- Page 1 and 2:
FTOS Configuration Guide for ® the
- Page 3 and 4:
Table 1 lists the new features in F
- Page 5 and 6:
Table 2 FTOS Features Newly Support
- Page 7 and 8:
Table 4 Newly Supported Hardware in
- Page 9 and 10:
Contents New Features . . . . . . .
- Page 11 and 12:
configure FTP server parameters . .
- Page 13 and 14:
SCP and SSH . . . . . . . . . . . .
- Page 15 and 16:
Configuration Task List for Port Ch
- Page 17 and 18:
enable ICMP redirects . . . . . . .
- Page 19 and 20:
Marking DSCP in Outgoing Packet . .
- Page 21 and 22:
Adding and Removing Interfaces . .
- Page 23 and 24:
General Routing Protocols . . . . .
- Page 25 and 26:
Preface About this Guide Objectives
- Page 27 and 28:
Chapter 1 Configuration Fundamental
- Page 29 and 30:
Figure 2 CLI Modes in FTOS CONFIGUR
- Page 31 and 32:
Table 6 FTOS Command Modes CLI Comm
- Page 33 and 34:
Figure 5 Undoing a command with the
- Page 35 and 36:
Table 7 Short-Cut Keys and their Ac
- Page 37 and 38:
If either of these messages appears
- Page 39 and 40:
Chapter 2 Getting Started When you
- Page 41 and 42:
Configuring a Host Name The host na
- Page 43 and 44:
To configure a username and passwor
- Page 45 and 46:
Important Points to Remember • Yo
- Page 47 and 48:
Viewing Files File information and
- Page 49 and 50:
To change the default storage locat
- Page 51 and 52:
1. Select a cache boot-image. See p
- Page 53 and 54:
View your cache boot configuration
- Page 55 and 56:
Chapter 3 Management This chapter e
- Page 57 and 58:
specify logging to a Syslog server
- Page 59 and 60:
In the lines above, local7 is the l
- Page 61 and 62:
configure a UNIX logging facility l
- Page 63 and 64:
To have FTOS include a timestamp wi
- Page 65 and 66:
configure the system to send SNMP n
- Page 67 and 68:
set SNMP information To set the con
- Page 69 and 70:
Table 10 MIB Objects for Copying Co
- Page 71 and 72:
Table 11 Copying Configuration File
- Page 73 and 74:
Figure 33 shows the command syntax
- Page 75 and 76:
To view the configured NTP time ser
- Page 77 and 78:
To view whether NTP is configured o
- Page 79 and 80:
configure FTP client parameters To
- Page 81 and 82:
To configure and assign an IP ACL t
- Page 83 and 84:
Figure 40 shows the steps used to c
- Page 85 and 86:
Figure 41 • Set a manual lock usi
- Page 87 and 88:
Chapter 4 Configuration Replace and
- Page 89 and 90:
Archiving a Configuration File Figu
- Page 91 and 92:
Figure 45 Force10#configure replace
- Page 93 and 94:
Configuring Auto-archive Figure 49
- Page 95 and 96:
Figure 51 Viewing the Difference be
- Page 97 and 98:
Chapter 5 RMON This describes the R
- Page 99 and 100:
setting rmon alarm To set an alarm
- Page 101 and 102:
The following example shows the rmo
- Page 103 and 104:
Chapter 6 Security Security in FTOS
- Page 105 and 106:
monitor accounting FTOS does not su
- Page 107 and 108:
AAA Authentication Login To configu
- Page 109 and 110:
To use local authentication for ena
- Page 111 and 112:
To configure a user name and passwo
- Page 113 and 114:
Step Command Syntax Command Mode Pu
- Page 115 and 116:
To view the password configured for
- Page 117 and 118:
