Installation Guide - Eset
Installation Guide - Eset
Installation Guide - Eset
Create successful ePaper yourself
Turn your PDF publications into a flip-book with our unique Google optimized e-Paper software.
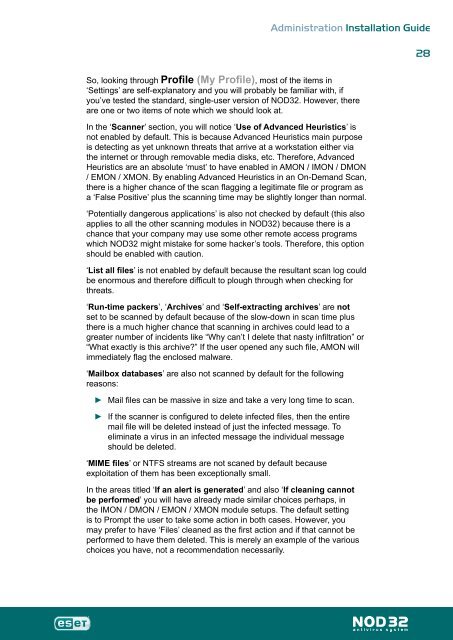
Administration <strong>Installation</strong> <strong>Guide</strong><br />
So, looking through Profile (My Profile), most of the items in<br />
‘Settings’ are self-explanatory and you will probably be familiar with, if<br />
you’ve tested the standard, single-user version of NOD32. However, there<br />
are one or two items of note which we should look at.<br />
In the ‘Scanner’ section, you will notice ‘Use of Advanced Heuristics’ is<br />
not enabled by default. This is because Advanced Heuristics main purpose<br />
is detecting as yet unknown threats that arrive at a workstation either via<br />
the internet or through removable media disks, etc. Therefore, Advanced<br />
Heuristics are an absolute ‘must’ to have enabled in AMON / IMON / DMON<br />
/ EMON / XMON. By enabling Advanced Heuristics in an On-Demand Scan,<br />
there is a higher chance of the scan flagging a legitimate file or program as<br />
a ‘False Positive’ plus the scanning time may be slightly longer than normal.<br />
‘Potentially dangerous applications’ is also not checked by default (this also<br />
applies to all the other scanning modules in NOD32) because there is a<br />
chance that your company may use some other remote access programs<br />
which NOD32 might mistake for some hacker’s tools. Therefore, this option<br />
should be enabled with caution.<br />
‘List all files’ is not enabled by default because the resultant scan log could<br />
be enormous and therefore difficult to plough through when checking for<br />
threats.<br />
‘Run-time packers’, ‘Archives’ and ‘Self-extracting archives’ are not<br />
set to be scanned by default because of the slow-down in scan time plus<br />
there is a much higher chance that scanning in archives could lead to a<br />
greater number of incidents like “Why can’t I delete that nasty infiltration” or<br />
“What exactly is this archive?” If the user opened any such file, AMON will<br />
immediately flag the enclosed malware.<br />
‘Mailbox databases’ are also not scanned by default for the following<br />
reasons:<br />
►<br />
►<br />
Mail files can be massive in size and take a very long time to scan.<br />
If the scanner is configured to delete infected files, then the entire<br />
mail file will be deleted instead of just the infected message. To<br />
eliminate a virus in an infected message the individual message<br />
should be deleted.<br />
‘MIME files’ or NTFS streams are not scaned by default because<br />
exploitation of them has been exceptionally small.<br />
In the areas titled ‘If an alert is generated’ and also ‘If cleaning cannot<br />
be performed’ you will have already made similar choices perhaps, in<br />
the IMON / DMON / EMON / XMON module setups. The default setting<br />
is to Prompt the user to take some action in both cases. However, you<br />
may prefer to have ‘Files’ cleaned as the first action and if that cannot be<br />
performed to have them deleted. This is merely an example of the various<br />
choices you have, not a recommendation necessarily.<br />
8