code_of_practice_V3_2019
Create successful ePaper yourself
Turn your PDF publications into a flip-book with our unique Google optimized e-Paper software.
11.6.5 Security measures include:<br />
n Security by design, using best <strong>practice</strong> principles;<br />
n Use <strong>of</strong> safe operating system (or no operating system at all), as many cyber-attacks exploit the operating system<br />
itself;<br />
n Air-gapping (denial <strong>of</strong> communications so that the firmware, once programmed, is safe). This eliminates backdoor<br />
attacks and is effectively applied to many sensors such as GPS, heading and depth sensors;<br />
n Command link encryption;<br />
n Use <strong>of</strong> multiple command links, effectively providing command link backup.<br />
n BIT testing to verify the integrity <strong>of</strong> firmware and mission and configuration data at run time.<br />
11.6.6 A Cyber Security Analysis should be conducted to identify possible security vulnerabilities and their effects on<br />
the vital systems and the performance <strong>of</strong> the craft or vessel, including but not limited to the command link, the<br />
generation and dissemination <strong>of</strong> waypoints, steering, and the ability to initiate Emergency Stop.<br />
11.6.7 The Cyber Security Analysis should be interpreted and acted upon in a manner similar to the Risk Assessment,<br />
in terms <strong>of</strong> identifying the need to apply corrective measures to reduce risk to an acceptably low level.<br />
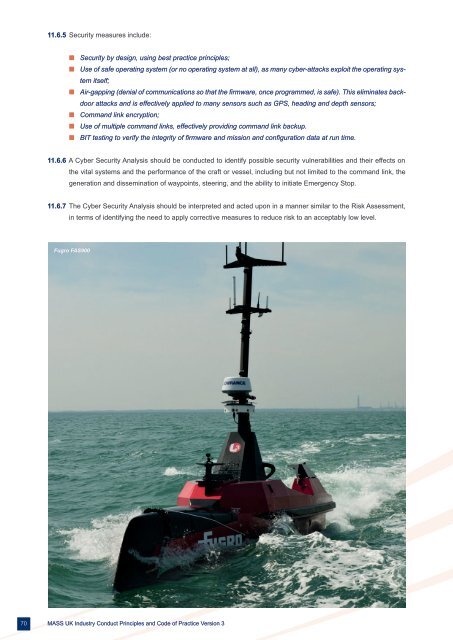
Fugro FAS900<br />
70<br />
MASS UK Industry Conduct Principles and Code <strong>of</strong> Practice Version 3