Introducing
IntroducingWindowsServer2016_ebook
IntroducingWindowsServer2016_ebook
Create successful ePaper yourself
Turn your PDF publications into a flip-book with our unique Google optimized e-Paper software.
Securing privileged access<br />
In this section, we are going to explore a few concepts regarding securing privileged access. First we<br />
are going to dive into the concepts of Just-in-Time and Just Enough Administration. Then, we are<br />
going to explain how you combine all of the tools and technologies we have discussed in this chapter<br />
into an implementation strategy for your organization.<br />
Just-in-Time and Just Enough Administration<br />
Just-in-Time (JIT) administration is a fairly basic concept: the principal is that we evolve to a state in<br />
which there are no full-time administrators, or, more specifically, we have no accounts that have fulltime<br />
administrator privileges. Rather, through a simple process, the privileges required are requested<br />
just before they are actually needed, then approved, and then granted to the account for a specific<br />
time period. This ensures that the task can be carried out successfully with the correct amount of<br />
privileges for the allotted time. JIT works in conjunction with Just Enough Administration (JEA) to<br />
secure the correct privileges. In Windows Server 2016, these technologies are combined to provide<br />
Privileged Access Management (PAM).<br />
More info For more information about PAM, go to https://technet.microsoft.com/library/<br />
dn903243.aspx.<br />
Now, let’s take a quick look at JEA. This is part of the Windows Management Framework 5.0 package<br />
and has been supported since Windows Server 2008 R2. Using JEA, you can assign specific privileges<br />
(just enough of them) to a user account that are needed to perform a given required function. This<br />
means that you don’t need to assign a user to an administrator account and then remember to<br />
remove that person later. JEA gives us the role-based access control (RBAC) that modern enterprises<br />
require to achieve more secure environments.<br />
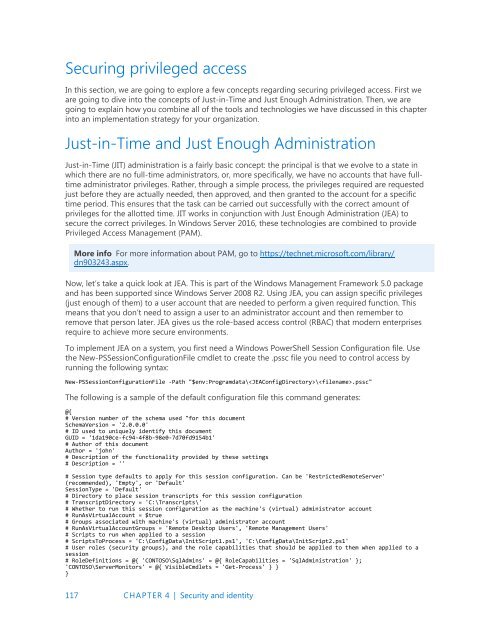
To implement JEA on a system, you first need a Windows PowerShell Session Configuration file. Use<br />
the New-PSSessionConfigurationFile cmdlet to create the .pssc file you need to control access by<br />
running the following syntax:<br />
New-PSSessionConfigurationFile -Path "$env:Programdata\\.pssc"<br />
The following is a sample of the default configuration file this command generates:<br />
@{<br />
# Version number of the schema used "for this document<br />
SchemaVersion = '2.0.0.0'<br />
# ID used to uniquely identify this document<br />
GUID = '1da190ce-fc94-4f8b-98e0-7d70fd9154b1'<br />
# Author of this document<br />
Author = 'john'<br />
# Description of the functionality provided by these settings<br />
# Description = ''<br />
# Session type defaults to apply for this session configuration. Can be 'RestrictedRemoteServer'<br />
(recommended), 'Empty', or 'Default'<br />
SessionType = 'Default'<br />
# Directory to place session transcripts for this session configuration<br />
# TranscriptDirectory = 'C:\Transcripts\'<br />
# Whether to run this session configuration as the machine's (virtual) administrator account<br />
# RunAsVirtualAccount = $true<br />
# Groups associated with machine's (virtual) administrator account<br />
# RunAsVirtualAccountGroups = 'Remote Desktop Users', 'Remote Management Users'<br />
# Scripts to run when applied to a session<br />
# ScriptsToProcess = 'C:\ConfigData\InitScript1.ps1', 'C:\ConfigData\InitScript2.ps1'<br />
# User roles (security groups), and the role capabilities that should be applied to them when applied to a<br />
session<br />
# RoleDefinitions = @{ 'CONTOSO\SqlAdmins' = @{ RoleCapabilities = 'SqlAdministration' };<br />
'CONTOSO\ServerMonitors' = @{ VisibleCmdlets = 'Get-Process' } }<br />
}<br />
117 CHAPTER 4 | Security and identity