4.0
1NSchAb
1NSchAb
- No tags were found...
Create successful ePaper yourself
Turn your PDF publications into a flip-book with our unique Google optimized e-Paper software.
122<br />
Web Application Penetration Testing<br />
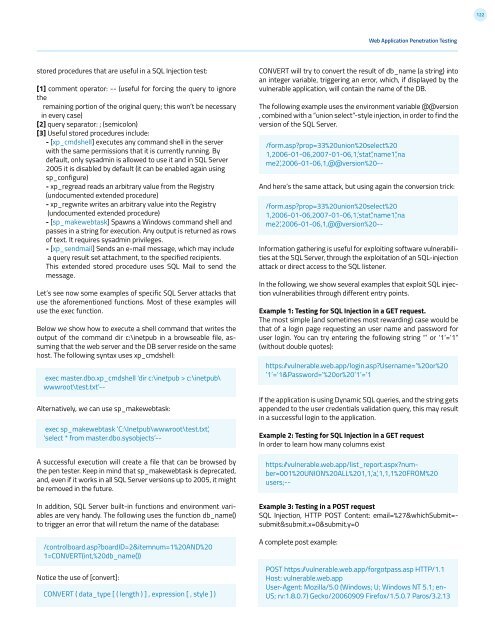
stored procedures that are useful in a SQL Injection test:<br />
[1] comment operator: -- (useful for forcing the query to ignore<br />
the<br />
remaining portion of the original query; this won’t be necessary<br />
in every case)<br />
[2] query separator: ; (semicolon)<br />
[3] Useful stored procedures include:<br />
- [xp_cmdshell] executes any command shell in the server<br />
with the same permissions that it is currently running. By<br />
default, only sysadmin is allowed to use it and in SQL Server<br />
2005 it is disabled by default (it can be enabled again using<br />
sp_configure)<br />
- xp_regread reads an arbitrary value from the Registry<br />
(undocumented extended procedure)<br />
- xp_regwrite writes an arbitrary value into the Registry<br />
(undocumented extended procedure)<br />
- [sp_makewebtask] Spawns a Windows command shell and<br />
passes in a string for execution. Any output is returned as rows<br />
of text. It requires sysadmin privileges.<br />
- [xp_sendmail] Sends an e-mail message, which may include<br />
a query result set attachment, to the specified recipients.<br />
This extended stored procedure uses SQL Mail to send the<br />
message.<br />
Let’s see now some examples of specific SQL Server attacks that<br />
use the aforementioned functions. Most of these examples will<br />
use the exec function.<br />
Below we show how to execute a shell command that writes the<br />
output of the command dir c:\inetpub in a browseable file, assuming<br />
that the web server and the DB server reside on the same<br />
host. The following syntax uses xp_cmdshell:<br />
exec master.dbo.xp_cmdshell ‘dir c:\inetpub > c:\inetpub\<br />
wwwroot\test.txt’--<br />
Alternatively, we can use sp_makewebtask:<br />
exec sp_makewebtask ‘C:\Inetpub\wwwroot\test.txt’,<br />
‘select * from master.dbo.sysobjects’--<br />
A successful execution will create a file that can be browsed by<br />
the pen tester. Keep in mind that sp_makewebtask is deprecated,<br />
and, even if it works in all SQL Server versions up to 2005, it might<br />
be removed in the future.<br />
In addition, SQL Server built-in functions and environment variables<br />
are very handy. The following uses the function db_name()<br />
to trigger an error that will return the name of the database:<br />
/controlboard.asp?boardID=2&itemnum=1%20AND%20<br />
1=CONVERT(int,%20db_name())<br />
Notice the use of [convert]:<br />
CONVERT ( data_type [ ( length ) ] , expression [ , style ] )<br />
CONVERT will try to convert the result of db_name (a string) into<br />
an integer variable, triggering an error, which, if displayed by the<br />
vulnerable application, will contain the name of the DB.<br />
The following example uses the environment variable @@version<br />
, combined with a “union select”-style injection, in order to find the<br />
version of the SQL Server.<br />
/form.asp?prop=33%20union%20select%20<br />
1,2006-01-06,2007-01-06,1,’stat’,’name1’,’na<br />
me2’,2006-01-06,1,@@version%20--<br />
And here’s the same attack, but using again the conversion trick:<br />
/form.asp?prop=33%20union%20select%20<br />
1,2006-01-06,2007-01-06,1,’stat’,’name1’,’na<br />
me2’,2006-01-06,1,@@version%20--<br />
Information gathering is useful for exploiting software vulnerabilities<br />
at the SQL Server, through the exploitation of an SQL-injection<br />
attack or direct access to the SQL listener.<br />
In the following, we show several examples that exploit SQL injection<br />
vulnerabilities through different entry points.<br />
Example 1: Testing for SQL Injection in a GET request.<br />
The most simple (and sometimes most rewarding) case would be<br />
that of a login page requesting an user name and password for<br />
user login. You can try entering the following string “’ or ‘1’=’1”<br />
(without double quotes):<br />
https: /vulnerable.web.app/login.asp?Username=’%20or%20<br />
’1’=’1&Password=’%20or%20’1’=’1<br />
If the application is using Dynamic SQL queries, and the string gets<br />
appended to the user credentials validation query, this may result<br />
in a successful login to the application.<br />
Example 2: Testing for SQL Injection in a GET request<br />
In order to learn how many columns exist<br />
https: /vulnerable.web.app/list_report.aspx?number=001%20UNION%20ALL%201,1,’a’,1,1,1%20FROM%20<br />
users;--<br />
Example 3: Testing in a POST request<br />
SQL Injection, HTTP POST Content: email=%27&whichSubmit=submit&submit.x=0&submit.y=0<br />
A complete post example:<br />
POST https: /vulnerable.web.app/forgotpass.asp HTTP/1.1<br />
Host: vulnerable.web.app<br />
User-Agent: Mozilla/5.0 (Windows; U; Windows NT 5.1; en-<br />
US; rv:1.8.0.7) Gecko/20060909 Firefox/1.5.0.7 Paros/3.2.13