DARPA ULTRALOG Final Report - Industrial and Manufacturing ...
DARPA ULTRALOG Final Report - Industrial and Manufacturing ...
DARPA ULTRALOG Final Report - Industrial and Manufacturing ...
Create successful ePaper yourself
Turn your PDF publications into a flip-book with our unique Google optimized e-Paper software.
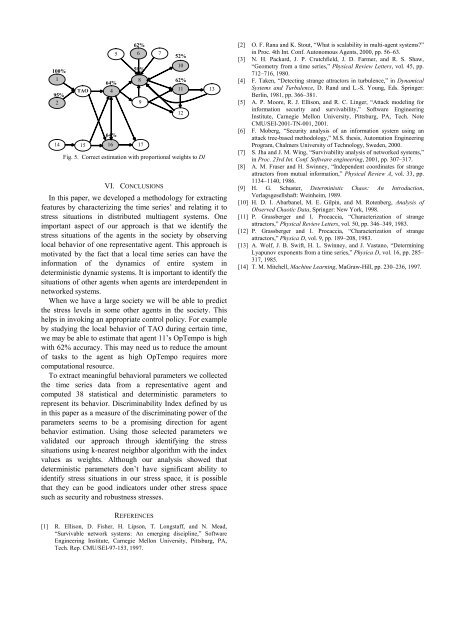
100%<br />
1<br />
95%<br />
2<br />
14 15<br />
64%<br />
TAO 4<br />
64%<br />
62%<br />
5 6 7<br />
59%<br />
VI. CONCLUSIONS<br />
In this paper, we developed a methodology for extracting<br />
features by characterizing the time series’ <strong>and</strong> relating it to<br />
stress situations in distributed multiagent systems. One<br />
important aspect of our approach is that we identify the<br />
stress situations of the agents in the society by observing<br />
local behavior of one representative agent. This approach is<br />
motivated by the fact that a local time series can have the<br />
information of the dynamics of entire system in<br />
deterministic dynamic systems. It is important to identify the<br />
situations of other agents when agents are interdependent in<br />
networked systems.<br />
When we have a large society we will be able to predict<br />
the stress levels in some other agents in the society. This<br />
helps in invoking an appropriate control policy. For example<br />
by studying the local behavior of TAO during certain time,<br />
we may be able to estimate that agent 11’s OpTempo is high<br />
with 62% accuracy. This may need us to reduce the amount<br />
of tasks to the agent as high OpTempo requires more<br />
computational resource.<br />
To extract meaningful behavioral parameters we collected<br />
the time series data from a representative agent <strong>and</strong><br />
computed 38 statistical <strong>and</strong> deterministic parameters to<br />
represent its behavior. Discriminability Index defined by us<br />
in this paper as a measure of the discriminating power of the<br />
parameters seems to be a promising direction for agent<br />
behavior estimation. Using those selected parameters we<br />
validated our approach through identifying the stress<br />
situations using k-nearest neighbor algorithm with the index<br />
values as weights. Although our analysis showed that<br />
deterministic parameters don’t have significant ability to<br />
identify stress situations in our stress space, it is possible<br />
that they can be good indicators under other stress space<br />
such as security <strong>and</strong> robustness stresses.<br />
8<br />
9<br />
16 17<br />
52%<br />
10<br />
62%<br />
Fig. 5. Correct estimation with proportional weights to DI<br />
11<br />
12<br />
13<br />
[2] O. F. Rana <strong>and</strong> K. Stout, “What is scalability in multi-agent systems?”<br />
in Proc. 4th Int. Conf. Autonomous Agents, 2000, pp. 56–63.<br />
[3] N. H. Packard, J. P. Crutchfield, J. D. Farmer, <strong>and</strong> R. S. Shaw,<br />
“Geometry from a time series,” Physical Review Letters, vol. 45, pp.<br />
712–716, 1980.<br />
[4] F. Taken, “Detecting strange attractors in turbulence,” in Dynamical<br />
Systems <strong>and</strong> Turbulence, D. R<strong>and</strong> <strong>and</strong> L.-S. Young, Eds. Springer:<br />
Berlin, 1981, pp. 366–381.<br />
[5] A. P. Moore, R. J. Ellison, <strong>and</strong> R. C. Linger, “Attack modeling for<br />
information security <strong>and</strong> survivability,” Software Engineering<br />
Institute, Carnegie Mellon University, Pittsburg, PA, Tech. Note<br />
CMU/SEI-2001-TN-001, 2001.<br />
[6] F. Moberg, “Security analysis of an information system using an<br />
attack tree-based methodology,” M.S. thesis, Automation Engineering<br />
Program, Chalmers University of Technology, Sweden, 2000.<br />
[7] S. Jha <strong>and</strong> J. M. Wing, “Survivability analysis of networked systems,”<br />
in Proc. 23rd Int. Conf. Software engineering, 2001, pp. 307–317.<br />
[8] A. M. Fraser <strong>and</strong> H. Swinney, “Independent coordinates for strange<br />
attractors from mutual information,” Physical Review A, vol. 33, pp.<br />
1134–1140, 1986.<br />
[9] H. G. Schuster, Deterministic Chaos: An Introduction,<br />
Verlagsgesellshaft: Weinheim, 1989.<br />
[10] H. D. I. Abarbanel, M. E. Gilpin, <strong>and</strong> M. Rotenberg, Analysis of<br />
Observed Chaotic Data, Springer: New York, 1998.<br />
[11] P. Grassberger <strong>and</strong> I. Procaccia, “Characterization of strange<br />
attractors,” Physical Review Letters, vol. 50, pp. 346–349, 1983.<br />
[12] P. Grassberger <strong>and</strong> I. Procaccia, “Characterization of strange<br />
attractors,” Physica D, vol. 9, pp. 189–208, 1983.<br />
[13] A. Wolf, J. B. Swift, H. L. Swinney, <strong>and</strong> J. Vastano, “Determining<br />
Lyapunov exponents from a time series,” Physica D, vol. 16, pp. 285–<br />
317, 1985.<br />
[14] T. M. Mitchell, Machine Learning, MaGraw-Hill, pp. 230–236, 1997.<br />
REFERENCES<br />
[1] R. Ellison, D. Fisher, H. Lipson, T. Longstaff, <strong>and</strong> N. Mead,<br />
“Survivable network systems: An emerging discipline,” Software<br />
Engineering Institute, Carnegie Mellon University, Pittsburg, PA,<br />
Tech. Rep. CMU/SEI-97-153, 1997.