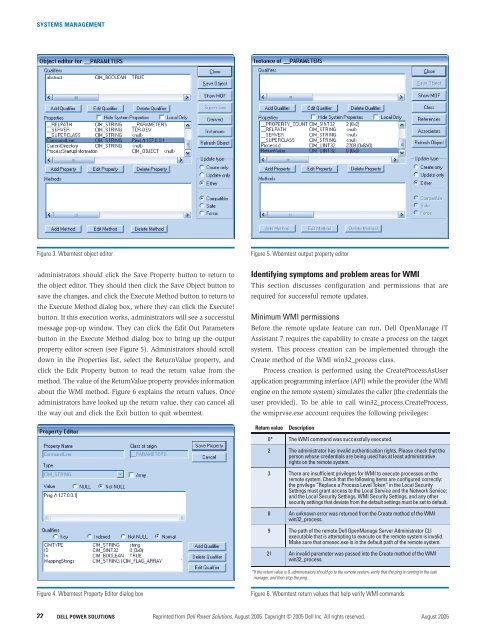
SYSTEMS MANAGEMENTFigure 3. Wbemtest object editorFigure 5. Wbemtest output property editoradministrators should click the Save Property button to return tothe object editor. They should then click the Save Object button tosave the changes, and click the Execute Method button to return tothe Execute Method dialog box, where they can click the Execute!button. If this execution works, administrators will see a successfulmessage pop-up window. They can click the Edit Out Parametersbutton in the Execute Method dialog box to bring up the outputproperty editor screen (see Figure 5). Administrators should scrolldown in the Properties list, select the ReturnValue property, andclick the Edit Property button to read the return value from themethod. The value of the ReturnValue property provides informationabout the WMI method. Figure 6 explains the return values. Onceadministrators have looked up the return value, they can cancel allthe way out and click the Exit button to quit wbemtest.Identifying symptoms and problem areas for WMIThis section discusses configuration and permissions that arerequired for successful remote updates.Minimum WMI permissionsBefore the remote update feature can run, Dell OpenManage ITAssistant 7 requires the capability to create a process on the targetsystem. This process creation can be implemented through theCreate method of the WMI win32_process class.Process creation is performed using the CreateProcessAsUserapplication programming interface (API) while the provider (the WMIengine on the remote system) simulates the caller (the credentials theuser provided). To be able to call win32_process.CreateProcess,the wmiprvse.exe account requires the following privileges:Return valueDescription0* The WMI command was successfully executed.2 The administrator has invalid authentication rights. Please check that theperson whose credentials are being used has at least administrativerights on the remote system.3 There are insufficient privileges for WMI to execute processes on theremote system. Check that the following items are configured correctly:the privilege “Replace a Process Level Token” in the Local SecuritySettings must grant access to the Local Service and the Network Service;and the Local Security Settings, WMI Security Settings, and any othersecurity settings that deviate from the default settings must be set to default.8 An unknown error was returned from the Create method of the WMIwin32_process.9 The path of the remote Dell OpenManage Server Administrator CLIexecutable that is attempting to execute on the remote system is invalid.Make sure that omexec.exe is in the default path of the remote system.21 An invalid parameter was passed into the Create method of the WMIwin32_process.*If the return value is 0, administrators should go to the remote system, verify that the ping is running in the taskmanager, and then stop the ping.Figure 4. Wbemtest Property Editor dialog boxFigure 6. Wbemtest return values that help verify WMI commands22DELL <strong>POWER</strong> <strong>SOLUTIONS</strong> Reprinted from Dell Power Solutions, August 2005. Copyright © 2005 Dell Inc. All rights reserved. August 2005
SYSTEMS MANAGEMENT• SeImpersonatePrivilege: Simulate a client (MicrosoftWindows Server 2003 or Windows XP with Service Pack 2)• SeAssignPrimaryTokenPrivilege: Replace a process-level token• SeIncreaseQuotaPrivilege: Adjust memory quotas for a processTo authorize WMI users and set permissions, administratorsshould access WMI Control. To do so, they must right-click the MyComputer icon on the target system, select “Manage,” and thenselect “Services and Applications” in the Computer Managementtree. Next, they should right-click on “WMI Control” and select“Properties.” From this window, administrators should click theSecurity tab, select the namespace for which they want to assign auser or group access, and then click the Security button.For example, an administrator provides access to Root>CIMV2.In the Security for ROOT\CIMV2 dialog box, the administrator clicksthe Add button; then the Select Users, Computers, or Groups dialogbox appears, where the name of the object (user or group) to beadded is entered. The administrator clicks the Check Names buttonto verify the entry and then clicks the OK button. Administratorsmay have to change the location or use the Advanced button toquery for objects. The dialog box Help feature—which is accessedby right-clicking on any element and selecting “What is this?”