salesforce_security_impl_guide
salesforce_security_impl_guide
salesforce_security_impl_guide
Create successful ePaper yourself
Turn your PDF publications into a flip-book with our unique Google optimized e-Paper software.
Securing and Sharing Data<br />
Revoking Permissions and Access<br />
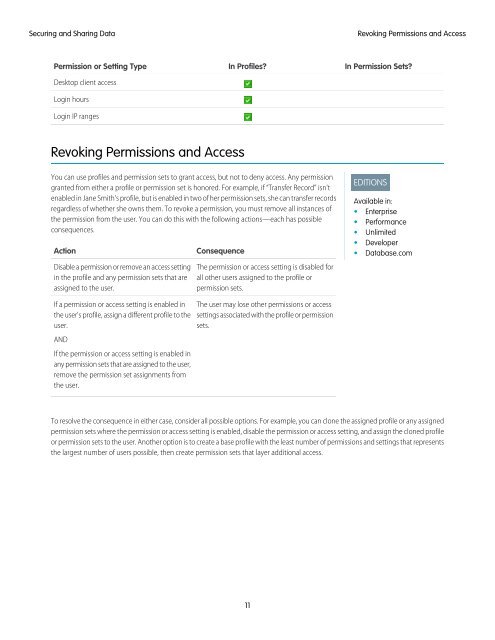
Permission or Setting Type<br />
Desktop client access<br />
Login hours<br />
Login IP ranges<br />
In Profiles<br />
In Permission Sets<br />
Revoking Permissions and Access<br />
You can use profiles and permission sets to grant access, but not to deny access. Any permission<br />
granted from either a profile or permission set is honored. For example, if “Transfer Record” isn't<br />
enabled in Jane Smith's profile, but is enabled in two of her permission sets, she can transfer records<br />
regardless of whether she owns them. To revoke a permission, you must remove all instances of<br />
the permission from the user. You can do this with the following actions—each has possible<br />
consequences.<br />
Action<br />
Disable a permission or remove an access setting<br />
in the profile and any permission sets that are<br />
assigned to the user.<br />
Consequence<br />
The permission or access setting is disabled for<br />
all other users assigned to the profile or<br />
permission sets.<br />
EDITIONS<br />
Available in:<br />
• Enterprise<br />
• Performance<br />
• Unlimited<br />
• Developer<br />
• Database.com<br />
If a permission or access setting is enabled in<br />
the user's profile, assign a different profile to the<br />
user.<br />
AND<br />
If the permission or access setting is enabled in<br />
any permission sets that are assigned to the user,<br />
remove the permission set assignments from<br />
the user.<br />
The user may lose other permissions or access<br />
settings associated with the profile or permission<br />
sets.<br />
To resolve the consequence in either case, consider all possible options. For example, you can clone the assigned profile or any assigned<br />
permission sets where the permission or access setting is enabled, disable the permission or access setting, and assign the cloned profile<br />
or permission sets to the user. Another option is to create a base profile with the least number of permissions and settings that represents<br />
the largest number of users possible, then create permission sets that layer additional access.<br />
11