NIST 800-44 Version 2 Guidelines on Securing Public Web Servers
NIST 800-44 Version 2 Guidelines on Securing Public Web Servers
NIST 800-44 Version 2 Guidelines on Securing Public Web Servers
Create successful ePaper yourself
Turn your PDF publications into a flip-book with our unique Google optimized e-Paper software.
GUIDELINES ON SECURING PUBLIC WEB SERVERS<br />
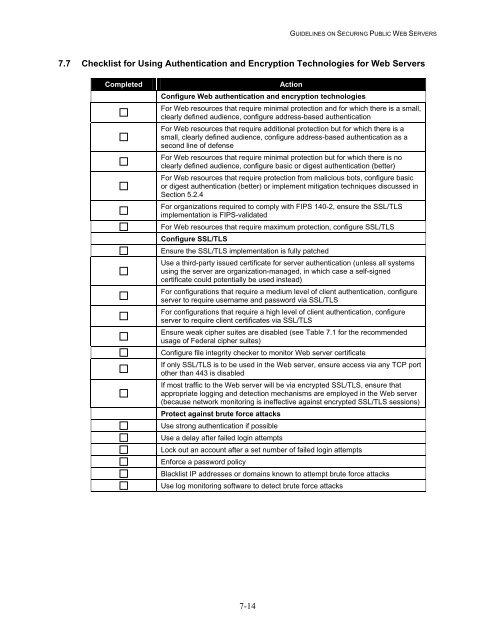
7.7 Checklist for Using Authenticati<strong>on</strong> and Encrypti<strong>on</strong> Technologies for <strong>Web</strong> <strong>Servers</strong><br />
Completed<br />
Acti<strong>on</strong><br />
C<strong>on</strong>figure <strong>Web</strong> authenticati<strong>on</strong> and encrypti<strong>on</strong> technologies<br />
For <strong>Web</strong> resources that require minimal protecti<strong>on</strong> and for which there is a small,<br />
clearly defined audience, c<strong>on</strong>figure address-based authenticati<strong>on</strong><br />
For <strong>Web</strong> resources that require additi<strong>on</strong>al protecti<strong>on</strong> but for which there is a<br />
small, clearly defined audience, c<strong>on</strong>figure address-based authenticati<strong>on</strong> as a<br />
sec<strong>on</strong>d line of defense<br />
For <strong>Web</strong> resources that require minimal protecti<strong>on</strong> but for which there is no<br />
clearly defined audience, c<strong>on</strong>figure basic or digest authenticati<strong>on</strong> (better)<br />
For <strong>Web</strong> resources that require protecti<strong>on</strong> from malicious bots, c<strong>on</strong>figure basic<br />
or digest authenticati<strong>on</strong> (better) or implement mitigati<strong>on</strong> techniques discussed in<br />
Secti<strong>on</strong> 5.2.4<br />
For organizati<strong>on</strong>s required to comply with FIPS 140-2, ensure the SSL/TLS<br />
implementati<strong>on</strong> is FIPS-validated<br />
For <strong>Web</strong> resources that require maximum protecti<strong>on</strong>, c<strong>on</strong>figure SSL/TLS<br />
C<strong>on</strong>figure SSL/TLS<br />
Ensure the SSL/TLS implementati<strong>on</strong> is fully patched<br />
Use a third-party issued certificate for server authenticati<strong>on</strong> (unless all systems<br />
using the server are organizati<strong>on</strong>-managed, in which case a self-signed<br />
certificate could potentially be used instead)<br />
For c<strong>on</strong>figurati<strong>on</strong>s that require a medium level of client authenticati<strong>on</strong>, c<strong>on</strong>figure<br />
server to require username and password via SSL/TLS<br />
For c<strong>on</strong>figurati<strong>on</strong>s that require a high level of client authenticati<strong>on</strong>, c<strong>on</strong>figure<br />
server to require client certificates via SSL/TLS<br />
Ensure weak cipher suites are disabled (see Table 7.1 for the recommended<br />
usage of Federal cipher suites)<br />
C<strong>on</strong>figure file integrity checker to m<strong>on</strong>itor <strong>Web</strong> server certificate<br />
If <strong>on</strong>ly SSL/TLS is to be used in the <strong>Web</strong> server, ensure access via any TCP port<br />
other than <str<strong>on</strong>g>44</str<strong>on</strong>g>3 is disabled<br />
If most traffic to the <strong>Web</strong> server will be via encrypted SSL/TLS, ensure that<br />
appropriate logging and detecti<strong>on</strong> mechanisms are employed in the <strong>Web</strong> server<br />
(because network m<strong>on</strong>itoring is ineffective against encrypted SSL/TLS sessi<strong>on</strong>s)<br />
Protect against brute force attacks<br />
Use str<strong>on</strong>g authenticati<strong>on</strong> if possible<br />
Use a delay after failed login attempts<br />
Lock out an account after a set number of failed login attempts<br />
Enforce a password policy<br />
Blacklist IP addresses or domains known to attempt brute force attacks<br />
Use log m<strong>on</strong>itoring software to detect brute force attacks<br />
7-14