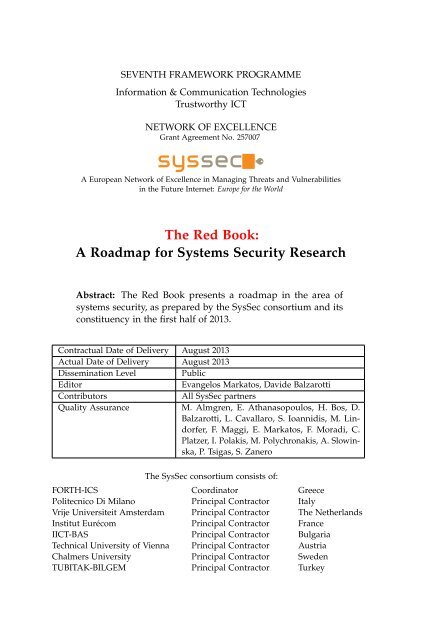
- Page 1: SEVENTH FRAMEWORK PROGRAMMETHERED B
- Page 5: SYSSEC TASK FORCE for the ROADMAPon
- Page 8 and 9: Journalists may want to focus on se
- Page 10 and 11: Contents16 Forward 10917 Federal Pl
- Page 12 and 13: 1. Executive SummaryThe major domai
- Page 15 and 16: 2 IntroductionCyberspace penetratio
- Page 17 and 18: 2.2. Mapping the Threats We FearShe
- Page 19 and 20: 2.3. Listing the Assets We ValueShe
- Page 21 and 22: 2.4. Understanding the Domains of t
- Page 23 and 24: 2.5. Horizontal Research Directions
- Page 25: 2.6. What If?world where the threat
- Page 29 and 30: 3 In Search of Lost AnonymityDawn o
- Page 31 and 32: 3.4. State of the ArtDo we build a
- Page 33: 3.6. Example problems3.5.3 Deletion
- Page 36 and 37: 4. Software VulnerabilitiesInsecure
- Page 38 and 39: 4. Software Vulnerabilitiesinformat
- Page 40 and 41: 4. Software Vulnerabilitiescations
- Page 43 and 44: 5 Social NetworksFraming the famili
- Page 45 and 46: 5.2. What Is Expected to Happen?eva
- Page 47 and 48: 5.5. Research Gapsonline ratings. A
- Page 49 and 50: 6 Critical Infrastructure SecurityG
- Page 51 and 52: 6.2. Who Is Going to Be Affected?6.
- Page 53 and 54:
6.5. State of the Artretroactively
- Page 55 and 56:
6.6. Research Gapsand authenticity.
- Page 57:
6.7. Example Problemsyour ICS infra
- Page 60 and 61:
7. Authentication and Authorization
- Page 62 and 63:
7. Authentication and Authorization
- Page 64 and 65:
7. Authentication and Authorization
- Page 66 and 67:
7. Authentication and Authorization
- Page 68 and 69:
8. Security of Mobile Devicesfinanc
- Page 70 and 71:
8. Security of Mobile Devicesinform
- Page 72 and 73:
8. Security of Mobile DevicesFinall
- Page 75 and 76:
9 Legacy SystemsJoined into a singl
- Page 77 and 78:
9.5. State of the Artas an attack.
- Page 79:
9.7. Example Problemsdicators, they
- Page 82 and 83:
10. Usable SecurityInternet, for ex
- Page 84 and 85:
10. Usable SecurityA perfect exampl
- Page 86 and 87:
10. Usable Security10.7 Example Pro
- Page 89 and 90:
11 The Botnet that Would not DieLin
- Page 91 and 92:
11.1. What Is the Problem?messages,
- Page 93 and 94:
11.4. What Is the Worst That Can Ha
- Page 95 and 96:
12 MalwareMost users and administra
- Page 97 and 98:
12.4. What Is the Worst That Can Ha
- Page 99 and 100:
12.7. Example Problemsternative sof
- Page 101 and 102:
13 Social Engineering and PhishingN
- Page 103 and 104:
13.3. What Is Expected to Happen?(v
- Page 105 and 106:
13.4. What Is the Worst That Can Ha
- Page 107 and 108:
13.5. State of the ArtScammers oper
- Page 109:
13.7. Example ProblemsThis will she
- Page 112 and 113:
14. Grand Challenges14.3 Provide Pr
- Page 115 and 116:
15 Cyber Security: A Crisisof Prior
- Page 117 and 118:
16 Forward: Managing Threats inICT
- Page 119 and 120:
16.2. Recommendationsoperating on)
- Page 121 and 122:
17 Federal Plan for Cyber Security
- Page 123 and 124:
17.2. Recommendations“Make cyber
- Page 125 and 126:
18 EffectsPlus Trust and SecurityRe
- Page 127 and 128:
18.3. Vision18.2.3 Changes in Socie
- Page 129 and 130:
19 Digital Government: Building a 2
- Page 131 and 132:
20 H2020: The Challenge of Providin
- Page 133:
20.2. Societal Perspective• “En
- Page 136 and 137:
21. RISEPTIS Report• Taking advan
- Page 139 and 140:
22 ENISA Threat Landscape and Indus
- Page 141 and 142:
22.2. Emerging Issues per Area9. Id
- Page 143 and 144:
22.4. Industrial Reportsrepresent t
- Page 145 and 146:
23 Cyber Security and InformationIn
- Page 147:
23.3. Recommendationsflexible, dist
- Page 150 and 151:
24. Cyber Security Strategy• All
- Page 152 and 153:
24. Cyber Security Strategydinate t
- Page 154 and 155:
25. The Dutch National Cyber Securi
- Page 156 and 157:
25. The Dutch National Cyber Securi
- Page 158 and 159:
25. The Dutch National Cyber Securi
- Page 160 and 161:
25. The Dutch National Cyber Securi
- Page 162 and 163:
25. The Dutch National Cyber Securi
- Page 164 and 165:
25. The Dutch National Cyber Securi
- Page 166 and 167:
A. Methodologiessummarized document
- Page 168 and 169:
B. SysSec Threats Landscape Evoluti
- Page 170 and 171:
B. SysSec Threats Landscape Evoluti
- Page 172 and 173:
B. SysSec Threats Landscape Evoluti
- Page 174 and 175:
Bibliography[22] Google Accounts Au
- Page 176 and 177:
Bibliography[69] Obama Order Sped U
- Page 178 and 179:
Bibliography[108] J. Bonneau, C. He
- Page 180 and 181:
Bibliography[150] D. Desai. Malware
- Page 182 and 183:
Bibliography[194] V. George, T. Pia
- Page 184 and 185:
Bibliography[233] G. S. Kc, A. D. K
- Page 186 and 187:
Bibliography[272] G. McDonald, L. O
- Page 188 and 189:
Bibliography[309] E. Passerini, R.
- Page 190 and 191:
Bibliography[350] S. Sidiroglou and
- Page 192 and 193:
Bibliography[387] D. Wagner, J. S.
- Page 194:
SEVENTH FRAMEWORK PROGRAMMEInformat