Control Manager Installation Guide - Trend Micro? Online Help
Control Manager Installation Guide - Trend Micro? Online Help
Control Manager Installation Guide - Trend Micro? Online Help
Create successful ePaper yourself
Turn your PDF publications into a flip-book with our unique Google optimized e-Paper software.
<strong>Control</strong> <strong>Manager</strong> 6.0 <strong>Installation</strong> <strong>Guide</strong><br />
2-18<br />
Note<br />
Before adjusting the interval to a number below 15 minutes, study your existing<br />
network traffic to understand the impact of increased use of network bandwidth.<br />
Network Protocols<br />
<strong>Control</strong> <strong>Manager</strong> uses the UDP and TCP protocols for communication.<br />
Source of Network Traffic<br />
Log Traffic<br />
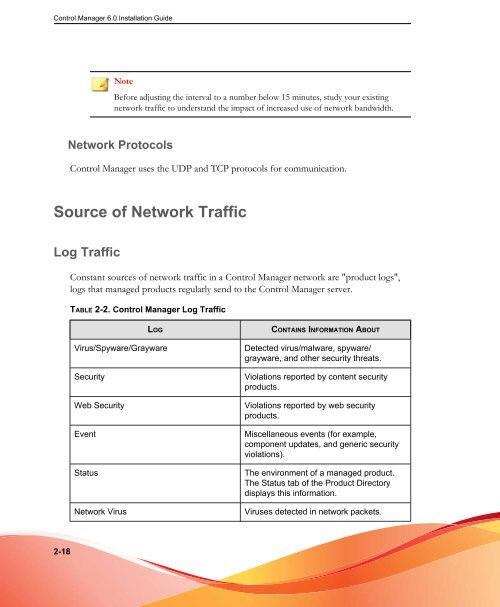
Constant sources of network traffic in a <strong>Control</strong> <strong>Manager</strong> network are "product logs",<br />
logs that managed products regularly send to the <strong>Control</strong> <strong>Manager</strong> server.<br />
TABLE 2-2. <strong>Control</strong> <strong>Manager</strong> Log Traffic<br />
LOG CONTAINS INFORMATION ABOUT<br />
Virus/Spyware/Grayware Detected virus/malware, spyware/<br />
grayware, and other security threats.<br />
Security Violations reported by content security<br />
products.<br />
Web Security Violations reported by web security<br />
products.<br />
Event Miscellaneous events (for example,<br />
component updates, and generic security<br />
violations).<br />
Status The environment of a managed product.<br />
The Status tab of the Product Directory<br />
displays this information.<br />
Network Virus Viruses detected in network packets.