Index Note: Page numbers followed by f indicate figures <strong>and</strong> t indicate tables. A Aerial hacking drone quadcopters, 224 I2C, 234 IMU, 234 Phantom, 233 vs. QuadShot, 234 SPI, 234 QuadShot advantages, 224 Alfa adapter, 228, 228f BeagleBone installation, 227–228, 227f Cappuccino, 224–225, 225f disadvantages, 227 Latte, 224–225 LIA controller board, 228, 229 Mocha, 224–225, 225f power conservation, 230–233 vs. quadcopters, 234 router-only operation, 229–230 Xbee adapter <strong>and</strong> cape, 229, 229f Xbee serial interface board, 226–227, 226f selection factors, 223, 224 Aircrack-ng, 195, 196f Alfa wireless adapter, 7–8, 95 American wire gauge (AWG), 98, 98t Analogue to digital converters (ADCs), 20–21 Arch Linux, 34–35, 34t, 35f Army secret drones installation equipment removal, 222 initial hiding, 220–221 maintenance, 222 wired drone, 216, 219f wireless battery-powered drone, 216, 219f wireless USB-powered drone, 216, 220f hacking drones hiding artificial plants, 209–211 audio visual control panel, 209–211, 212f building roofs, 207, 208f Buzz Lightyear, 216, 218f car drone, 208, 209f Dalek Desk Defender toy, 214, 216f, 217f desks, 208–209, 210f drop ceilings, 209, 211f fake nest, 206–207, 207f floor panel, 209–211, 212f h<strong>and</strong> sanitizer dispenser, 209–211, 214f haxtar, 216, 219f network printer, 209–211, 213f phone st<strong>and</strong>, 209–211, 213f plants, 209–211, 215f rocks, 207 snow-covered bush, 206–207, 206f storage closets, 209 table, 209–211, 215f TARDIS toy, 214, 217f wall-mounted televisions, 209–211 Attack planning, 191–192 ATMega328P microcontroller, 237 AWG. See American wire gauge (AWG) B Basic service set identification (BSSID), 108 Battery power Duracell batteries, 99–100, 101, 101t NiMH batteries, 101, 101t power supply heat sink, 99, 100f prototyping board, 99, 100f 7805 voltage regulator, 99, 99f TO-220 package, 99 BeagleBoard.org Foundation, 2 Beagle-Board Web site, 2–3 BeagleBoard-xM, 7, 7f above view, 14, 15f vs. BeagleBone Black, 26, 26t below view, 14, 15f custom-etched enclosure, 17, 17f DB9 RS-232 serial port, 17 DM3730 processor, 14 DVI-D connection, 16 HDMI connector, 16 integrated Fast Ethernet port, 17 JTAG connector, 17 LCD screen, 16 LEDs, 16–17 microSD card slot, 16 NEON SIMD coprocessor, 14 package on package design, 14 S-Video connection, 16 TPS65950 chip, 16 USB 2.0 host ports, 16 Windows CE, 27–28 239
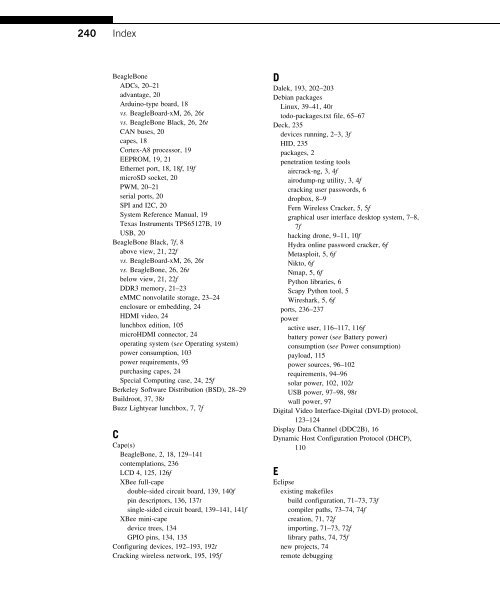
