Trend Micro Mobile Security for Symbian OS/S60 3rd Edition User's ...
Trend Micro Mobile Security for Symbian OS/S60 3rd Edition User's ...
Trend Micro Mobile Security for Symbian OS/S60 3rd Edition User's ...
Create successful ePaper yourself
Turn your PDF publications into a flip-book with our unique Google optimized e-Paper software.
Using the Firewall<br />
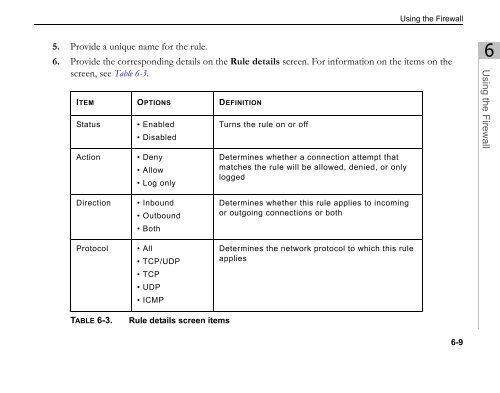
5. Provide a unique name <strong>for</strong> the rule.<br />
6. Provide the corresponding details on the Rule details screen. For in<strong>for</strong>mation on the items on the<br />
screen, see Table 6-3.<br />
ITEM OPTIONS DEFINITION<br />
Status • Enabled<br />
• Disabled<br />
Action • Deny<br />
• Allow<br />
• Log only<br />
Direction • Inbound<br />
• Outbound<br />
• Both<br />
Protocol • All<br />
• TCP/UDP<br />
• TCP<br />
• UDP<br />
• ICMP<br />
TABLE 6-3. Rule details screen items<br />
Turns the rule on or off<br />
Determines whether a connection attempt that<br />
matches the rule will be allowed, denied, or only<br />
logged<br />
Determines whether this rule applies to incoming<br />
or outgoing connections or both<br />
Determines the network protocol to which this rule<br />
applies<br />
6-9<br />
6<br />
Using the Firewall