—canprovide more details.At the top of this list, the caller account should haveFILE_EXECUTE and FILE_READ_DATA access to the image it isabout to launch. The account should also be able to bypass traversechecking (SeChangeNotifyPrivilege is enabled).In the Security dialog box, under Permissions for Administrators,administrators should select the permissions to allow or denythe new user or group. Permission levels are as follows:DNS name problemsDell OpenManage IT Assistant offers administrators the ability todiscover systems by IP address range or by host name. Once ITAhas determined the host name for a discovered device, however,it will connect to that machine using the host name for remoteupdates. With a network that contains a mixture of domains andworkgroups, more than one system may match the host name thatITA is using to access the target system. In such a case, severaltypes of failures may occur because ITA is communicating with thewrong system. The only way to correct this situation is to identifythe problem system(s) and change the host names to be uniqueacross the network.This duplicate name error also can occur if systems that arepart of a domain are ghosted—that is, the hard drive image for asystem was created from ghost software used to duplicate images ofhard drives. All members of a domain should be uniquely named;otherwise, a system with a duplicate name will fail when attemptingvarious network tasks. In this case, the system must be removedfrom the domain and added again with a unique name.Streamlining remote software updatesThrough WMI, Dell OpenManage IT Assistant 7 can enable efficientdeployment and execution of remote software updates acrossMicrosoft Windows–based systems. In particular, enterprises withcomplex networks, numerous security policies, and a large numberof servers face a high probability of encountering problems whendeploying remote software updates in a WMI environment. Thetroubleshooting guidelines discussed in this article can help administratorsstreamline systems management and the remote softwareupdate process using ITA 7.• Execute Methods: Allows methods exported from the WMIclasses or instances to be run.• Full Write: Allows full read, write, and delete access to allWMI objects, classes, and instances.• Partial Write: Allows write access to static WMI objects.• Provider Write: Allows write access to objects that aresupplied by providers.• Enable Account: Allows read access to WMI objects.• Remote Enable: Allows remote access to the namespace.• Read Security: Allows read-only access to WMI securityinformation.• Edit Security: Allows read and write access to WMI securityinformation.Note: To set WMI permissions, an administrator must be amember of the Administrators group on the local computer.Administrators also can set permissions on a remote computer.To access a remote computer, they should right-click on “ComputerManagement” to connect to the other computer.Bradley Bransom is a senior developer on the Dell Server Administratorteam. Prior to joining Dell, Bradley was employed by AMD, 3COM, andTexas Instruments. He has a B.S. in Computer Science with a minor inMathematics from Texas A&M University.Tobin Rysenga is a senior developer on the Dell OpenManage IT Assistantdevelopment team. Prior to joining Dell, Tobin worked for Maxis, Microprose,and Glass Eye and has worked as an independent consultant.FOR MORE INFORMATIONDell OpenManage IT Assistant User’s Guide:support.dell.com/support/edocs/software/smitasst/7.0Shetty, Sudhir, Steve Heracleous, and Rohit Sharma. “SoftwareChange Management Using Dell OpenManage IT Assistant.”Dell Power Solutions, August 2005. www.dell.com/downloads/global/power/ps3q05-20050106-Sharma.pdfwww.dell.com/powersolutions Reprinted from Dell Power Solutions, August 2005. Copyright © 2005 Dell Inc. All rights reserved. DELL <strong>POWER</strong> <strong>SOLUTIONS</strong> 23