240 Index BeagleBone ADCs, 20–21 advantage, 20 Arduino-type board, 18 vs. BeagleBoard-xM, 26, 26t vs. BeagleBone Black, 26, 26t CAN buses, 20 capes, 18 Cortex-A8 processor, 19 EEPROM, 19, 21 Ethernet port, 18, 18f, 19f microSD socket, 20 PWM, 20–21 serial ports, 20 SPI <strong>and</strong> I2C, 20 System Reference Manual, 19 Texas Instruments TPS65127B, 19 USB, 20 BeagleBone Black, 7f, 8 above view, 21, 22f vs. BeagleBoard-xM, 26, 26t vs. BeagleBone, 26, 26t below view, 21, 22f DDR3 memory, 21–23 eMMC nonvolatile storage, 23–24 enclosure or embedding, 24 HDMI video, 24 lunchbox edition, 105 microHDMI connector, 24 operating system (see Operating system) power consumption, 103 power requirements, 95 purchasing capes, 24 Special Computing case, 24, 25f Berkeley Software Distribution (BSD), 28–29 Buildroot, 37, 38t Buzz Lightyear lunchbox, 7, 7f C Cape(s) BeagleBone, 2, 18, 129–141 contemplations, 236 LCD 4, 125, 126f XBee full-cape double-sided circuit board, 139, 140f pin descriptors, 136, 137t single-sided circuit board, 139–141, 141f XBee mini-cape device trees, 134 GPIO pins, 134, 135 Configuring devices, 192–193, 192t Cracking wireless network, 195, 195f D Dalek, 193, 202–203 Debian packages Linux, 39–41, 40t todo-packages.txt file, 65–67 Deck, 235 devices running, 2–3, 3f HID, 235 packages, 2 penetration testing tools aircrack-ng, 3, 4f airodump-ng utility, 3, 4f cracking user passwords, 6 dropbox, 8–9 Fern Wireless Cracker, 5, 5f graphical user interface desktop system, 7–8, 7f hacking drone, 9–11, 10f Hydra online password cracker, 6f Metasploit, 5, 6f Nikto, 6f Nmap, 5, 6f Python libraries, 6 Scapy Python tool, 5 Wireshark, 5, 6f ports, 236–237 power active user, 116–117, 116f battery power (see Battery power) consumption (see <strong>Power</strong> consumption) payload, 115 power sources, 96–102 requirements, 94–96 solar power, 102, 102t USB power, 97–98, 98t wall power, 97 Digital Video Interface-Digital (DVI-D) protocol, 123–124 Display Data Channel (DDC2B), 16 Dynamic Host Configuration Protocol (DHCP), 110 E Eclipse existing makefiles build configuration, 71–73, 73f compiler paths, 73–74, 74f creation, 71, 72f importing, 71–73, 72f library paths, 74, 75f new projects, 74 remote debugging
- Page 2 and 3:
Hacking and Penetration Testing wit
- Page 4 and 5:
Hacking and Penetration Testing wit
- Page 6 and 7:
Dedicated to my favorite wife, my f
- Page 8 and 9:
Contents Foreword..................
