NIST 800-44 Version 2 Guidelines on Securing Public Web Servers
NIST 800-44 Version 2 Guidelines on Securing Public Web Servers
NIST 800-44 Version 2 Guidelines on Securing Public Web Servers
You also want an ePaper? Increase the reach of your titles
YUMPU automatically turns print PDFs into web optimized ePapers that Google loves.
GUIDELINES ON SECURING PUBLIC WEB SERVERS<br />
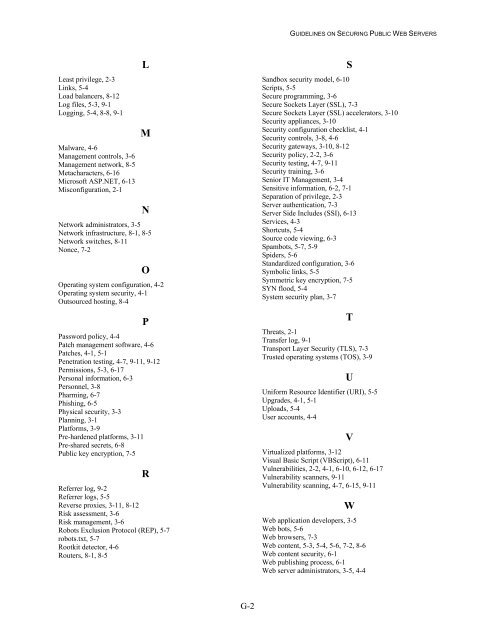
Least privilege, 2-3<br />
Links, 5-4<br />
Load balancers, 8-12<br />
Log files, 5-3, 9-1<br />
Logging, 5-4, 8-8, 9-1<br />
Malware, 4-6<br />
Management c<strong>on</strong>trols, 3-6<br />
Management network, 8-5<br />
Metacharacters, 6-16<br />
Microsoft ASP.NET, 6-13<br />
Misc<strong>on</strong>figurati<strong>on</strong>, 2-1<br />
L<br />
M<br />
N<br />
Network administrators, 3-5<br />
Network infrastructure, 8-1, 8-5<br />
Network switches, 8-11<br />
N<strong>on</strong>ce, 7-2<br />
O<br />
Operating system c<strong>on</strong>figurati<strong>on</strong>, 4-2<br />
Operating system security, 4-1<br />
Outsourced hosting, 8-4<br />
P<br />
Password policy, 4-4<br />
Patch management software, 4-6<br />
Patches, 4-1, 5-1<br />
Penetrati<strong>on</strong> testing, 4-7, 9-11, 9-12<br />
Permissi<strong>on</strong>s, 5-3, 6-17<br />
Pers<strong>on</strong>al informati<strong>on</strong>, 6-3<br />
Pers<strong>on</strong>nel, 3-8<br />
Pharming, 6-7<br />
Phishing, 6-5<br />
Physical security, 3-3<br />
Planning, 3-1<br />
Platforms, 3-9<br />
Pre-hardened platforms, 3-11<br />
Pre-shared secrets, 6-8<br />
<strong>Public</strong> key encrypti<strong>on</strong>, 7-5<br />
R<br />
Referrer log, 9-2<br />
Referrer logs, 5-5<br />
Reverse proxies, 3-11, 8-12<br />
Risk assessment, 3-6<br />
Risk management, 3-6<br />
Robots Exclusi<strong>on</strong> Protocol (REP), 5-7<br />
robots.txt, 5-7<br />
Rootkit detector, 4-6<br />
Routers, 8-1, 8-5<br />
Sandbox security model, 6-10<br />
Scripts, 5-5<br />
Secure programming, 3-6<br />
Secure Sockets Layer (SSL), 7-3<br />
Secure Sockets Layer (SSL) accelerators, 3-10<br />
Security appliances, 3-10<br />
Security c<strong>on</strong>figurati<strong>on</strong> checklist, 4-1<br />
Security c<strong>on</strong>trols, 3-8, 4-6<br />
Security gateways, 3-10, 8-12<br />
Security policy, 2-2, 3-6<br />
Security testing, 4-7, 9-11<br />
Security training, 3-6<br />
Senior IT Management, 3-4<br />
Sensitive informati<strong>on</strong>, 6-2, 7-1<br />
Separati<strong>on</strong> of privilege, 2-3<br />
Server authenticati<strong>on</strong>, 7-3<br />
Server Side Includes (SSI), 6-13<br />
Services, 4-3<br />
Shortcuts, 5-4<br />
Source code viewing, 6-3<br />
Spambots, 5-7, 5-9<br />
Spiders, 5-6<br />
Standardized c<strong>on</strong>figurati<strong>on</strong>, 3-6<br />
Symbolic links, 5-5<br />
Symmetric key encrypti<strong>on</strong>, 7-5<br />
SYN flood, 5-4<br />
System security plan, 3-7<br />
S<br />
T<br />
Threats, 2-1<br />
Transfer log, 9-1<br />
Transport Layer Security (TLS), 7-3<br />
Trusted operating systems (TOS), 3-9<br />
U<br />
Uniform Resource Identifier (URI), 5-5<br />
Upgrades, 4-1, 5-1<br />
Uploads, 5-4<br />
User accounts, 4-4<br />
V<br />
Virtualized platforms, 3-12<br />
Visual Basic Script (VBScript), 6-11<br />
Vulnerabilities, 2-2, 4-1, 6-10, 6-12, 6-17<br />
Vulnerability scanners, 9-11<br />
Vulnerability scanning, 4-7, 6-15, 9-11<br />
W<br />
<strong>Web</strong> applicati<strong>on</strong> developers, 3-5<br />
<strong>Web</strong> bots, 5-6<br />
<strong>Web</strong> browsers, 7-3<br />
<strong>Web</strong> c<strong>on</strong>tent, 5-3, 5-4, 5-6, 7-2, 8-6<br />
<strong>Web</strong> c<strong>on</strong>tent security, 6-1<br />
<strong>Web</strong> publishing process, 6-1<br />
<strong>Web</strong> server administrators, 3-5, 4-4<br />
G-2