Introduction to the Apache Web Server - ApacheCon
Introduction to the Apache Web Server - ApacheCon
Introduction to the Apache Web Server - ApacheCon
Create successful ePaper yourself
Turn your PDF publications into a flip-book with our unique Google optimized e-Paper software.
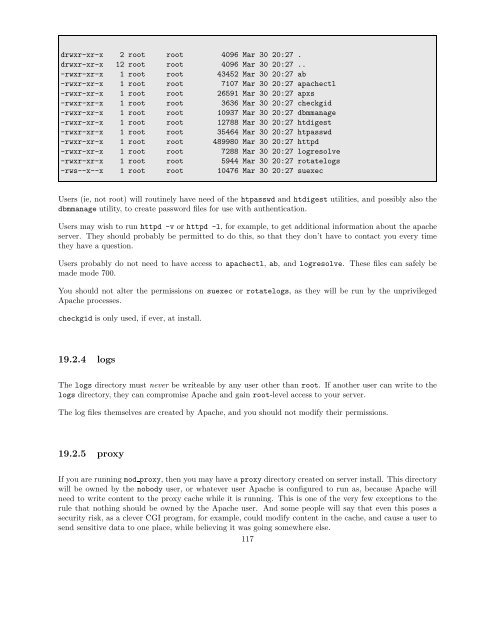
drwxr-xr-x 2 root root 4096 Mar 30 20:27 .<br />
drwxr-xr-x 12 root root 4096 Mar 30 20:27 ..<br />
-rwxr-xr-x 1 root root 43452 Mar 30 20:27 ab<br />
-rwxr-xr-x 1 root root 7107 Mar 30 20:27 apachectl<br />
-rwxr-xr-x 1 root root 26591 Mar 30 20:27 apxs<br />
-rwxr-xr-x 1 root root 3636 Mar 30 20:27 checkgid<br />
-rwxr-xr-x 1 root root 10937 Mar 30 20:27 dbmmanage<br />
-rwxr-xr-x 1 root root 12788 Mar 30 20:27 htdigest<br />
-rwxr-xr-x 1 root root 35464 Mar 30 20:27 htpasswd<br />
-rwxr-xr-x 1 root root 489980 Mar 30 20:27 httpd<br />
-rwxr-xr-x 1 root root 7288 Mar 30 20:27 logresolve<br />
-rwxr-xr-x 1 root root 5944 Mar 30 20:27 rotatelogs<br />
-rws--x--x 1 root root 10476 Mar 30 20:27 suexec<br />
Users (ie, not root) will routinely have need of <strong>the</strong> htpasswd and htdigest utilities, and possibly also <strong>the</strong><br />
dbmmanage utility, <strong>to</strong> create password files for use with au<strong>the</strong>ntication.<br />
Users may wish <strong>to</strong> run httpd -v or httpd -l, for example, <strong>to</strong> get additional information about <strong>the</strong> apache<br />
server. They should probably be permitted <strong>to</strong> do this, so that <strong>the</strong>y don’t have <strong>to</strong> contact you every time<br />
<strong>the</strong>y have a question.<br />
Users probably do not need <strong>to</strong> have access <strong>to</strong> apachectl, ab, and logresolve. These files can safely be<br />
made mode 700.<br />
You should not alter <strong>the</strong> permissions on suexec or rotatelogs, as <strong>the</strong>y will be run by <strong>the</strong> unprivileged<br />
<strong>Apache</strong> processes.<br />
checkgid is only used, if ever, at install.<br />
19.2.4 logs<br />
The logs direc<strong>to</strong>ry must never be writeable by any user o<strong>the</strong>r than root. If ano<strong>the</strong>r user can write <strong>to</strong> <strong>the</strong><br />
logs direc<strong>to</strong>ry, <strong>the</strong>y can compromise <strong>Apache</strong> and gain root-level access <strong>to</strong> your server.<br />
The log files <strong>the</strong>mselves are created by <strong>Apache</strong>, and you should not modify <strong>the</strong>ir permissions.<br />
19.2.5 proxy<br />
If you are running mod proxy, <strong>the</strong>n you may have a proxy direc<strong>to</strong>ry created on server install. This direc<strong>to</strong>ry<br />
will be owned by <strong>the</strong> nobody user, or whatever user <strong>Apache</strong> is configured <strong>to</strong> run as, because <strong>Apache</strong> will<br />
need <strong>to</strong> write content <strong>to</strong> <strong>the</strong> proxy cache while it is running. This is one of <strong>the</strong> very few exceptions <strong>to</strong> <strong>the</strong><br />
rule that nothing should be owned by <strong>the</strong> <strong>Apache</strong> user. And some people will say that even this poses a<br />
security risk, as a clever CGI program, for example, could modify content in <strong>the</strong> cache, and cause a user <strong>to</strong><br />
send sensitive data <strong>to</strong> one place, while believing it was going somewhere else.<br />
117