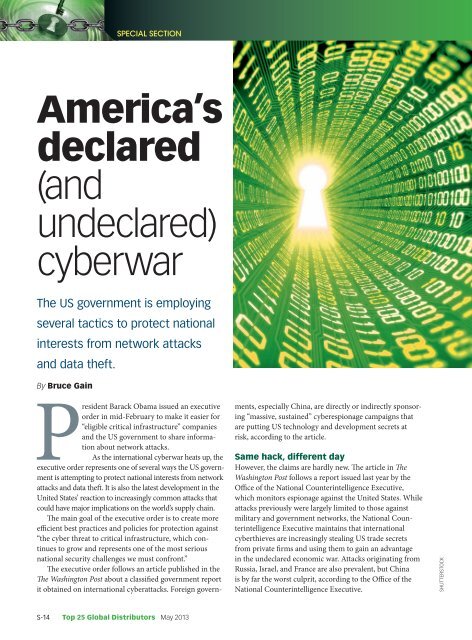
Special SectionAmerica’sdeclared(andundeclared)cyberwarThe US government is employingseveral tactics to protect nationalinterests from network attacksand data theft.By Bruce GainPresident Barack Obama issued an executiveorder in mid-February to make it easier for“eligible critical infrastructure” companiesand the US government to share informationabout network attacks.As the international cyberwar heats up, theexecutive order represents one of several ways the US governmentis attempting to protect national interests from networkattacks and data theft. It is also the latest development in theUnited States’ reaction to increasingly common attacks thatcould have major implications on the world’s supply chain.The main goal of the executive order is to create moreefficient best practices and policies for protection against“the cyber threat to critical infrastructure, which continuesto grow and represents one of the most seriousnational security challenges we must confront.”The executive order follows an article published in theThe Washington Post about a classified government reportit obtained on international cyberattacks. Foreign governments,especially China, are directly or indirectly sponsoring“massive, sustained” cyberespionage campaigns thatare putting US technology and development secrets atrisk, according to the article.Same hack, different dayHowever, the claims are hardly new. The article in TheWashington Post follows a report issued last year by theOffice of the National Counterintelligence Executive,which monitors espionage against the United States. Whileattacks previously were largely limited to those againstmilitary and government networks, the National CounterintelligenceExecutive maintains that internationalcyberthieves are increasingly stealing US trade secretsfrom private firms and using them to gain an advantagein the undeclared economic war. Attacks originating fromRussia, Israel, and France are also prevalent, but Chinais by far the worst culprit, according to the Office of theNational Counterintelligence Executive.SHUTTERSTOCKS-14 Top 25 Global Distributors <strong>May</strong> <strong>2013</strong>
The economic consequences in the United Statesfrom trade secret and other data theft by foreign partiesare significant but difficult to quantify. The Office of theNational Counterintelligence Executive said the attackscould cost the US economy up to $400 billion a year, butadded that some estimates are substantially lower. However,speaking on a recent edition of Face the Nation, BobOrr of CBS News cited estimates by House IntelligenceCommittee Chairman Mike Rogers who said cybertheftagainst US interests represents up to $400 billion in stolenintellectual property.No innocents?But as the US government seeks to shore up its cyberdefenses,it is not necessarily a passive participant in thisundeclared cyberwar. The US government, according toFrench media reports, was behind attacks on the Frenchpresident’s residence during the months leading up to thepresidential elections last year. Boththe United States and France wouldnot comment on the reports, yet crediblenational French publications, includingL’Express and Le Télégramme,confirmed that the attack took place.Le Monde, one of the most wellrespectednewspapers outside of theUnited States, cited a French diplomatwho said he demanded an explanationfrom the US government about why itaccessed then French President NicolasSarkozy’s e-mails and other data.The United States and Israel wereunofficially behind the Stuxnet virus attack. Consideredto be one of the most complex and lethal virus programsever coded, the virus succeeded in crippling the supervisorycontrol and data acquisition (SCADA) systems thatIranian scientists supposedly use to enrich uranium.The French presidential and Stuxnet attacks are, ofcourse, just two examples of attacks against foreign intereststhat supposedly originated in the United States. To theextent that the United States does apply its vast arsenal ofAs the usgovernment seeksto shore up itscyberdefenses, it isnot necessArily ApAssive pArticipAntin this undeclAredcyberwAr.defense spending to cybersurveillance and even cyberwarfareremains the stuff of chat-room discussions andinformation that will remain classified for decades fromnow, if it ever does become known.Technology theftBut as network attacks against US interests ramp up, theUS government is also obviously worried about how illegallyobtained technologies will shift beyond the shores ofthe United States. The theft potentially has huge implicationsin the technology industry, since stolen technologiesdeveloped in the United States, which spends the most inthe world on research, could be marketed and producedelsewhere.Citing China as the main culprit, Rogers noted duringthe Meet the Press episode how product blueprints andknow-how are stolen by data theft and then used to producespecific products.“I mean,” said Rogers, “theChinese basically are replicatingthese products about as fast as theycan. And we’re not doing very muchabout it. This is the first stage ofwhat could be a very, very big problemif they turn this pillaging ofwealth into attacking key systems.”However, the US government’smore aggressive role in protectingintellectual property from cyberattacksshould have at least someeffect. The US government shouldalso likely step up its more offensiveactions in this covert cyberwar, although those actions willremain very covert.Meanwhile, each skirmish and battle won could havea direct effect on which countries get to produce whichtechnologies.•Bruce Gain is a freelance writer based in France who got hisstart in the electronics world by hacking the family Commodore64 in the early 1980s.<strong>May</strong> <strong>2013</strong> Top 25 Global Distributors S-15



![[270].pdf 37407KB Sep 02 2010 09:55:57 AM - ElectronicsAndBooks](https://img.yumpu.com/50350834/1/185x260/270pdf-37407kb-sep-02-2010-095557-am-electronicsandbooks.jpg?quality=85)
![draaien, A Viruly 1935 OCR c20130324 [320]. - ElectronicsAndBooks](https://img.yumpu.com/49957773/1/190x252/draaien-a-viruly-1935-ocr-c20130324-320-electronicsandbooks.jpg?quality=85)



![20051110 c20051031 [105].pdf 35001KB Feb 18 2009 08:46:32 PM](https://img.yumpu.com/48687202/1/190x253/20051110-c20051031-105pdf-35001kb-feb-18-2009-084632-pm.jpg?quality=85)