- Page 10 and 11:
Contents ix Network Hubs and Switch
- Page 12 and 13:
Foreword So I will start out this f
- Page 14 and 15:
Author Biography Dr. Philip Polstra
- Page 16 and 17:
Acknowledgments First and foremost,
- Page 18 and 19:
CHAPTER Meet the deck 1 INFORMATION
- Page 20 and 21:
The deck 3 FIGURE 1.1 Collection of
- Page 22 and 23:
The deck 5 FIGURE 1.4 Fern WiFi Cra
- Page 24 and 25:
The deck 7 MODES OF OPERATION One o
- Page 26 and 27:
The deck 9 stores data only on a lo
- Page 28 and 29:
Summary 11 I knew that The Deck, wh
- Page 30 and 31:
CHAPTER Meet the beagles 2 INFORMAT
- Page 32 and 33:
Texas instruments devices 15 FIGURE
- Page 34 and 35:
Texas instruments devices 17 proces
- Page 36 and 37:
Texas instruments devices 19 FIGURE
- Page 38 and 39:
Texas instruments devices 21 The AD
- Page 40 and 41:
Texas instruments devices 23 WHY NO
- Page 42 and 43:
Texas instruments devices 25 FIGURE
- Page 44 and 45:
CHAPTER Installing a base operating
- Page 46 and 47:
Introduction 29 FIGURE 3.2 QNX smar
- Page 48 and 49:
Introduction 31 FIGURE 3.4 Android
- Page 50 and 51:
Introduction 33 (http://openembedde
- Page 52 and 53:
Introduction 35 FIGURE 3.6 Arch Lin
- Page 54 and 55:
Introduction 37 Sabayon In the phys
- Page 56 and 57:
Introduction 39 Table 3.7 Fedora Pe
- Page 58 and 59:
Introduction 41 tar xJf debian*.xz
- Page 60 and 61:
Ubuntu options 43 supportive commun
- Page 62 and 63:
Creating a microSD Card 45 Device t
- Page 64 and 65:
Chapter 3 Appendix: digging deeper
- Page 66 and 67:
Chapter 3 Appendix: digging deeper
- Page 68 and 69:
Chapter 3 Appendix: digging deeper
- Page 70 and 71:
Chapter 3 Appendix: digging deeper
- Page 72 and 73:
CHAPTER Filling the toolbox 4 INFOR
- Page 74 and 75:
Adding a graphical environment 57 b
- Page 76 and 77:
Adding a graphical environment 59 W
- Page 78 and 79:
Adding a graphical environment 61 t
- Page 80 and 81:
Adding tools the easy way 63 The li
- Page 82 and 83:
Adding tools the easy way 65 check_
- Page 84 and 85:
Adding tools the easy way 67 echo -
- Page 86 and 87:
Adding tools the hard way 69 # chec
- Page 88 and 89:
Adding tools the hard way 71 descri
- Page 90 and 91:
Adding tools the hard way 73 FIGURE
- Page 92 and 93:
Adding tools the hard way 75 FIGURE
- Page 94 and 95:
Adding tools the hard way 77 FIGURE
- Page 96 and 97:
Adding tools the hard way 79 FIGURE
- Page 98 and 99:
Adding tools the hard way 81 FIGURE
- Page 100 and 101:
Adding tools the hard way 83 FIGURE
- Page 102 and 103:
Adding tools the hard way 85 dl_src
- Page 104 and 105:
Starter set of tools 87 and possibl
- Page 106 and 107:
Starter set of tools 89 #get John w
- Page 108 and 109:
Starter set of tools 91 The company
- Page 110 and 111:
CHAPTER Powering The Deck 5 INFORMA
- Page 112 and 113:
Power requirements 95 the city and
- Page 114 and 115:
Power sources 97 WALL POWER When it
- Page 116 and 117:
Power sources 99 Thanks to commonly
- Page 118 and 119:
Power sources 101 Table 5.2 Duracel
- Page 120 and 121:
Reducing power consumption 103 REDU
- Page 122 and 123:
Penetration testing with a single b
- Page 124 and 125:
Penetration testing with a single b
- Page 126 and 127:
Penetration testing with a single b
- Page 128 and 129:
Penetration testing with a single b
- Page 130 and 131:
Penetration testing with a single b
- Page 132 and 133:
Penetration testing with a single b
- Page 134 and 135:
Penetration testing with a single b
