NIST 800-44 Version 2 Guidelines on Securing Public Web Servers
NIST 800-44 Version 2 Guidelines on Securing Public Web Servers
NIST 800-44 Version 2 Guidelines on Securing Public Web Servers
Create successful ePaper yourself
Turn your PDF publications into a flip-book with our unique Google optimized e-Paper software.
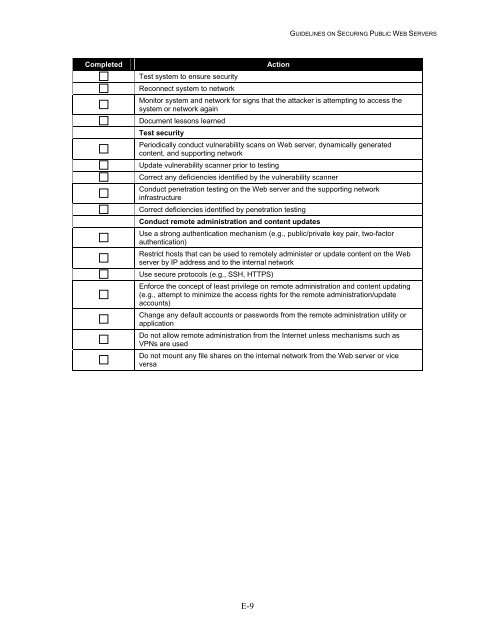
GUIDELINES ON SECURING PUBLIC WEB SERVERS<br />
Completed<br />
Test system to ensure security<br />
Rec<strong>on</strong>nect system to network<br />
Acti<strong>on</strong><br />
M<strong>on</strong>itor system and network for signs that the attacker is attempting to access the<br />
system or network again<br />
Document less<strong>on</strong>s learned<br />
Test security<br />
Periodically c<strong>on</strong>duct vulnerability scans <strong>on</strong> <strong>Web</strong> server, dynamically generated<br />
c<strong>on</strong>tent, and supporting network<br />
Update vulnerability scanner prior to testing<br />
Correct any deficiencies identified by the vulnerability scanner<br />
C<strong>on</strong>duct penetrati<strong>on</strong> testing <strong>on</strong> the <strong>Web</strong> server and the supporting network<br />
infrastructure<br />
Correct deficiencies identified by penetrati<strong>on</strong> testing<br />
C<strong>on</strong>duct remote administrati<strong>on</strong> and c<strong>on</strong>tent updates<br />
Use a str<strong>on</strong>g authenticati<strong>on</strong> mechanism (e.g., public/private key pair, two-factor<br />
authenticati<strong>on</strong>)<br />
Restrict hosts that can be used to remotely administer or update c<strong>on</strong>tent <strong>on</strong> the <strong>Web</strong><br />
server by IP address and to the internal network<br />
Use secure protocols (e.g., SSH, HTTPS)<br />
Enforce the c<strong>on</strong>cept of least privilege <strong>on</strong> remote administrati<strong>on</strong> and c<strong>on</strong>tent updating<br />
(e.g., attempt to minimize the access rights for the remote administrati<strong>on</strong>/update<br />
accounts)<br />
Change any default accounts or passwords from the remote administrati<strong>on</strong> utility or<br />
applicati<strong>on</strong><br />
Do not allow remote administrati<strong>on</strong> from the Internet unless mechanisms such as<br />
VPNs are used<br />
Do not mount any file shares <strong>on</strong> the internal network from the <strong>Web</strong> server or vice<br />
versa<br />
E-9