Analysis and Evaluation of the Windows Event Log - Bill Buchanan
Analysis and Evaluation of the Windows Event Log - Bill Buchanan
Analysis and Evaluation of the Windows Event Log - Bill Buchanan
Create successful ePaper yourself
Turn your PDF publications into a flip-book with our unique Google optimized e-Paper software.
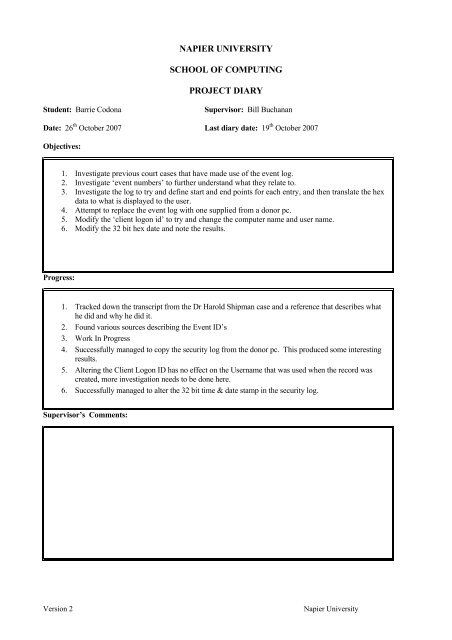
NAPIER UNIVERSITY<br />
SCHOOL OF COMPUTING<br />
PROJECT DIARY<br />
Student: Barrie Codona<br />
Supervisor: <strong>Bill</strong> <strong>Buchanan</strong><br />
Date: 26 th October 2007 Last diary date: 19 th October 2007<br />
Objectives:<br />
1. Investigate previous court cases that have made use <strong>of</strong> <strong>the</strong> event log.<br />
2. Investigate ‘event numbers’ to fur<strong>the</strong>r underst<strong>and</strong> what <strong>the</strong>y relate to.<br />
3. Investigate <strong>the</strong> log to try <strong>and</strong> define start <strong>and</strong> end points for each entry, <strong>and</strong> <strong>the</strong>n translate <strong>the</strong> hex<br />
data to what is displayed to <strong>the</strong> user.<br />
4. Attempt to replace <strong>the</strong> event log with one supplied from a donor pc.<br />
5. Modify <strong>the</strong> ‘client logon id’ to try <strong>and</strong> change <strong>the</strong> computer name <strong>and</strong> user name.<br />
6. Modify <strong>the</strong> 32 bit hex date <strong>and</strong> note <strong>the</strong> results.<br />
Progress:<br />
1. Tracked down <strong>the</strong> transcript from <strong>the</strong> Dr Harold Shipman case <strong>and</strong> a reference that describes what<br />
he did <strong>and</strong> why he did it.<br />
2. Found various sources describing <strong>the</strong> <strong>Event</strong> ID’s<br />
3. Work In Progress<br />
4. Successfully managed to copy <strong>the</strong> security log from <strong>the</strong> donor pc. This produced some interesting<br />
results.<br />
5. Altering <strong>the</strong> Client <strong>Log</strong>on ID has no effect on <strong>the</strong> Username that was used when <strong>the</strong> record was<br />
created, more investigation needs to be done here.<br />
6. Successfully managed to alter <strong>the</strong> 32 bit time & date stamp in <strong>the</strong> security log.<br />
Supervisor’s Comments:<br />
Version 2<br />
Napier University









![Unit 5. Switches and VLANs [PDF]](https://img.yumpu.com/34422504/1/184x260/unit-5-switches-and-vlans-pdf.jpg?quality=85)





