Analysis and Evaluation of the Windows Event Log - Bill Buchanan
Analysis and Evaluation of the Windows Event Log - Bill Buchanan
Analysis and Evaluation of the Windows Event Log - Bill Buchanan
Create successful ePaper yourself
Turn your PDF publications into a flip-book with our unique Google optimized e-Paper software.
Barrie Codona, BSc (Hons) Network Computing, 2007<br />
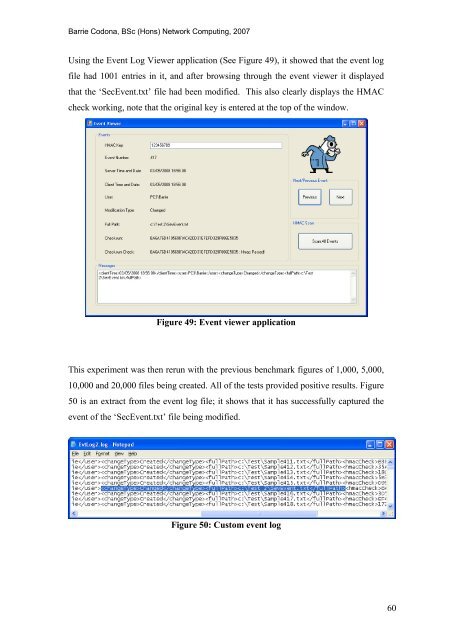
Using <strong>the</strong> <strong>Event</strong> <strong>Log</strong> Viewer application (See Figure 49), it showed that <strong>the</strong> event log<br />
file had 1001 entries in it, <strong>and</strong> after browsing through <strong>the</strong> event viewer it displayed<br />
that <strong>the</strong> ‘Sec<strong>Event</strong>.txt’ file had been modified. This also clearly displays <strong>the</strong> HMAC<br />
check working, note that <strong>the</strong> original key is entered at <strong>the</strong> top <strong>of</strong> <strong>the</strong> window.<br />
Figure 49: <strong>Event</strong> viewer application<br />
This experiment was <strong>the</strong>n rerun with <strong>the</strong> previous benchmark figures <strong>of</strong> 1,000, 5,000,<br />
10,000 <strong>and</strong> 20,000 files being created. All <strong>of</strong> <strong>the</strong> tests provided positive results. Figure<br />
50 is an extract from <strong>the</strong> event log file; it shows that it has successfully captured <strong>the</strong><br />
event <strong>of</strong> <strong>the</strong> ‘Sec<strong>Event</strong>.txt’ file being modified.<br />
Figure 50: Custom event log<br />
60









![Unit 5. Switches and VLANs [PDF]](https://img.yumpu.com/34422504/1/184x260/unit-5-switches-and-vlans-pdf.jpg?quality=85)