Privilege Level Through the RADIUS
- Page 119 and 120:
If you want to change an optional p
- Page 121 and 122:
To select TACACS as the login authe
- Page 123 and 124:
TACACS+ Remote Authentication and A
- Page 125 and 126:
FTOS can assign different access cl
- Page 127 and 128:
To enable the SSH server for versio
- Page 129 and 130:
SSH with IPv6 FTOS supports both in
- Page 131 and 132:
Step Task 4 Attempt an inbound Teln
- Page 133 and 134:
Host-based Authentication Authentic
- Page 135 and 136:
Trace List You can log packet activ
- Page 137 and 138:
Step Command Syntax Command Mode Pu
- Page 139 and 140:
Command Syntax Command Mode Purpose
- Page 141 and 142:
Protection Against TCP Tiny and Ove
- Page 143 and 144:
Chapter 7 Layer 2 This chapter desc
- Page 145 and 146:
Port-Based VLANs Port-based VLANs a
- Page 147 and 148:
A VLAN is active only if the VLAN c
- Page 149 and 150:
Step Command Syntax Command Mode Pu
- Page 151 and 152:
MAC Addressing and MAC Access Lists
- Page 153 and 154:
Configuration Task List for MAC ACL
- Page 155 and 156: To view a specific configured MAC A
- Page 157 and 158: Figure 83 illustrates how the seq c
- Page 159 and 160: To view which MAC ACL is applied to
- Page 161 and 162: • Verify MAC learning-limit setti
- Page 163 and 164: This example shows four ways to spe
- Page 165 and 166: Recovering from MAC address learnin
- Page 167 and 168: When NIC teaming is employed, consi
- Page 169 and 170: As shown in Figure 98, the server M
- Page 171 and 172: Chapter 8 GVRP Protocol Overview Ty
- Page 173 and 174: Enable GVRP on a Layer 2 Interface
- Page 175 and 176: Chapter 9 Interfaces This chapter d
- Page 177 and 178: When an interface is in either mode
- Page 179 and 180: To enter the INTERFACE mode, use th
- Page 181 and 182: To clear the counters, use the foll
- Page 183 and 184: • Once the virtual IP address is
- Page 185 and 186: Dynamic—Port channels that are dy
- Page 187 and 188: To distribute IP traffic over a por
- Page 189 and 190: • shutdown/no shutdown • mtu (i
- Page 191 and 192: change the criteria used to distrib
- Page 193 and 194: configure the minimum oper up links
- Page 195 and 196: A consideration for including VLANs
- Page 197 and 198: duplicate entries Duplicate single
- Page 199 and 200: Step Command Syntax Command Mode Us
- Page 201 and 202: Force10#show interfaces tengigabite
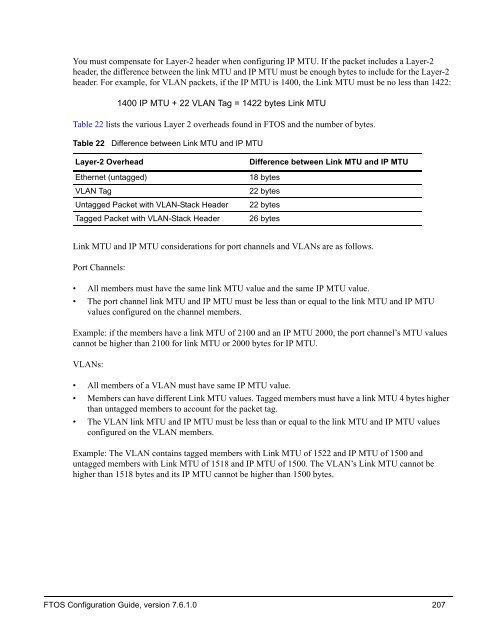
- Page 203 and 204: Though the rate is configurable wit
- Page 205: • improves network stability by p
- Page 209 and 210: Chapter 10 LACP The Link Aggregatio
- Page 211 and 212: LACP Configuration FTOS enables the
- Page 213 and 214: creating a LAG To create a LAG, def
- Page 215 and 216: Debugging LACP Command Syntax Comma
- Page 217 and 218: View the status of a failover group
- Page 219 and 220: Chapter 11 VLAN Stacking This chapt
- Page 221 and 222: Configuration Task List for VLAN-St
- Page 223 and 224: Use the show vlan command in the EX
- Page 225 and 226: E1200-1 Configuration E1200-1#sh ru
- Page 227 and 228: vlan-stack compatible member Gigabi
- Page 229 and 230: Chapter 12 IP Addressing Force10 sy
