Analysis and Evaluation of the Windows Event Log - Bill Buchanan
Analysis and Evaluation of the Windows Event Log - Bill Buchanan
Analysis and Evaluation of the Windows Event Log - Bill Buchanan
You also want an ePaper? Increase the reach of your titles
YUMPU automatically turns print PDFs into web optimized ePapers that Google loves.
Barrie Codona, BSc (Hons) Network Computing, 2007<br />
………………<br />
………………<br />
……………………<br />
………………<br />
……………………<br />
…………………<br />
Figure 11: Server XML string<br />
4.5 <strong>Event</strong> Viewer<br />
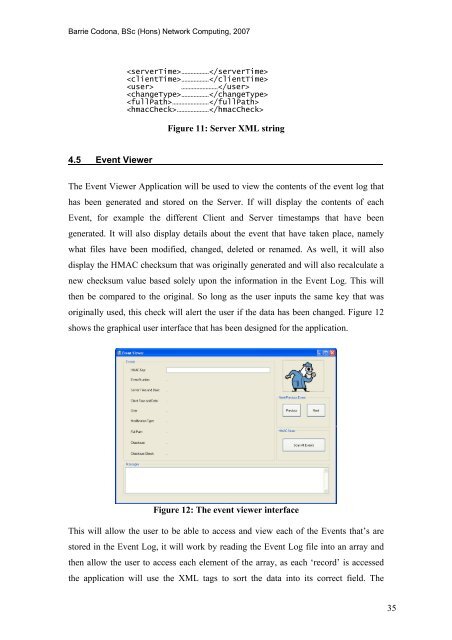
The <strong>Event</strong> Viewer Application will be used to view <strong>the</strong> contents <strong>of</strong> <strong>the</strong> event log that<br />
has been generated <strong>and</strong> stored on <strong>the</strong> Server. If will display <strong>the</strong> contents <strong>of</strong> each<br />
<strong>Event</strong>, for example <strong>the</strong> different Client <strong>and</strong> Server timestamps that have been<br />
generated. It will also display details about <strong>the</strong> event that have taken place, namely<br />
what files have been modified, changed, deleted or renamed. As well, it will also<br />
display <strong>the</strong> HMAC checksum that was originally generated <strong>and</strong> will also recalculate a<br />
new checksum value based solely upon <strong>the</strong> information in <strong>the</strong> <strong>Event</strong> <strong>Log</strong>. This will<br />
<strong>the</strong>n be compared to <strong>the</strong> original. So long as <strong>the</strong> user inputs <strong>the</strong> same key that was<br />
originally used, this check will alert <strong>the</strong> user if <strong>the</strong> data has been changed. Figure 12<br />
shows <strong>the</strong> graphical user interface that has been designed for <strong>the</strong> application.<br />
Figure 12: The event viewer interface<br />
This will allow <strong>the</strong> user to be able to access <strong>and</strong> view each <strong>of</strong> <strong>the</strong> <strong>Event</strong>s that’s are<br />
stored in <strong>the</strong> <strong>Event</strong> <strong>Log</strong>, it will work by reading <strong>the</strong> <strong>Event</strong> <strong>Log</strong> file into an array <strong>and</strong><br />
<strong>the</strong>n allow <strong>the</strong> user to access each element <strong>of</strong> <strong>the</strong> array, as each ‘record’ is accessed<br />
<strong>the</strong> application will use <strong>the</strong> XML tags to sort <strong>the</strong> data into its correct field. The<br />
35









![Unit 5. Switches and VLANs [PDF]](https://img.yumpu.com/34422504/1/184x260/unit-5-switches-and-vlans-pdf.jpg?quality=85)





