Hacking_and_Penetration_Testing_with_Low_Power_Devices
Create successful ePaper yourself
Turn your PDF publications into a flip-book with our unique Google optimized e-Paper software.
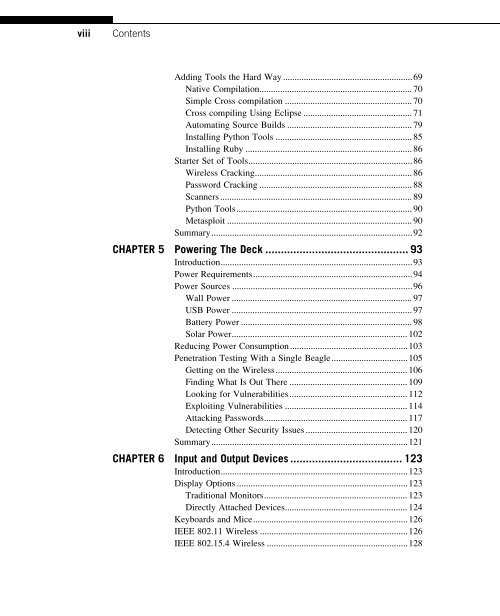
viii<br />
Contents<br />
Adding Tools the Hard Way ........................................................69<br />
Native Compilation.................................................................. 70<br />
Simple Cross compilation ....................................................... 70<br />
Cross compiling Using Eclipse ............................................... 71<br />
Automating Source Builds ...................................................... 79<br />
Installing Python Tools ........................................................... 85<br />
Installing Ruby ........................................................................ 86<br />
Starter Set of Tools.......................................................................86<br />
Wireless Cracking.................................................................... 86<br />
Password Cracking .................................................................. 88<br />
Scanners ................................................................................... 89<br />
Python Tools............................................................................ 90<br />
Metasploit ................................................................................ 90<br />
Summary.......................................................................................92<br />
CHAPTER 5 <strong>Power</strong>ing The Deck .............................................. 93<br />
Introduction...................................................................................93<br />
<strong>Power</strong> Requirements.....................................................................94<br />
<strong>Power</strong> Sources ..............................................................................96<br />
Wall <strong>Power</strong> .............................................................................. 97<br />
USB <strong>Power</strong> .............................................................................. 97<br />
Battery <strong>Power</strong> .......................................................................... 98<br />
Solar <strong>Power</strong>............................................................................ 102<br />
Reducing <strong>Power</strong> Consumption...................................................103<br />
<strong>Penetration</strong> <strong>Testing</strong> With a Single Beagle.................................105<br />
Getting on the Wireless......................................................... 106<br />
Finding What Is Out There ................................................... 109<br />
Looking for Vulnerabilities................................................... 112<br />
Exploiting Vulnerabilities ..................................................... 114<br />
Attacking Passwords.............................................................. 117<br />
Detecting Other Security Issues ............................................ 120<br />
Summary.....................................................................................121<br />
CHAPTER 6 Input <strong>and</strong> Output <strong>Devices</strong> .................................... 123<br />
Introduction.................................................................................123<br />
Display Options ..........................................................................123<br />
Traditional Monitors.............................................................. 123<br />
Directly Attached <strong>Devices</strong>..................................................... 124<br />
Keyboards <strong>and</strong> Mice...................................................................126<br />
IEEE 802.11 Wireless ................................................................126<br />
IEEE 802.15.4 Wireless .............................................................128