- Page 231 and 232: Step Command Syntax Command Mode Pu
- Page 233 and 234: • When interface goes down, FTOS
- Page 235 and 236: • enable dynamic resolution of ho
- Page 237 and 238: ARP Force10#traceroute www.force10n
- Page 239 and 240: Command Syntax Command Mode Purpose
- Page 241 and 242: 2. Configure a broadcast address on
- Page 243 and 244: UDP Helper with Broadcast-all Addre
- Page 245 and 246: Packet 2 is sent from a host on VLA
- Page 247 and 248: Chapter 13 IP Access Control Lists,
- Page 249 and 250: • configure a standard IP ACL on
- Page 251 and 252: To view all configured IP ACLs, use
- Page 253 and 254: Figure 171 illustrates how the seq
- Page 255 and 256: Note: If an interface is configured
- Page 257 and 258:
To create an ingress ACLs, use the
- Page 259 and 260:
Configuring ACLs to Loopback E-Seri
- Page 261 and 262:
• A prefix list without any permi
- Page 263 and 264:
Figure 178 illustrates a prefix lis
- Page 265 and 266:
To view the configuration, use the
- Page 267 and 268:
Figure 183 shows the resequencing o
- Page 269 and 270:
Figure 184 Resequencing Remarks For
- Page 271 and 272:
To view the configuration, use the
- Page 273 and 274:
Also, if there are different instan
- Page 275 and 276:
configure a route map for route red
- Page 277 and 278:
Chapter 14 Quality of Service Force
- Page 279 and 280:
Aggregated Shaping Aggregated shapi
- Page 281 and 282:
Force10#config t Force10(conf)#inte
- Page 283 and 284:
Command Syntax Command Mode Usage r
- Page 285 and 286:
Command Syntax Command Mode Usage s
- Page 287 and 288:
• In case a QoS service policy th
- Page 289 and 290:
create a class-map To create Layer
- Page 291 and 292:
match ip precedence You can also us
- Page 293 and 294:
To configure a class-map to use a L
- Page 295 and 296:
Figure 207 shows how to define a Qo
- Page 297 and 298:
To remove an existing output QoS po
- Page 299 and 300:
To delete the command, use the no r
- Page 301 and 302:
To remove a previously set IP DSCP
- Page 303 and 304:
Show Commands To view input QoS pol
- Page 305 and 306:
Specify trust DSCP To define a dyna
- Page 307 and 308:
apply input policy maps to interfac
- Page 309 and 310:
To remove the output policy map fro
- Page 311 and 312:
Table 30 Pre-defined WRED Profile T
- Page 313 and 314:
To view the QoS statistics for WRED
- Page 315 and 316:
Figure 234 Packet Drop Rate for WRE
- Page 317 and 318:
• When multicast bandwidth is ass
- Page 319 and 320:
Test the policy-map size against th
- Page 321 and 322:
Chapter 15 VRRP Virtual Router Redu
- Page 323 and 324:
VRRP Benefits With VRRP configured
- Page 325 and 326:
To create a virtual router, use the
- Page 327 and 328:
Figure 240 shows the same VRRP grou
- Page 329 and 330:
To view the password, use the show
- Page 331 and 332:
To track an interface, use the foll
- Page 333 and 334:
Chapter 16 Spanning Tree Protocol P
- Page 335 and 336:
R1(conf)# int range gi 1/1 - 4 R1(c
- Page 337 and 338:
oot R1 R2 1/1 1/2 3/1 3/2 R3 1/3 1/
- Page 339 and 340:
To change these parameters: Task Co
- Page 341 and 342:
Preventing Network Disruptions with
- Page 343 and 344:
