Hacking_and_Penetration_Testing_with_Low_Power_Devices
Create successful ePaper yourself
Turn your PDF publications into a flip-book with our unique Google optimized e-Paper software.
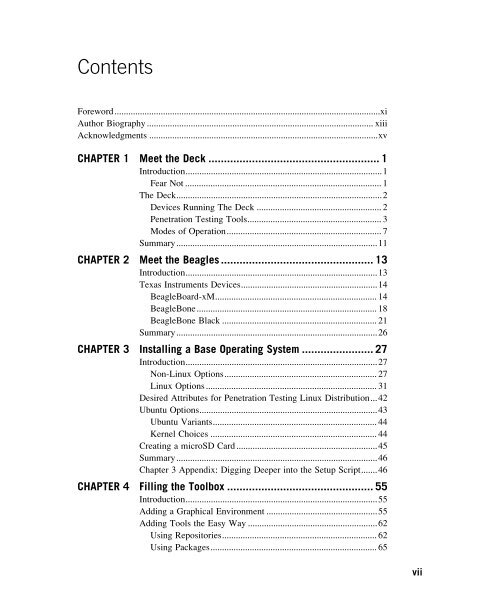
Contents<br />
Foreword...................................................................................................................xi<br />
Author Biography .................................................................................................. xiii<br />
Acknowledgments ...................................................................................................xv<br />
CHAPTER 1 Meet the Deck ....................................................... 1<br />
Introduction.....................................................................................1<br />
Fear Not ..................................................................................... 1<br />
The Deck.........................................................................................2<br />
<strong>Devices</strong> Running The Deck ...................................................... 2<br />
<strong>Penetration</strong> <strong>Testing</strong> Tools.......................................................... 3<br />
Modes of Operation................................................................... 7<br />
Summary.......................................................................................11<br />
CHAPTER 2 Meet the Beagles ................................................. 13<br />
Introduction...................................................................................13<br />
Texas Instruments <strong>Devices</strong>...........................................................14<br />
BeagleBoard-xM...................................................................... 14<br />
BeagleBone.............................................................................. 18<br />
BeagleBone Black ................................................................... 21<br />
Summary.......................................................................................26<br />
CHAPTER 3 Installing a Base Operating System ....................... 27<br />
Introduction...................................................................................27<br />
Non-Linux Options.................................................................. 27<br />
Linux Options .......................................................................... 31<br />
Desired Attributes for <strong>Penetration</strong> <strong>Testing</strong> Linux Distribution...42<br />
Ubuntu Options.............................................................................43<br />
Ubuntu Variants....................................................................... 44<br />
Kernel Choices ........................................................................ 44<br />
Creating a microSD Card .............................................................45<br />
Summary.......................................................................................46<br />
Chapter 3 Appendix: Digging Deeper into the Setup Script.......46<br />
CHAPTER 4 Filling the Toolbox ............................................... 55<br />
Introduction...................................................................................55<br />
Adding a Graphical Environment ................................................55<br />
Adding Tools the Easy Way ........................................................62<br />
Using Repositories................................................................... 62<br />
Using Packages........................................................................ 65<br />
vii