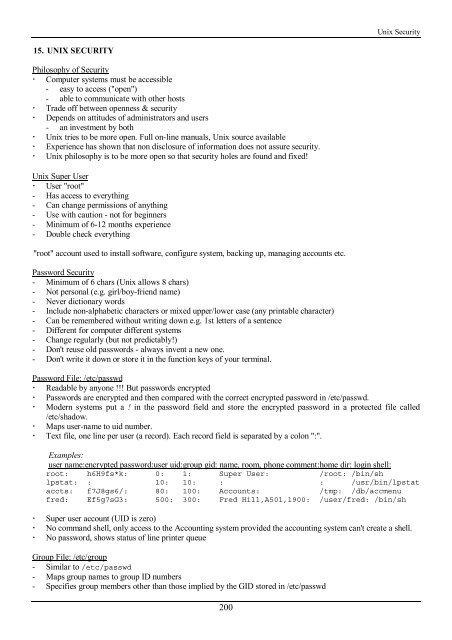
<strong>Unix</strong> Security<br />
15. UNIX SECURITY<br />
Philosophy of Security<br />
! Computer systems must be accessible<br />
- easy to access ("open")<br />
- able to communicate <strong>with</strong> o<strong>the</strong>r hosts<br />
! Trade off between openness & security<br />
! Depends on attitudes of administrators and users<br />
- an investment by both<br />
! <strong>Unix</strong> tries to be more open. Full on-line manuals, <strong>Unix</strong> source available<br />
! Experience has shown that non disclosure of information does not assure security.<br />
! <strong>Unix</strong> philosophy is to be more open so that security holes are found and fixed!<br />
<strong>Unix</strong> Super User<br />
! User "root"<br />
- Has access to everything<br />
- Can change permissions of anything<br />
- Use <strong>with</strong> caution - not for beginners<br />
- Minimum of 6-12 months experience<br />
- Double check everything<br />
"root" account used to install software, configure system, backing up, managing accounts etc.<br />
Password Security<br />
- Minimum of 6 chars (<strong>Unix</strong> allows 8 chars)<br />
- Not personal (e.g. girl/boy-friend name)<br />
- Never dictionary words<br />
- Include non-alphabetic characters or mixed upper/lower case (any printable character)<br />
- Can be remembered <strong>with</strong>out writing down e.g. 1st letters of a sentence<br />
- Different for computer different systems<br />
- Change regularly (but not predictably!)<br />
- Don't reuse old passwords - always invent a new one.<br />
- Don't write it down or store it in <strong>the</strong> function keys of your terminal.<br />
Password File: /etc/passwd<br />
! Readable by anyone !!! But passwords encrypted<br />
! Passwords are encrypted and <strong>the</strong>n compared <strong>with</strong> <strong>the</strong> correct encrypted password in /etc/passwd.<br />
! Modern systems put a ! in <strong>the</strong> password field and store <strong>the</strong> encrypted password in a protected file called<br />
/etc/shadow.<br />
! Maps user-name to uid number.<br />
! Text file, one line per user (a record). Each record field is separated by a colon ":".<br />
Examples:<br />
user name:encrypted password:user uid:group gid: name, room, phone comment:home dir: login shell:<br />
root: h6H9fs*k: 0: 1: Super User: /root: /bin/sh<br />
lpstat: : 10: 10: : : /usr/bin/lpstat<br />
accts: f7J8gs6/: 80: 100: Accounts: /tmp: /db/accmenu<br />
fred: Ef5g7sG3: 500: 300: Fred Hill,A501,1900: /user/fred: /bin/sh<br />
! Super user account (UID is zero)<br />
! No command shell, only access to <strong>the</strong> Accounting system provided <strong>the</strong> accounting system can't create a shell.<br />
! No password, shows status of line printer queue<br />
Group File: /etc/group<br />
- Similar to /etc/passwd<br />
- Maps group names to group ID numbers<br />
- Specifies group members o<strong>the</strong>r than those implied by <strong>the</strong> GID stored in /etc/passwd<br />
200