CA Identity Manager Implementation Guide - CA Technologies
CA Identity Manager Implementation Guide - CA Technologies
CA Identity Manager Implementation Guide - CA Technologies
- No tags were found...
Create successful ePaper yourself
Turn your PDF publications into a flip-book with our unique Google optimized e-Paper software.
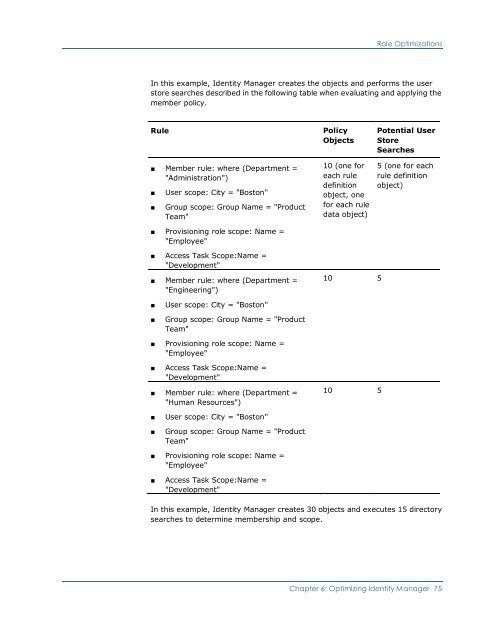
Role OptimizationsIn this example, <strong>Identity</strong> <strong>Manager</strong> creates the objects and performs the userstore searches described in the following table when evaluating and applying themember policy.Rule■ Member rule: where (Department ="Administration")■■User scope: City = "Boston"Group scope: Group Name = "ProductTeam"■ Provisioning role scope: Name ="Employee"PolicyObjects10 (one foreach ruledefinitionobject, onefor each ruledata object)Potential UserStoreSearches5 (one for eachrule definitionobject)■ Access Task Scope:Name ="Development"■ Member rule: where (Department ="Engineering")10 5■■User scope: City = "Boston"Group scope: Group Name = "ProductTeam"■ Provisioning role scope: Name ="Employee"■ Access Task Scope:Name ="Development"■ Member rule: where (Department ="Human Resources")10 5■■User scope: City = "Boston"Group scope: Group Name = "ProductTeam"■ Provisioning role scope: Name ="Employee"■ Access Task Scope:Name ="Development"In this example, <strong>Identity</strong> <strong>Manager</strong> creates 30 objects and executes 15 directorysearches to determine membership and scope.Chapter 6: Optimizing <strong>Identity</strong> <strong>Manager</strong> 75