You also want an ePaper? Increase the reach of your titles
YUMPU automatically turns print PDFs into web optimized ePapers that Google loves.
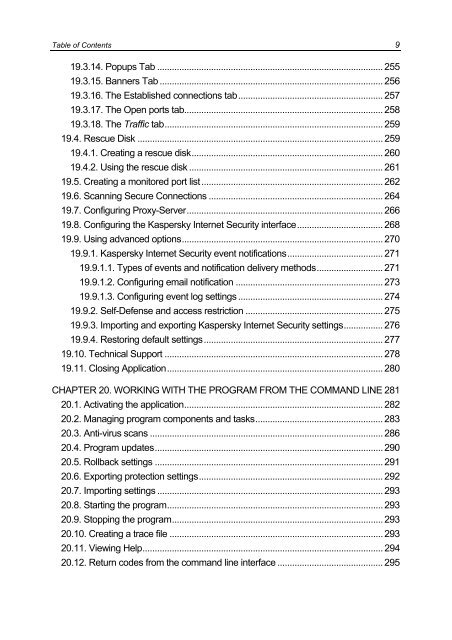
Table of Contents 9<br />
19.3.14. Popups Tab ............................................................................................ 255<br />
19.3.15. Banners Tab ........................................................................................... 256<br />
19.3.16. The Established connections tab........................................................... 257<br />
19.3.17. The Open ports tab................................................................................. 258<br />
19.3.18. The Traffic tab......................................................................................... 259<br />
19.4. Rescue Disk .................................................................................................... 259<br />
19.4.1. Creating a rescue disk.............................................................................. 260<br />
19.4.2. Using the rescue disk ............................................................................... 261<br />
19.5. Creating a monitored port list.......................................................................... 262<br />
19.6. Scanning Secure Connections ....................................................................... 264<br />
19.7. Configuring Proxy-Server................................................................................ 266<br />
19.8. Configuring the <strong>Kaspersky</strong> Internet Security interface................................... 268<br />
19.9. Using advanced options.................................................................................. 270<br />
19.9.1. <strong>Kaspersky</strong> Internet Security event notifications....................................... 271<br />
19.9.1.1. Types of events and notification delivery methods........................... 271<br />
19.9.1.2. Configuring email notification ............................................................ 273<br />
19.9.1.3. Configuring event log settings ........................................................... 274<br />
19.9.2. Self-Defense and access restriction ........................................................ 275<br />
19.9.3. Importing and exporting <strong>Kaspersky</strong> Internet Security settings................ 276<br />
19.9.4. Restoring default settings......................................................................... 277<br />
19.10. Technical Support ......................................................................................... 278<br />
19.11. Closing Application........................................................................................ 280<br />
CHAPTER 20. WORKING WITH THE PROGRAM FROM THE COMMAND LINE 281<br />
20.1. Activating the application................................................................................. 282<br />
20.2. Managing program components and tasks.................................................... 283<br />
20.3. Anti-virus scans ............................................................................................... 286<br />
20.4. Program updates............................................................................................. 290<br />
20.5. Rollback settings ............................................................................................. 291<br />
20.6. Exporting protection settings........................................................................... 292<br />
20.7. Importing settings ............................................................................................ 293<br />
20.8. Starting the program........................................................................................ 293<br />
20.9. Stopping the program...................................................................................... 293<br />
20.10. Creating a trace file ....................................................................................... 293<br />
20.11. Viewing Help.................................................................................................. 294<br />
20.12. Return codes from the command line interface ........................................... 295