You also want an ePaper? Increase the reach of your titles
YUMPU automatically turns print PDFs into web optimized ePapers that Google loves.
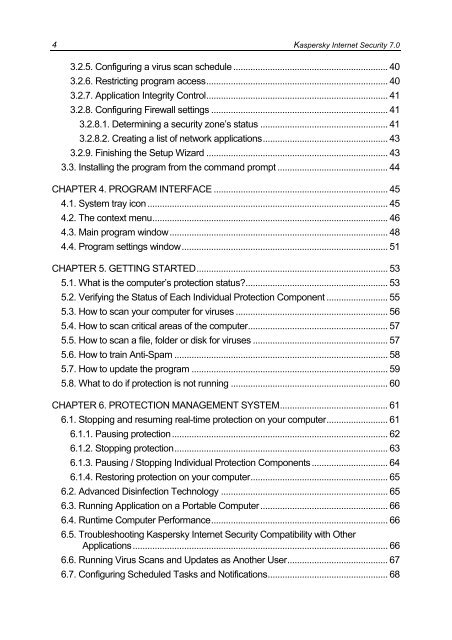
4 <strong>Kaspersky</strong> Internet Security 7.0<br />
3.2.5. Configuring a virus scan schedule ............................................................... 40<br />
3.2.6. Restricting program access.......................................................................... 40<br />
3.2.7. Application Integrity Control.......................................................................... 41<br />
3.2.8. Configuring Firewall settings ........................................................................ 41<br />
3.2.8.1. Determining a security zone’s status .................................................... 41<br />
3.2.8.2. Creating a list of network applications................................................... 43<br />
3.2.9. Finishing the Setup Wizard .......................................................................... 43<br />
3.3. Installing the program from the command prompt ............................................. 44<br />
CHAPTER 4. PROGRAM INTERFACE ....................................................................... 45<br />
4.1. System tray icon .................................................................................................. 45<br />
4.2. The context menu................................................................................................ 46<br />
4.3. Main program window......................................................................................... 48<br />
4.4. Program settings window.................................................................................... 51<br />
CHAPTER 5. GETTING STARTED.............................................................................. 53<br />
5.1. What is the computer’s protection status?.......................................................... 53<br />
5.2. Verifying the Status of Each Individual Protection Component ......................... 55<br />
5.3. How to scan your computer for viruses .............................................................. 56<br />
5.4. How to scan critical areas of the computer......................................................... 57<br />
5.5. How to scan a file, folder or disk for viruses ....................................................... 57<br />
5.6. How to train Anti-Spam ....................................................................................... 58<br />
5.7. How to update the program ................................................................................ 59<br />
5.8. What to do if protection is not running ................................................................ 60<br />
CHAPTER 6. PROTECTION MANAGEMENT SYSTEM............................................ 61<br />
6.1. Stopping and resuming real-time protection on your computer......................... 61<br />
6.1.1. Pausing protection........................................................................................ 62<br />
6.1.2. Stopping protection....................................................................................... 63<br />
6.1.3. Pausing / Stopping Individual Protection Components ............................... 64<br />
6.1.4. Restoring protection on your computer........................................................ 65<br />
6.2. Advanced Disinfection Technology .................................................................... 65<br />
6.3. Running Application on a Portable Computer.................................................... 66<br />
6.4. Runtime Computer Performance........................................................................ 66<br />
6.5. Troubleshooting <strong>Kaspersky</strong> Internet Security Compatibility with Other<br />
Applications........................................................................................................ 66<br />
6.6. Running Virus Scans and Updates as Another <strong>User</strong>......................................... 67<br />
6.7. Configuring Scheduled Tasks and Notifications................................................. 68