Analysis and Evaluation of the Windows Event Log - Bill Buchanan
Analysis and Evaluation of the Windows Event Log - Bill Buchanan
Analysis and Evaluation of the Windows Event Log - Bill Buchanan
Create successful ePaper yourself
Turn your PDF publications into a flip-book with our unique Google optimized e-Paper software.
Barrie Codona, BSc (Hons) Network Computing, 2007<br />
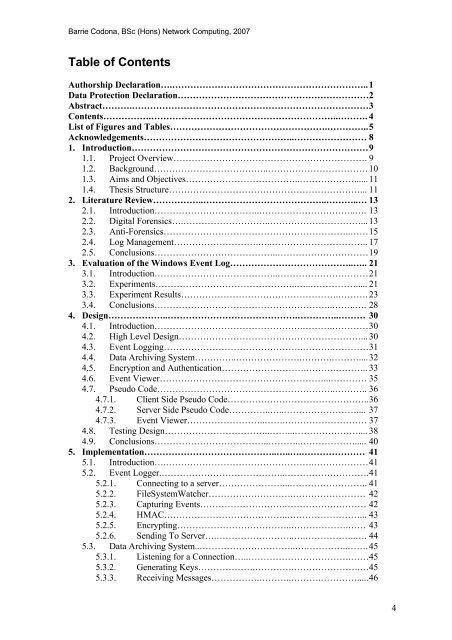
Table <strong>of</strong> Contents<br />
Authorship Declaration….……………………………………………………….. 1<br />
Data Protection Declaration……………………………………………………… 2<br />
Abstract……….…………………………………………………………………… 3<br />
Contents…………….……………………………………………………..………. 4<br />
List <strong>of</strong> Figures <strong>and</strong> Tables…………………………………………….………….. 5<br />
Acknowledgements…………………………………………..…………………… 8<br />
1. Introduction…………………………………………………………………… 9<br />
1.1. Project Overview………………………………………………………. 9<br />
1.2. Background………………………………..…………………………… 10<br />
1.3. Aims <strong>and</strong> Objectives………………………………..………………...... 11<br />
1.4. Thesis Structure………………………………………………………... 11<br />
2. Literature Review……………..…………………………………..………..… 13<br />
2.1. Introduction……………………………..…………………………..…. 13<br />
2.2. Digital Forensics….………………………..…………………………... 13<br />
2.3. Anti-Forensics……………………………………………………..…… 15<br />
2.4. <strong>Log</strong> Management……………………….…..………………………….. 17<br />
2.5. Conclusions…………………………………..………………………… 19<br />
3. <strong>Evaluation</strong> <strong>of</strong> <strong>the</strong> <strong>Windows</strong> <strong>Event</strong> <strong>Log</strong>…………………………………..….. 21<br />
3.1. Introduction…………………………………..………………………… 21<br />
3.2. Experiments………………………………………..…..……………..... 21<br />
3.3. Experiment Results…………………………………………….………. 23<br />
3.4. Conclusions…………………………………………………..……..…. 28<br />
4. Design………………..…………………………………….…………..……… 30<br />
4.1. Introduction………………………………………….……….………… 30<br />
4.2. High Level Design……………………………………………………... 30<br />
4.3. <strong>Event</strong> <strong>Log</strong>ging……………………………………….……….………… 31<br />
4.4. Data Archiving System…………..………………….……….……….... 32<br />
4.5. Encryption <strong>and</strong> Au<strong>the</strong>ntication……………………….……….……….. 33<br />
4.6. <strong>Event</strong> Viewer………………………………………………...………… 35<br />
4.7. Pseudo Code…………………………………………………..……….. 36<br />
4.7.1. Client Side Pseudo Code……………………………………….. 36<br />
4.7.2. Server Side Pseudo Code…………..…..…………………….... 37<br />
4.7.3. <strong>Event</strong> Viewer……………………..…….……………………… 37<br />
4.8. Testing Design……………………………..……...………………….... 38<br />
4.9. Conclusions………………………………..………..………………..... 40<br />
5. Implementation……………………………………..…..….………………… 41<br />
5.1. Introduction….………………………………………….……………… 41<br />
5.2. <strong>Event</strong> <strong>Log</strong>ger.…………………………………..………………………. 41<br />
5.2.1. Connecting to a server…………………...…………………….. 41<br />
5.2.2. FileSystemWatcher……………………….…………………… 42<br />
5.2.3. Capturing <strong>Event</strong>s……………………….……………………… 42<br />
5.2.4. HMAC…………………………………..……………………... 43<br />
5.2.5. Encrypting………………………………..……………….…… 43<br />
5.2.6. Sending To Server….……………………..….……………..…. 44<br />
5.3. Data Archiving System..…………………………..….…………..……. 45<br />
5.3.1. Listening for a Connection…..…………………………….…… 45<br />
5.3.2. Generating Keys……………….………….………………….… 45<br />
5.3.3. Receiving Messages…………….………..……….…………..... 46<br />
4









![Unit 5. Switches and VLANs [PDF]](https://img.yumpu.com/34422504/1/184x260/unit-5-switches-and-vlans-pdf.jpg?quality=85)





