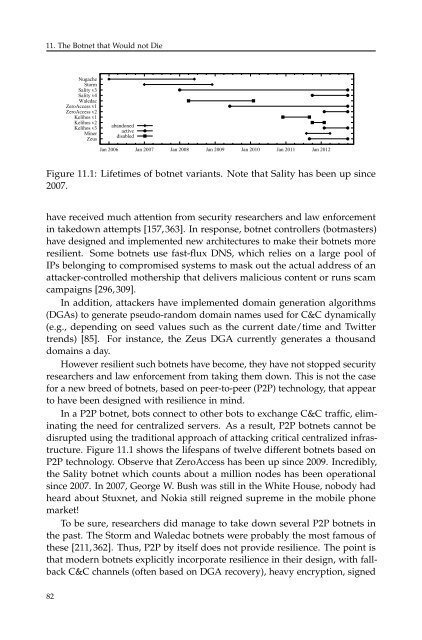
11. The Botnet that Would not DieNugacheStormSality v3Sality v4WaledacZeroAccess v1ZeroAccess v2Kelihos v1Kelihos v2Kelihos v3MinerZeusabandonedactivedisabledJan 2006 Jan 2007 Jan 2008 Jan 2009 Jan 2010 Jan 2011 Jan 2012Figure 11.1: Lifetimes of botnet variants. Note that Sality has been up since2007.have received much attention from security researchers and law enforcementin takedown attempts [157,363]. In response, botnet controllers (botmasters)have designed and implemented new architectures to make their botnets moreresilient. Some botnets use fast-flux DNS, which relies on a large pool ofIPs belonging to compromised systems to mask out the actual address of anattacker-controlled mothership that delivers malicious content or runs scamcampaigns [296, 309].In addition, attackers have implemented domain generation algorithms(DGAs) to generate pseudo-random domain names used for C&C dynamically(e.g., depending on seed values such as the current date/time and Twittertrends) [85]. For instance, the Zeus DGA currently generates a thousanddomains a day.However resilient such botnets have become, they have not stopped securityresearchers and law enforcement from taking them down. This is not the casefor a new breed of botnets, based on peer-to-peer (P2P) technology, that appearto have been designed with resilience in mind.In a P2P botnet, bots connect to other bots to exchange C&C traffic, eliminatingthe need for centralized servers. As a result, P2P botnets cannot bedisrupted using the traditional approach of attacking critical centralized infrastructure.Figure 11.1 shows the lifespans of twelve different botnets based onP2P technology. Observe that ZeroAccess has been up since 2009. Inc<strong>red</strong>ibly,the Sality botnet which counts about a million nodes has been operationalsince 2007. In 2007, George W. Bush was still in the White House, nobody hadheard about Stuxnet, and Nokia still reigned supreme in the mobile phonemarket!To be sure, researchers did manage to take down several P2P botnets inthe past. The Storm and Waledac botnets were probably the most famous ofthese [211, 362]. Thus, P2P by itself does not provide resilience. The point isthat modern botnets explicitly incorporate resilience in their design, with fallbackC&C channels (often based on DGA recovery), heavy encryption, signed82
11.1. What Is the Problem?messages, slow peerlist exchanges, and reputation-based peer replacement.Moreover, unlike earlier P2P botnets like Storm and Waledac, almost all newP2P botnets use an unstructu<strong>red</strong> P2P infrastructure—which turns out to bemuch harder to take down.11.1.2 ResilienceWe will distinguish between different kinds of resilience for P2P networks:Intelligence gathering resilience: For many attacks on (and mitigation techniquesfor) P2P botnets, we need to find out who is infected and perhapseven the topology of the P2P network.Modern botnets are made resilient against intelligence gathering forinstance by keeping most bots behind NATs and firewalls (making themimpossible to crawl), not using explicit identifiers (making it impossibleto estimate the exact number of infected machines, as IP addresses areboth reused and renewed), not exchanging peers frequently and notexchanging many peers to begin with (making crawling very slow), etc.All these techniques are employed even today by botnets like Sality andZeus. For instance, Sality bots exchange peers once every 40 minutesand Zeus every 30 minutes. Moreover, Sality exchanges only a singlepeer at a time. A future botnet may be slower still. If you are too slow inmapping out the bots, the churn in the P2P network will have made yournumbers obsolete almost immediately. This limits the measures that youcan take based on these numbers. For instance, placing many peers inquarantine unnecessarily will probably not be acceptable.Disruption resilience: well-known attacks to disrupt P2P botnets includesinkholing (where all bots are <strong>red</strong>irected to an attacker-controlled machinecalled a sinkhole), and command poisoning (where we distribute spoofedcommands to other bots and/or transmit invalid messages). A simplemeasure against command poisoning is to protect the command usingsignatures and nonces (e.g., Kelihos and Sality v4 use RSA2048, whileZeroAccess uses RSA1024). Typically, encryption is used to prevent themfrom being visible in the network.Moreover, to sinkhole an unstructu<strong>red</strong> P2P botnet, it is crucial that we areable to poison other peers’ peer lists. Modern botnets spend considerableeffort to prevent this. For instance, by not exchanging many peers (e.g.,Sality exchanges only one peer at a time), not replacing peers with a highreputation (Sality), replacing peers in a non-p<strong>red</strong>ictable manner (e.g.,Sality picks peers at random, rather than recent ones, like Kelihos andNugache, or peers that are close like Zeus and Storm), by providing abackup C&C channels (such as Zeus’s DGA-based channel, or Kelihos’83
