NIST 800-44 Version 2 Guidelines on Securing Public Web Servers
NIST 800-44 Version 2 Guidelines on Securing Public Web Servers
NIST 800-44 Version 2 Guidelines on Securing Public Web Servers
Create successful ePaper yourself
Turn your PDF publications into a flip-book with our unique Google optimized e-Paper software.
GUIDELINES ON SECURING PUBLIC WEB SERVERS<br />
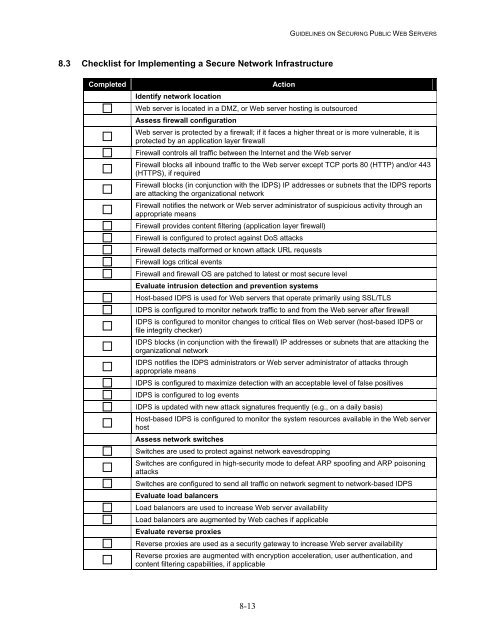
8.3 Checklist for Implementing a Secure Network Infrastructure<br />
Completed<br />
Identify network locati<strong>on</strong><br />
Acti<strong>on</strong><br />
<strong>Web</strong> server is located in a DMZ, or <strong>Web</strong> server hosting is outsourced<br />
Assess firewall c<strong>on</strong>figurati<strong>on</strong><br />
<strong>Web</strong> server is protected by a firewall; if it faces a higher threat or is more vulnerable, it is<br />
protected by an applicati<strong>on</strong> layer firewall<br />
Firewall c<strong>on</strong>trols all traffic between the Internet and the <strong>Web</strong> server<br />
Firewall blocks all inbound traffic to the <strong>Web</strong> server except TCP ports 80 (HTTP) and/or <str<strong>on</strong>g>44</str<strong>on</strong>g>3<br />
(HTTPS), if required<br />
Firewall blocks (in c<strong>on</strong>juncti<strong>on</strong> with the IDPS) IP addresses or subnets that the IDPS reports<br />
are attacking the organizati<strong>on</strong>al network<br />
Firewall notifies the network or <strong>Web</strong> server administrator of suspicious activity through an<br />
appropriate means<br />
Firewall provides c<strong>on</strong>tent filtering (applicati<strong>on</strong> layer firewall)<br />
Firewall is c<strong>on</strong>figured to protect against DoS attacks<br />
Firewall detects malformed or known attack URL requests<br />
Firewall logs critical events<br />
Firewall and firewall OS are patched to latest or most secure level<br />
Evaluate intrusi<strong>on</strong> detecti<strong>on</strong> and preventi<strong>on</strong> systems<br />
Host-based IDPS is used for <strong>Web</strong> servers that operate primarily using SSL/TLS<br />
IDPS is c<strong>on</strong>figured to m<strong>on</strong>itor network traffic to and from the <strong>Web</strong> server after firewall<br />
IDPS is c<strong>on</strong>figured to m<strong>on</strong>itor changes to critical files <strong>on</strong> <strong>Web</strong> server (host-based IDPS or<br />
file integrity checker)<br />
IDPS blocks (in c<strong>on</strong>juncti<strong>on</strong> with the firewall) IP addresses or subnets that are attacking the<br />
organizati<strong>on</strong>al network<br />
IDPS notifies the IDPS administrators or <strong>Web</strong> server administrator of attacks through<br />
appropriate means<br />
IDPS is c<strong>on</strong>figured to maximize detecti<strong>on</strong> with an acceptable level of false positives<br />
IDPS is c<strong>on</strong>figured to log events<br />
IDPS is updated with new attack signatures frequently (e.g., <strong>on</strong> a daily basis)<br />
Host-based IDPS is c<strong>on</strong>figured to m<strong>on</strong>itor the system resources available in the <strong>Web</strong> server<br />
host<br />
Assess network switches<br />
Switches are used to protect against network eavesdropping<br />
Switches are c<strong>on</strong>figured in high-security mode to defeat ARP spoofing and ARP pois<strong>on</strong>ing<br />
attacks<br />
Switches are c<strong>on</strong>figured to send all traffic <strong>on</strong> network segment to network-based IDPS<br />
Evaluate load balancers<br />
Load balancers are used to increase <strong>Web</strong> server availability<br />
Load balancers are augmented by <strong>Web</strong> caches if applicable<br />
Evaluate reverse proxies<br />
Reverse proxies are used as a security gateway to increase <strong>Web</strong> server availability<br />
Reverse proxies are augmented with encrypti<strong>on</strong> accelerati<strong>on</strong>, user authenticati<strong>on</strong>, and<br />
c<strong>on</strong>tent filtering capabilities, if applicable<br />
8-13