TITRE Adaptive Packet Video Streaming Over IP Networks - LaBRI
TITRE Adaptive Packet Video Streaming Over IP Networks - LaBRI
TITRE Adaptive Packet Video Streaming Over IP Networks - LaBRI
You also want an ePaper? Increase the reach of your titles
YUMPU automatically turns print PDFs into web optimized ePapers that Google loves.
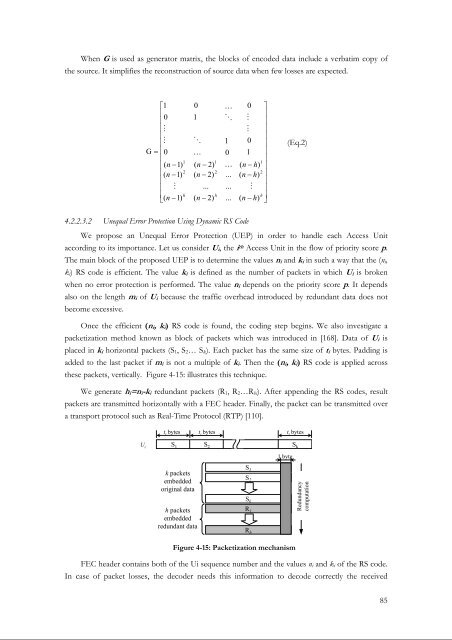
When G is used as generator matrix, the blocks of encoded data include a verbatim copy of<br />
the source. It simplifies the reconstruction of source data when few losses are expected.<br />
⎡1<br />
⎢<br />
⎢<br />
0<br />
⎢M<br />
⎢<br />
⎢M<br />
G = ⎢0<br />
⎢<br />
⎢(<br />
n −1)<br />
⎢(<br />
n −1)<br />
⎢<br />
⎢ M<br />
⎢<br />
⎣(<br />
n −1)<br />
1<br />
2<br />
h<br />
0<br />
1<br />
O<br />
K<br />
( n − 2)<br />
( n − 2)<br />
...<br />
( n − 2)<br />
1<br />
2<br />
h<br />
K<br />
O<br />
1<br />
0<br />
K<br />
...<br />
...<br />
...<br />
0 ⎤<br />
M<br />
⎥<br />
⎥<br />
M ⎥<br />
⎥<br />
0 ⎥<br />
1 ⎥<br />
⎥<br />
1<br />
( n − h)<br />
⎥<br />
2<br />
( n − h)<br />
⎥<br />
⎥<br />
M ⎥<br />
h<br />
( n − h)<br />
⎥<br />
⎦<br />
(Eq.2)<br />
4.2.2.3.2 Unequal Error Protection Using Dynamic RS Code<br />
We propose an Unequal Error Protection (UEP) in order to handle each Access Unit<br />
according to its importance. Let us consider U , i the i th Access Unit in the flow of priority score p.<br />
The main block of the proposed UEP is to determine the values n i and k i in such a way that the (n i ,<br />
k i ) RS code is efficient. The value k i is defined as the number of packets in which U i is broken<br />
when no error protection is performed. The value n i depends on the priority score p. It depends<br />
also on the length m i of U i because the traffic overhead introduced by redundant data does not<br />
become excessive.<br />
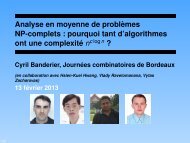
Once the efficient (n i , k ) i RS code is found, the coding step begins. We also investigate a<br />
packetization method known as block of packets which was introduced in [168]. Data of U i is<br />
placed in k i horizontal packets (S 1 , S 2 … S k ). Each packet has the same size of t i bytes. Padding is<br />
added to the last packet if m i is not a multiple of k . i Then the (n i , k ) i RS code is applied across<br />
these packets, vertically. Figure 4-15: illustrates this technique.<br />
We generate h i =n i -k i redundant packets (R 1 , R 2 …R hi ). After appending the RS codes, result<br />
packets are transmitted horizontally with a FEC header. Finally, the packet can be transmitted over<br />
a transport protocol such as Real-Time Protocol (RTP) [110].<br />
U i<br />
S 1 S 2 S k<br />
t i<br />
bytes t i<br />
bytes<br />
t i<br />
bytes<br />
1 byte<br />
k packets<br />
embedded<br />
original data<br />
h packets<br />
embedded<br />
redundant data<br />
S 1<br />
S 2<br />
S k<br />
R 1<br />
R h<br />
Redundancy<br />
computation<br />
Figure 4-15: <strong>Packet</strong>ization mechanism<br />
FEC header contains both of the Ui sequence number and the values n i and k i of the RS code.<br />
In case of packet losses, the decoder needs this information to decode correctly the received<br />
85