- Page 1:
SEVENTH FRAMEWORK PROGRAMMETHERED B
- Page 4 and 5:
The Red Book. ©2013 The SysSec Con
- Page 7 and 8:
PrefaceAfter the completion of its
- Page 9 and 10:
Contents1 Executive Summary 32 Intr
- Page 11 and 12:
1 Executive SummaryBased on publish
- Page 13:
1.2. Grand Challenges4. will have t
- Page 16 and 17:
2. Introductionwho want to get at t
- Page 18 and 19:
2. Introduction• Although conside
- Page 20 and 21:
2. Introductionfuture, where each a
- Page 22 and 23:
2. Introductiondrones), such sensor
- Page 24 and 25:
2. Introductioncover our energy nee
- Page 27:
Part I: Threats Identified
- Page 30 and 31:
3. In Search of Lost Anonymity3.2 W
- Page 32 and 33:
3. In Search of Lost Anonymityguide
- Page 35 and 36:
4 Software VulnerabilitiesExtending
- Page 37 and 38:
4.1. What Is the Problem?infrastruc
- Page 39 and 40: 4.5. State of the Artparts of criti
- Page 41: 4.7. Example Problemstem mitigation
- Page 44 and 45: 5. Social Networks5.1 Who Is Going
- Page 46 and 47: 5. Social Networksby such an applic
- Page 48 and 49: 5. Social Networksdisasters. This r
- Page 50 and 51: 6. Critical Infrastructure Security
- Page 52 and 53: 6. Critical Infrastructure Security
- Page 54 and 55: 6. Critical Infrastructure Security
- Page 56 and 57: 6. Critical Infrastructure Security
- Page 59 and 60: 7 Authentication and AuthorizationH
- Page 61 and 62: 7.2. Who Is Going to Be Affected?so
- Page 63 and 64: 7.5. State of the ArtFinally, ident
- Page 65 and 66: 7.6. Research Gapshashes and evalua
- Page 67 and 68: 8 Security of Mobile DevicesIn an e
- Page 69 and 70: 8.3. What Is the Worst That Can Hap
- Page 71 and 72: 8.4. State of the ArtAll the other
- Page 73: 8.6. Example Problemserated anomaly
- Page 76 and 77: 9. Legacy Systemsthe execution of a
- Page 78 and 79: 9. Legacy Systemsparts of the progr
- Page 81 and 82: 10 Usable SecurityKeys, locks, and
- Page 83 and 84: 10.4. What Is the Worst That Can Ha
- Page 85 and 86: 10.6. Research Gaps10.6 Research Ga
- Page 87: 10.7. Example Problemsof value for
- Page 92 and 93: 11. The Botnet that Would not Diefa
- Page 94 and 95: 11. The Botnet that Would not Dieti
- Page 96 and 97: 12. Malwarethan 128 million malware
- Page 98 and 99: 12. Malwareequipped with auto-updat
- Page 100 and 101: 12. Malwarethe introduction of App
- Page 102 and 103: 13. Social Engineering and Phishing
- Page 104 and 105: 13. Social Engineering and Phishing
- Page 106 and 107: 13. Social Engineering and Phishing
- Page 108 and 109: 13. Social Engineering and Phishing
- Page 111 and 112: 14 Grand ChallengesOne of the most
- Page 113: Part II: Related Work
- Page 116 and 117: 15. A Crisis of Prioritization•
- Page 118 and 119: 16. Forwardare accessible from the
- Page 120 and 121: 16. ForwardRecommendation 4: “The
- Page 122 and 123: 17. Federal Plan for Cyber Security
- Page 124 and 125: 17. Federal Plan for Cyber Security
- Page 126 and 127: 18. EffectsPlus18.1 Roadmap Structu
- Page 128 and 129: 18. EffectsPlus18.6 Identified Prio
- Page 130 and 131: 19. Digital GovernmentThe roadmap o
- Page 132 and 133: 20. Horizon2020• “Making cyber
- Page 135 and 136: 21 Trust in the Information Society
- Page 137: 21.2. Recommendationsallows for the
- Page 140 and 141:
22. ENISA Threat Landscape2. Malwar
- Page 142 and 143:
22. ENISA Threat LandscapeSocial Te
- Page 144 and 145:
22. ENISA Threat Landscapewriters w
- Page 146 and 147:
23. Cyber Security Research Worksho
- Page 149 and 150:
24 Cyber Security Strategy of theEu
- Page 151 and 152:
24.2. Strategic PrioritiesProposed
- Page 153 and 154:
25 The Dutch National Cyber Securit
- Page 155 and 156:
25.1. ContextsInternet (e.g., smart
- Page 157 and 158:
25.1. Contextsdefensive approaches
- Page 159 and 160:
25.2. Research Themesand radio broa
- Page 161 and 162:
25.2. Research Themesconsists of se
- Page 163 and 164:
25.2. Research ThemesRisk managemen
- Page 165 and 166:
AMethodologiesIn this appendix we o
- Page 167 and 168:
BSysSec Threats Landscape Evolution
- Page 169 and 170:
B.4. SysSec 2013 Threats LandscapeT
- Page 171 and 172:
B.4. SysSec 2013 Threats LandscapeS
- Page 173 and 174:
Bibliography[1] 10 Questions for Ke
- Page 175 and 176:
Bibliography[45] SCADA & Security o
- Page 177 and 178:
Bibliography[88] A. Avizienis, J.-C
- Page 179 and 180:
Bibliography[130] G. Cluley. 600,00
- Page 181 and 182:
Bibliography[172] D. Evans. Top 25
- Page 183 and 184:
Bibliography[214] ICS-CERT. Monthly
- Page 185 and 186:
Bibliography[253] C. Lever, M. Anto
- Page 187 and 188:
Bibliography[291] Mozilla. Browseri
- Page 189 and 190:
Bibliography[329] F. Raja, K. Hawke
- Page 191 and 192:
Bibliography[370] T. Telegraph. Bog
- Page 193 and 194:
Bibliography[407] W. Yang, N. Li, Y