Hacking_and_Penetration_Testing_with_Low_Power_Devices
Create successful ePaper yourself
Turn your PDF publications into a flip-book with our unique Google optimized e-Paper software.
146 CHAPTER 6 Input <strong>and</strong> output devices<br />
# is this a (802.11) packet, in particular a beacon frame<br />
if pkt.haslayer(Dot11) :<br />
pkt_list.append(pkt)<br />
# is this a client that I used to know?<br />
if pkt.addr2 not in client_list :<br />
client_list.append(pkt.addr2)<br />
print "Client: " + str(pkt.addr2) + " detected"<br />
def main() :<br />
# parse comm<strong>and</strong> line options<br />
parser ¼ optparse.OptionParser(’usage %prog -b -e\<br />
’)<br />
parser.add_option(’-b’, dest¼’bssid’, type¼’string’,\<br />
help¼’target BSSID’)<br />
parser.add_option(’-e’, dest¼’essid’, type¼’string’,\<br />
help¼’target ESSID’)<br />
(options, args) ¼ parser.parse_args()<br />
bssid ¼ options.bssid<br />
essid ¼ options.essid<br />
# if essid <strong>and</strong> bssid aren’t specified exit<br />
if (essid ¼¼ None ) j (bssid ¼¼ None):<br />
print parser.usage<br />
exit(0)<br />
print "Capturing traffic for ESSID:%s BSSID:%s" % (essid, bssid)<br />
sniff(iface¼"mon0", prn¼packet_h<strong>and</strong>ler, timeout¼60)<br />
pktcap ¼ PcapWriter(essid + ’.pcap’, append¼True, sync¼True)<br />
pktcap.write(pkt_list)<br />
pktcap.close()<br />
print "All done"<br />
exit(0)<br />
if __name__ ¼¼ ’__main__’ :<br />
main()<br />
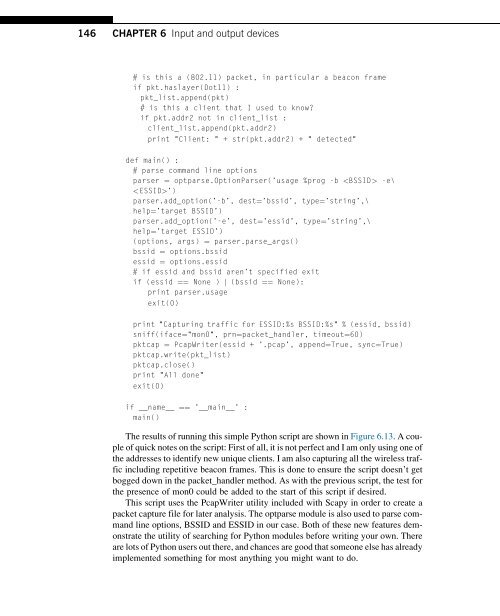
The results of running this simple Python script are shown in Figure 6.13. A couple<br />
of quick notes on the script: First of all, it is not perfect <strong>and</strong> I am only using one of<br />
the addresses to identify new unique clients. I am also capturing all the wireless traffic<br />
including repetitive beacon frames. This is done to ensure the script doesn’t get<br />
bogged down in the packet_h<strong>and</strong>ler method. As <strong>with</strong> the previous script, the test for<br />
the presence of mon0 could be added to the start of this script if desired.<br />
This script uses the PcapWriter utility included <strong>with</strong> Scapy in order to create a<br />
packet capture file for later analysis. The optparse module is also used to parse comm<strong>and</strong><br />
line options, BSSID <strong>and</strong> ESSID in our case. Both of these new features demonstrate<br />
the utility of searching for Python modules before writing your own. There<br />
are lots of Python users out there, <strong>and</strong> chances are good that someone else has already<br />
implemented something for most anything you might want to do.