SNMP Traps for Root Elections and T
- Page 345 and 346:
Chapter 17 PVST+ PVST+ (Per-VLAN Sp
- Page 347 and 348:
Configuring Bridge Priority In STP,
- Page 349 and 350:
To change the max-age value in seco
- Page 351 and 352:
To change the port priority of an i
- Page 353 and 354:
Figure 265, shows the brief output
- Page 355 and 356:
Chapter 18 RSTP Rapid Spanning Tree
- Page 357 and 358:
To configure the interfaces for Lay
- Page 359 and 360:
R1#show spanning-tree rstp Root Ide
- Page 361 and 362:
To change these parameters, use the
- Page 363 and 364:
Task Command Syntax Command Mode As
- Page 365 and 366:
Chapter 19 MSTP IEEE 802.1s MSTP (M
- Page 367 and 368:
To allow for a larger number of por
- Page 369 and 370:
Force10#show spanning-tree msti 1 M
- Page 371 and 372:
The parameters forward-delay, hello
- Page 373 and 374:
Table 39 Multiple Spanning Tree Por
- Page 375 and 376:
Chapter 20 OSPF Open Shortest Path
- Page 377 and 378:
To confirm that this behavior is im
- Page 379 and 380:
FTOS supports one OSPF routing proc
- Page 381 and 382:
OSPF, by default, sends hello packe
- Page 383 and 384:
To suppress the interface’s parti
- Page 385 and 386:
Command Syntax Command Mode Usage i
- Page 387 and 388:
Command Syntax Command Mode Usage g
- Page 389 and 390:
edistribute routes You can add rout
- Page 391 and 392:
Chapter 21 802.1x Protocol Overview
- Page 393 and 394:
4. The authentication server replie
- Page 395 and 396:
To enable 802.1x: Step Task Command
- Page 397 and 398:
To configure the quiet period after
- Page 399 and 400:
Re-authenticating a Port Periodic R
- Page 401 and 402:
Figure 302 shows configuration info
- Page 403 and 404:
Guest and Authentication-fail VLANs
- Page 405 and 406:
Figure 305 Configuring an Authentic
- Page 407 and 408:
Chapter 22 Upgrade Procedures This
- Page 409 and 410:
Step Task Command Command Mode 3 Up
- Page 411 and 412:
Figure 308 Viewing the Boot Code Ve
- Page 413 and 414:
Figure 311 Determining if the Runni
- Page 415 and 416:
Upgrading All FPGAs You have the op
- Page 417 and 418:
Perform an upgrade only when the sy
- Page 419 and 420:
Figure 316 Upgrading E-Series SFM F
- Page 421 and 422:
Appendix A SNMP Traps SNMP SNMP is
- Page 423 and 424:
Table 40 SNMP Traps and OIDs OID St
- Page 425 and 426:
Figure 318 SNMP Traps and Error Mes
- Page 427 and 428:
Figure 318 SNMP Traps and Error Mes
- Page 429 and 430:
Figure 318 SNMP Traps and Error Mes
- Page 431 and 432:
Appendix B RFCs and MIBs This appen
- Page 433 and 434:
• RFC 2575—View-based Access Co
- Page 435 and 436:
• Definitions of Managed Objects
- Page 437 and 438:
If you have forgotten or lost your
- Page 439 and 440:
Appendix C Managing VLANs using SNM
- Page 441 and 442:
Query q-bride MIB object, dot1qVlan
- Page 443 and 444:
To assign ports 1-23 (line card 0)
- Page 445 and 446:
Changing Administrative Status with
- Page 447 and 448:
Numerics 10/100/1000 Base-T Etherne
- Page 449 and 450:
channel 188 configuring secondary I
- Page 451 and 452:
default 73, 76 definition 73 enabli
- Page 453 and 454:
RFC 2519 432 RFC 2558 434, 435 RFC
- Page 455 and 456:
Customer traffic 219 definition 219