NIST 800-44 Version 2 Guidelines on Securing Public Web Servers
NIST 800-44 Version 2 Guidelines on Securing Public Web Servers
NIST 800-44 Version 2 Guidelines on Securing Public Web Servers
Create successful ePaper yourself
Turn your PDF publications into a flip-book with our unique Google optimized e-Paper software.
GUIDELINES ON SECURING PUBLIC WEB SERVERS<br />
trick the user through social engineering into clicking <strong>on</strong> the maliciously crafted URL. If the user’s<br />
<strong>Web</strong> browser was vulnerable to the exploit, the user’s machine could be compromised. Since this<br />
attack does require some level social engineering, it is c<strong>on</strong>sidered somewhat less dangerous than<br />
attacks <strong>on</strong> persistent vulnerabilities.<br />
The soluti<strong>on</strong> to XSS attacks is to validate all user input and remove any unexpected or potentially risky<br />
data. Another soluti<strong>on</strong> is to use an HTML-quoted versi<strong>on</strong> 45 of any user input that is presented back to<br />
other users. This will prevent the <strong>Web</strong> browsers of other users from interpreting that input and acting <strong>on</strong><br />
any embedded commands present.<br />
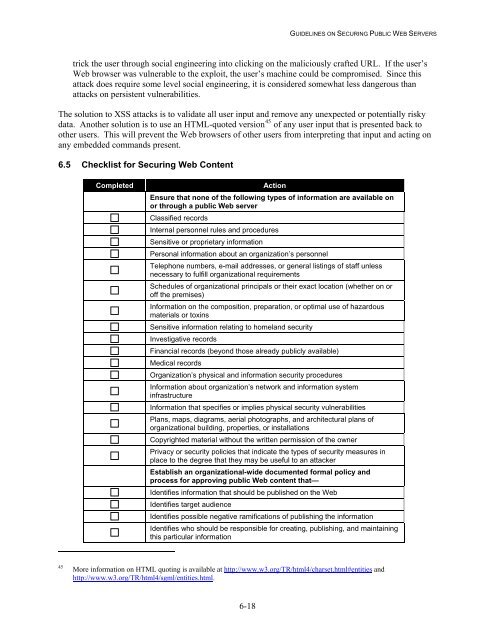
6.5 Checklist for <strong>Securing</strong> <strong>Web</strong> C<strong>on</strong>tent<br />
Completed<br />
Acti<strong>on</strong><br />
Ensure that n<strong>on</strong>e of the following types of informati<strong>on</strong> are available <strong>on</strong><br />
or through a public <strong>Web</strong> server<br />
Classified records<br />
Internal pers<strong>on</strong>nel rules and procedures<br />
Sensitive or proprietary informati<strong>on</strong><br />
Pers<strong>on</strong>al informati<strong>on</strong> about an organizati<strong>on</strong>’s pers<strong>on</strong>nel<br />
Teleph<strong>on</strong>e numbers, e-mail addresses, or general listings of staff unless<br />
necessary to fulfill organizati<strong>on</strong>al requirements<br />
Schedules of organizati<strong>on</strong>al principals or their exact locati<strong>on</strong> (whether <strong>on</strong> or<br />
off the premises)<br />
Informati<strong>on</strong> <strong>on</strong> the compositi<strong>on</strong>, preparati<strong>on</strong>, or optimal use of hazardous<br />
materials or toxins<br />
Sensitive informati<strong>on</strong> relating to homeland security<br />
Investigative records<br />
Financial records (bey<strong>on</strong>d those already publicly available)<br />
Medical records<br />
Organizati<strong>on</strong>’s physical and informati<strong>on</strong> security procedures<br />
Informati<strong>on</strong> about organizati<strong>on</strong>’s network and informati<strong>on</strong> system<br />
infrastructure<br />
Informati<strong>on</strong> that specifies or implies physical security vulnerabilities<br />
Plans, maps, diagrams, aerial photographs, and architectural plans of<br />
organizati<strong>on</strong>al building, properties, or installati<strong>on</strong>s<br />
Copyrighted material without the written permissi<strong>on</strong> of the owner<br />
Privacy or security policies that indicate the types of security measures in<br />
place to the degree that they may be useful to an attacker<br />
Establish an organizati<strong>on</strong>al-wide documented formal policy and<br />
process for approving public <strong>Web</strong> c<strong>on</strong>tent that—<br />
Identifies informati<strong>on</strong> that should be published <strong>on</strong> the <strong>Web</strong><br />
Identifies target audience<br />
Identifies possible negative ramificati<strong>on</strong>s of publishing the informati<strong>on</strong><br />
Identifies who should be resp<strong>on</strong>sible for creating, publishing, and maintaining<br />
this particular informati<strong>on</strong><br />
45<br />
More informati<strong>on</strong> <strong>on</strong> HTML quoting is available at http://www.w3.org/TR/html4/charset.html#entities and<br />
http://www.w3.org/TR/html4/sgml/entities.html.<br />
6-18