ENFORCEMENT
eop_ipec_jointstrategicplan_hi-res
eop_ipec_jointstrategicplan_hi-res
Create successful ePaper yourself
Turn your PDF publications into a flip-book with our unique Google optimized e-Paper software.
Joint Strategic Plan on Intellectual Property Enforcement<br />
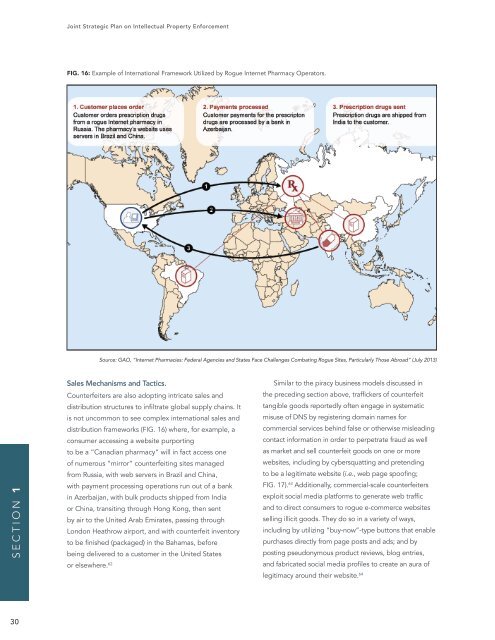
Figure FIG. 1: 16: Map Example of a Rogue of International Internet Framework Pharmacy Utilized Operation by Rogue Internet Pharmacy Operators.<br />
SECTION 1<br />
Source: GAO, “Internet Pharmacies: Federal Agencies and States Face Challenges Combating Rogue Sites, Particularly Those Abroad” (July 2013)<br />
Notes: This figure is based on a figure that was published in Kirill Levchenko et al., “Click<br />
Trajectories: End-to-End Analysis of the Spam Value Chain” (paper presented at the Institute of<br />
Sales Mechanisms and Tactics. Electrical and Electronics Engineers Similar Symposium to the piracy on Security business and Privacy, models Oakland, discussed CA, in May 22-25,<br />
2011), accessed October 1, 2012, http://cseweb.ucsd.edu/~savage/papers/Oakland11.pdf. The study<br />
Counterfeiters are also adopting intricate was sales funded and in part by grants the from preceding the National section Science above, Foundation. traffickers of counterfeit<br />
distribution structures to infiltrate global supply chains. It tangible goods reportedly often engage in systematic<br />
is not uncommon to see complex international Identifying sales rogue and Internet misuse pharmacy of DNS by registering operators domain for investigation names for and<br />
possible prosecution can be challenging as they take steps to remain<br />
distribution frameworks (FIG. 16) where, for example, a commercial services behind false or otherwise misleading<br />
anonymous. According to officials from multiple federal agencies, rogue<br />
consumer accessing a website purporting<br />
contact information in order to perpetrate fraud as well<br />
Internet pharmacy operators generally provide inaccurate contact<br />
to be a “Canadian pharmacy” will in fact information access one to domain as name market registrars and sell counterfeit and often goods use on technological one or more and<br />
of numerous “mirror” counterfeiting sites other managed means to disguise websites, their including identities, by cybersquatting physical locations, and pretending and affiliations<br />
from Russia, with web servers in Brazil and China,<br />
to be a legitimate website (i.e., web page spoofing;<br />
with payment processing operations run out of a bank FIG. 17). 63 Additionally, commercial-scale counterfeiters<br />
in Azerbaijan, with bulk products shipped from India<br />
exploit social media platforms to generate web traffic<br />
or China, transiting through Hong Kong, Page then 20 sent<br />
and to direct consumers to rogue GAO-13-560 e-commerce Internet websites Pharmacies<br />
by air to the United Arab Emirates, passing through<br />
selling illicit goods. They do so in a variety of ways,<br />
London Heathrow airport, and with counterfeit inventory including by utilizing “buy-now”-type buttons that enable<br />
to be finished (packaged) in the Bahamas, before<br />
purchases directly from page posts and ads; and by<br />
being delivered to a customer in the United States<br />
posting pseudonymous product reviews, blog entries,<br />
or elsewhere. 62<br />
and fabricated social media profiles to create an aura of<br />
legitimacy around their website. 64<br />
30