Introducing
IntroducingWindowsServer2016_ebook
IntroducingWindowsServer2016_ebook
You also want an ePaper? Increase the reach of your titles
YUMPU automatically turns print PDFs into web optimized ePapers that Google loves.
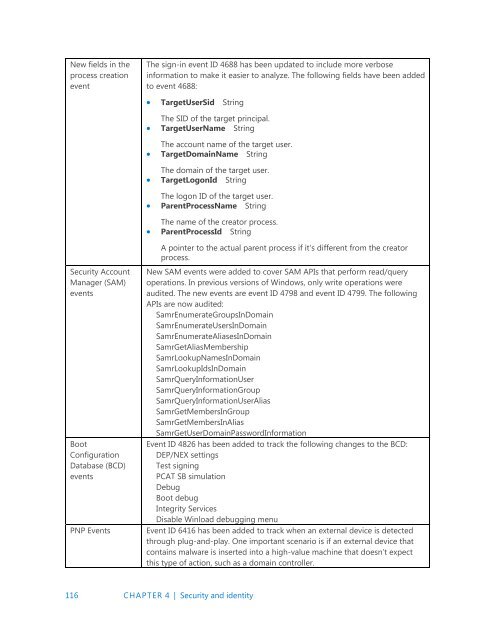
New fields in the<br />
process creation<br />
event<br />
The sign-in event ID 4688 has been updated to include more verbose<br />
information to make it easier to analyze. The following fields have been added<br />
to event 4688:<br />
<br />
TargetUserSid String<br />
<br />
<br />
<br />
<br />
<br />
The SID of the target principal.<br />
TargetUserName String<br />
The account name of the target user.<br />
TargetDomainName String<br />
The domain of the target user.<br />
TargetLogonId String<br />
The logon ID of the target user.<br />
ParentProcessName String<br />
The name of the creator process.<br />
ParentProcessId String<br />
Security Account<br />
Manager (SAM)<br />
events<br />
Boot<br />
Configuration<br />
Database (BCD)<br />
events<br />
PNP Events<br />
A pointer to the actual parent process if it's different from the creator<br />
process.<br />
New SAM events were added to cover SAM APIs that perform read/query<br />
operations. In previous versions of Windows, only write operations were<br />
audited. The new events are event ID 4798 and event ID 4799. The following<br />
APIs are now audited:<br />
SamrEnumerateGroupsInDomain<br />
SamrEnumerateUsersInDomain<br />
SamrEnumerateAliasesInDomain<br />
SamrGetAliasMembership<br />
SamrLookupNamesInDomain<br />
SamrLookupIdsInDomain<br />
SamrQueryInformationUser<br />
SamrQueryInformationGroup<br />
SamrQueryInformationUserAlias<br />
SamrGetMembersInGroup<br />
SamrGetMembersInAlias<br />
SamrGetUserDomainPasswordInformation<br />
Event ID 4826 has been added to track the following changes to the BCD:<br />
DEP/NEX settings<br />
Test signing<br />
PCAT SB simulation<br />
Debug<br />
Boot debug<br />
Integrity Services<br />
Disable Winload debugging menu<br />
Event ID 6416 has been added to track when an external device is detected<br />
through plug-and-play. One important scenario is if an external device that<br />
contains malware is inserted into a high-value machine that doesn’t expect<br />
this type of action, such as a domain controller.<br />
116 CHAPTER 4 | Security and identity