NIST 800-44 Version 2 Guidelines on Securing Public Web Servers
NIST 800-44 Version 2 Guidelines on Securing Public Web Servers
NIST 800-44 Version 2 Guidelines on Securing Public Web Servers
Create successful ePaper yourself
Turn your PDF publications into a flip-book with our unique Google optimized e-Paper software.
GUIDELINES ON SECURING PUBLIC WEB SERVERS<br />
Password protecti<strong>on</strong> is the <strong>on</strong>ly reliable way to exclude n<strong>on</strong>compliant bots or curious users. See Secti<strong>on</strong><br />
7 for more informati<strong>on</strong> <strong>on</strong> <strong>Web</strong>-based authenticati<strong>on</strong> methods.<br />
Often, spambots ignore robots.txt and search for email addresses <strong>on</strong> the <strong>Web</strong> site and/or forms to which<br />
they can submit spam-related c<strong>on</strong>tent. Spambots that merely scan the <strong>Web</strong> site typically do not affect its<br />
availability. Nevertheless, it may be beneficial to prevent them from harvesting e-mail addresses by<br />
performing address munging [Unsp06]—displaying e-mail addresses in an alternative human-readable<br />
format, such as listing name@mywww.gov as . Unfortunately, these<br />
techniques do not stop all spambots. The best defense against address harvesting is not to display e-mail<br />
addresses.<br />
Spambots searching for <strong>Web</strong> forms to submit spam-related c<strong>on</strong>tent are a direct threat to the <strong>Web</strong> site.<br />
They can affect the organizati<strong>on</strong>’s image if visitors view the submitted c<strong>on</strong>tent as an endorsement. They<br />
may also affect the <strong>Web</strong> site’s availability by making it difficult for users to find necessary c<strong>on</strong>tent.<br />
There are several techniques available to reduce the amount of spam submissi<strong>on</strong>s, including—<br />
Blocking form submissi<strong>on</strong>s that use spam-related keywords<br />
Using the rel=“nofollow” keyword in all submitted links, which will cause search engines to omit the<br />
links in their page-ranking algorithms, directly affecting the goals of a spambot [Google05]<br />
Requiring submitters to solve a Completely Automated <strong>Public</strong> Turing Test to Tell Computers and<br />
Humans Apart (CAPTCHA) prior to being allowed to submit c<strong>on</strong>tent.<br />
These techniques all have benefits and drawbacks associated with them. For example, some CAPTCHA<br />
techniques, which can be implemented as an obscured word in an image, do not comply with American<br />
Disability Associati<strong>on</strong> (ADA) or Secti<strong>on</strong> 508 accessibility guidelines. Informati<strong>on</strong> about <strong>on</strong>going<br />
research <strong>on</strong> detecting spambots can be found through the Adversarial Informati<strong>on</strong> Retrieval <strong>on</strong> the <strong>Web</strong><br />
(AIR<strong>Web</strong>) workshops. 29<br />
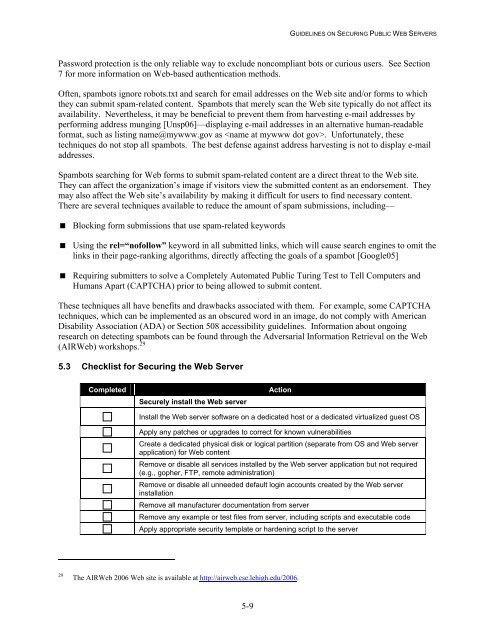
5.3 Checklist for <strong>Securing</strong> the <strong>Web</strong> Server<br />
Completed<br />
Securely install the <strong>Web</strong> server<br />
Acti<strong>on</strong><br />
Install the <strong>Web</strong> server software <strong>on</strong> a dedicated host or a dedicated virtualized guest OS<br />
Apply any patches or upgrades to correct for known vulnerabilities<br />
Create a dedicated physical disk or logical partiti<strong>on</strong> (separate from OS and <strong>Web</strong> server<br />
applicati<strong>on</strong>) for <strong>Web</strong> c<strong>on</strong>tent<br />
Remove or disable all services installed by the <strong>Web</strong> server applicati<strong>on</strong> but not required<br />
(e.g., gopher, FTP, remote administrati<strong>on</strong>)<br />
Remove or disable all unneeded default login accounts created by the <strong>Web</strong> server<br />
installati<strong>on</strong><br />
Remove all manufacturer documentati<strong>on</strong> from server<br />
Remove any example or test files from server, including scripts and executable code<br />
Apply appropriate security template or hardening script to the server<br />
29<br />
The AIR<strong>Web</strong> 2006 <strong>Web</strong> site is available at http://airweb.cse.lehigh.edu/2006.<br />
5-9