4.0
1NSchAb
1NSchAb
- No tags were found...
Create successful ePaper yourself
Turn your PDF publications into a flip-book with our unique Google optimized e-Paper software.
58<br />
Web Application Penetration Testing<br />
example the netsparker dictionary.<br />
References<br />
• Default Password list: http:/www.governmentsecurity.org/articles/<br />
DefaultLoginsandPasswordsforNetworkedDevices.php<br />
• Default Password list: http:/www.cirt.net/passwords<br />
Test HTTP Methods (OTG-CONFIG-006)<br />
Summary<br />
HTTP offers a number of methods that can be used to perform actions<br />
on the web server. Many of theses methods are designed to aid<br />
developers in deploying and testing HTTP applications. These HTTP<br />
methods can be used for nefarious purposes if the web server is misconfigured.<br />
Additionally, Cross Site Tracing (XST), a form of cross site<br />
scripting using the server’s HTTP TRACE method, is examined.<br />
While GET and POST are by far the most common methods that are<br />
used to access information provided by a web server, the Hypertext<br />
Transfer Protocol (HTTP) allows several other (and somewhat less<br />
known) methods. RFC 2616 (which describes HTTP version 1.1 which<br />
is the standard today) defines the following eight methods:<br />
• HEAD<br />
• GET<br />
• POST<br />
• PUT<br />
• DELETE<br />
• TRACE<br />
• OPTIONS<br />
• CONNECT<br />
Some of these methods can potentially pose a security risk for a web<br />
application, as they allow an attacker to modify the files stored on the<br />
web server and, in some scenarios, steal the credentials of legitimate<br />
users. More specifically, the methods that should be disabled are the<br />
following:<br />
• PUT: This method allows a client to upload new files on the web<br />
server. An attacker can exploit it by uploading malicious files (e.g.: an<br />
asp file that executes commands by invoking cmd.exe), or by simply<br />
using the victim’s server as a file repository.<br />
• DELETE: This method allows a client to delete a file on the web<br />
server. An attacker can exploit it as a very simple and direct way to<br />
deface a web site or to mount a DoS attack.<br />
• CONNECT: This method could allow a client to use the web server<br />
as a proxy.<br />
• TRACE: This method simply echoes back to the client whatever<br />
string has been sent to the server, and is used mainly for debugging<br />
purposes. This method, originally assumed harmless, can be used to<br />
mount an attack known as Cross Site Tracing, which has been discovered<br />
by Jeremiah Grossman (see links at the bottom of the page).<br />
If an application needs one or more of these methods, such as REST<br />
Web Services (which may require PUT or DELETE), it is important to<br />
check that their usage is properly limited to trusted users and safe<br />
conditions.<br />
Arbitrary HTTP Methods<br />
Arshan Dabirsiaghi (see links) discovered that many web application<br />
frameworks allowed well chosen or arbitrary HTTP methods to bypass<br />
an environment level access control check:<br />
• Many frameworks and languages treat “HEAD” as a “GET” request,<br />
albeit one without any body in the response. If a security constraint<br />
was set on “GET” requests such that only “authenticatedUsers”<br />
could access GET requests for a particular servlet or resource,<br />
it would be bypassed for the “HEAD” version. This allowed<br />
unauthorized blind submission of any privileged GET request.<br />
• Some frameworks allowed arbitrary HTTP methods such as “JEFF”<br />
or “CATS” to be used without limitation. These were treated as if<br />
a “GET” method was issued, and were found not to be subject to<br />
method role based access control checks on a number of languages<br />
and frameworks, again allowing unauthorized blind submission of<br />
privileged GET requests.<br />
In many cases, code which explicitly checked for a “GET” or “POST”<br />
method would be safe.<br />
How to Test<br />
Discover the Supported Methods<br />
To perform this test, the tester needs some way to figure out which<br />
HTTP methods are supported by the web server that is being examined.<br />
The OPTIONS HTTP method provides the tester with the most<br />
direct and effective way to do that. RFC 2616 states that, “The OP-<br />
TIONS method represents a request for information about the communication<br />
options available on the request/response chain identified<br />
by the Request-URI”.<br />
The testing method is extremely straightforward and we only need to<br />
fire up netcat (or telnet):<br />
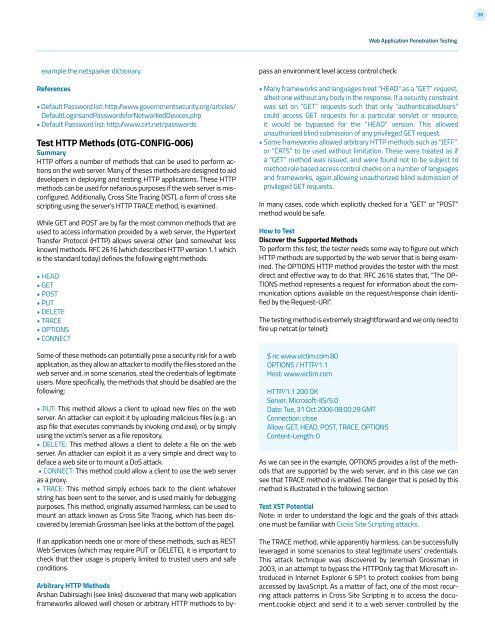
$ nc www.victim.com 80<br />
OPTIONS / HTTP/1.1<br />
Host: www.victim.com<br />
HTTP/1.1 200 OK<br />
Server: Microsoft-IIS/5.0<br />
Date: Tue, 31 Oct 2006 08:00:29 GMT<br />
Connection: close<br />
Allow: GET, HEAD, POST, TRACE, OPTIONS<br />
Content-Length: 0<br />
As we can see in the example, OPTIONS provides a list of the methods<br />
that are supported by the web server, and in this case we can<br />
see that TRACE method is enabled. The danger that is posed by this<br />
method is illustrated in the following section<br />
Test XST Potential<br />
Note: in order to understand the logic and the goals of this attack<br />
one must be familiar with Cross Site Scripting attacks.<br />
The TRACE method, while apparently harmless, can be successfully<br />
leveraged in some scenarios to steal legitimate users’ credentials.<br />
This attack technique was discovered by Jeremiah Grossman in<br />
2003, in an attempt to bypass the HTTPOnly tag that Microsoft introduced<br />
in Internet Explorer 6 SP1 to protect cookies from being<br />
accessed by JavaScript. As a matter of fact, one of the most recurring<br />
attack patterns in Cross Site Scripting is to access the document.cookie<br />
object and send it to a web server controlled by the