- Page 136 and 137:
Penetration testing with a single b
- Page 138 and 139:
Summary 121 site. In-depth testing
- Page 140 and 141:
CHAPTER Input and output devices 6
- Page 142 and 143:
Display options 125 FIGURE 6.1 LCD7
- Page 144 and 145:
IEEE 802.11 wireless 127 The Alfa A
- Page 146 and 147:
BeagleBone capes 129 FIGURE 6.4 UAR
- Page 148 and 149:
BeagleBone capes 131 pull-up resist
- Page 150 and 151:
BeagleBone capes 133 FIGURE 6.7 XBe
- Page 152 and 153:
BeagleBone capes 135 Newly created
- Page 154 and 155:
BeagleBone capes 137 Table 6.1 Cape
- Page 156 and 157:
BeagleBone capes 139 If you don’t
- Page 158 and 159:
Penetration testing with a single r
- Page 160 and 161:
Penetration testing with a single r
- Page 162 and 163:
Penetration testing with a single r
- Page 164 and 165:
Penetration testing with a single r
- Page 166 and 167:
Penetration testing with a single r
- Page 168 and 169:
Penetration testing with a single r
- Page 170 and 171:
Summary 153 if "done" in status.ite
- Page 172 and 173:
CHAPTER Building an army of devices
- Page 174 and 175:
Using IEEE 802.15.4 networking 157
- Page 176 and 177:
Configuring IEEE 802.15.4 modems 15
- Page 178 and 179:
Configuring IEEE 802.15.4 modems 16
- Page 180 and 181:
Configuring IEEE 802.15.4 modems 16
- Page 182 and 183:
Configuring IEEE 802.15.4 modems 16
- Page 184 and 185:
Remote control the easy way 167 FIG
- Page 186 and 187:
Remote control via python 169 seria
- Page 188 and 189:
Remote control via python 171 impor
- Page 190 and 191:
Remote control via python 173 elif
- Page 192 and 193:
Remote control via python 175 dnum
- Page 194 and 195:
Remote control via python 177 rc_na
- Page 196 and 197:
Remote control via python 179 The M
- Page 198 and 199:
Remote control via python 181 } [ "
- Page 200 and 201:
Remote control via python 183 Merel
- Page 202 and 203:
Saving power 185 on the modem. The
- Page 204 and 205:
Adding security 187 a different cha
- Page 206 and 207: Expanding Your Reach 189 FIGURE 7.1
- Page 208 and 209: Penetration testing with multiple d
- Page 210 and 211: Penetration testing with multiple d
- Page 212 and 213: Penetration testing with multiple d
- Page 214 and 215: Penetration testing with multiple d
- Page 216 and 217: Penetration testing with multiple d
- Page 218 and 219: Penetration testing with multiple d
- Page 220 and 221: Summary 203 # if IP and MAC aren’
- Page 222 and 223: CHAPTER Keeping your army secret 8
- Page 224 and 225: Hiding devices 207 FIGURE 8.2 At fi
- Page 226 and 227: Hiding devices 209 FIGURE 8.4 Car d
- Page 228 and 229: Hiding devices 211 FIGURE 8.7 Wirel
- Page 230 and 231: Hiding devices 213 FIGURE 8.11 Unde
- Page 232 and 233: Hiding devices 215 FIGURE 8.14 Unde
- Page 234 and 235: FIGURE 8.17 Inside the Dalek Desk D
- Page 236 and 237: FIGURE 8.21 The haxtar. The haxtar
- Page 238 and 239: Installing devices 221 example, wea
- Page 240 and 241: CHAPTER Adding air support 9 INFORM
- Page 242 and 243: Building the AirDeck 225 Latte is s
- Page 244 and 245: Building the AirDeck 227 what you a
- Page 246 and 247: Using your aerial drone 229 Power i
- Page 248 and 249: Using your aerial drone 231 Install
- Page 250 and 251: Alternative aircraft 233 else { //
- Page 252 and 253: CHAPTER Future directions 10 INFORM
- Page 254 and 255: Closing thoughts 237 For reasons me
- Page 258 and 259: Index 241 configuration, 77-79, 83f
- Page 260: Index 243 Python scripts, 143-144 w