CSP Gateway Configuration Guide - InterSystems Documentation
CSP Gateway Configuration Guide - InterSystems Documentation
CSP Gateway Configuration Guide - InterSystems Documentation
You also want an ePaper? Increase the reach of your titles
YUMPU automatically turns print PDFs into web optimized ePapers that Google loves.
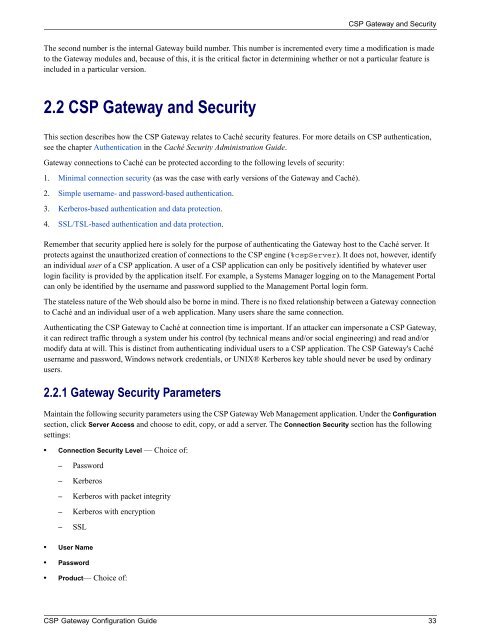
<strong>CSP</strong> <strong>Gateway</strong> and Security<br />
The second number is the internal <strong>Gateway</strong> build number. This number is incremented every time a modification is made<br />
to the <strong>Gateway</strong> modules and, because of this, it is the critical factor in determining whether or not a particular feature is<br />
included in a particular version.<br />
2.2 <strong>CSP</strong> <strong>Gateway</strong> and Security<br />
This section describes how the <strong>CSP</strong> <strong>Gateway</strong> relates to Caché security features. For more details on <strong>CSP</strong> authentication,<br />
see the chapter Authentication in the Caché Security Administration <strong>Guide</strong>.<br />
<strong>Gateway</strong> connections to Caché can be protected according to the following levels of security:<br />
1. Minimal connection security (as was the case with early versions of the <strong>Gateway</strong> and Caché).<br />
2. Simple username- and password-based authentication.<br />
3. Kerberos-based authentication and data protection.<br />
4. SSL/TSL-based authentication and data protection.<br />
Remember that security applied here is solely for the purpose of authenticating the <strong>Gateway</strong> host to the Caché server. It<br />
protects against the unauthorized creation of connections to the <strong>CSP</strong> engine (%cspServer). It does not, however, identify<br />
an individual user of a <strong>CSP</strong> application. A user of a <strong>CSP</strong> application can only be positively identified by whatever user<br />
login facility is provided by the application itself. For example, a Systems Manager logging on to the Management Portal<br />
can only be identified by the username and password supplied to the Management Portal login form.<br />
The stateless nature of the Web should also be borne in mind. There is no fixed relationship between a <strong>Gateway</strong> connection<br />
to Caché and an individual user of a web application. Many users share the same connection.<br />
Authenticating the <strong>CSP</strong> <strong>Gateway</strong> to Caché at connection time is important. If an attacker can impersonate a <strong>CSP</strong> <strong>Gateway</strong>,<br />
it can redirect traffic through a system under his control (by technical means and/or social engineering) and read and/or<br />
modify data at will. This is distinct from authenticating individual users to a <strong>CSP</strong> application. The <strong>CSP</strong> <strong>Gateway</strong>'s Caché<br />
username and password, Windows network credentials, or UNIX® Kerberos key table should never be used by ordinary<br />
users.<br />
2.2.1 <strong>Gateway</strong> Security Parameters<br />
Maintain the following security parameters using the <strong>CSP</strong> <strong>Gateway</strong> Web Management application. Under the <strong>Configuration</strong><br />
section, click Server Access and choose to edit, copy, or add a server. The Connection Security section has the following<br />
settings:<br />
• Connection Security Level — Choice of:<br />
– Password<br />
– Kerberos<br />
– Kerberos with packet integrity<br />
– Kerberos with encryption<br />
– SSL<br />
• User Name<br />
• Password<br />
• Product— Choice of:<br />
<strong>CSP</strong> <strong>Gateway</strong> <strong>Configuration</strong> <strong>Guide</strong> 33