4.0
1NSchAb
1NSchAb
- No tags were found...
You also want an ePaper? Increase the reach of your titles
YUMPU automatically turns print PDFs into web optimized ePapers that Google loves.
65<br />
Web Application Penetration Testing<br />
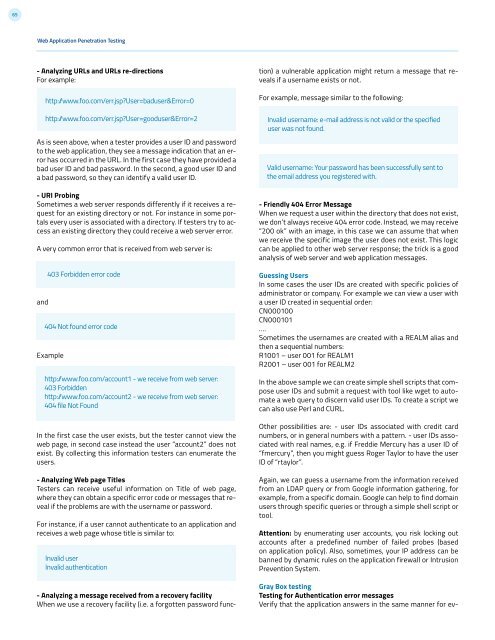
- Analyzing URLs and URLs re-directions<br />
For example:<br />
As is seen above, when a tester provides a user ID and password<br />
to the web application, they see a message indication that an error<br />
has occurred in the URL. In the first case they have provided a<br />
bad user ID and bad password. In the second, a good user ID and<br />
a bad password, so they can identify a valid user ID.<br />
- URI Probing<br />
Sometimes a web server responds differently if it receives a request<br />
for an existing directory or not. For instance in some portals<br />
every user is associated with a directory. If testers try to access<br />
an existing directory they could receive a web server error.<br />
A very common error that is received from web server is:<br />
and<br />
http:/www.foo.com/err.jsp?User=baduser&Error=0<br />
http:/www.foo.com/err.jsp?User=gooduser&Error=2<br />
403 Forbidden error code<br />
404 Not found error code<br />
Example<br />
http:/www.foo.com/account1 - we receive from web server:<br />
403 Forbidden<br />
http:/www.foo.com/account2 - we receive from web server:<br />
404 file Not Found<br />
In the first case the user exists, but the tester cannot view the<br />
web page, in second case instead the user “account2” does not<br />
exist. By collecting this information testers can enumerate the<br />
users.<br />
- Analyzing Web page Titles<br />
Testers can receive useful information on Title of web page,<br />
where they can obtain a specific error code or messages that reveal<br />
if the problems are with the username or password.<br />
For instance, if a user cannot authenticate to an application and<br />
receives a web page whose title is similar to:<br />
Invalid user<br />
Invalid authentication<br />
- Analyzing a message received from a recovery facility<br />
When we use a recovery facility (i.e. a forgotten password func-<br />
tion) a vulnerable application might return a message that reveals<br />
if a username exists or not.<br />
For example, message similar to the following:<br />
Invalid username: e-mail address is not valid or the specified<br />
user was not found.<br />
Valid username: Your password has been successfully sent to<br />
the email address you registered with.<br />
- Friendly 404 Error Message<br />
When we request a user within the directory that does not exist,<br />
we don’t always receive 404 error code. Instead, we may receive<br />
“200 ok” with an image, in this case we can assume that when<br />
we receive the specific image the user does not exist. This logic<br />
can be applied to other web server response; the trick is a good<br />
analysis of web server and web application messages.<br />
Guessing Users<br />
In some cases the user IDs are created with specific policies of<br />
administrator or company. For example we can view a user with<br />
a user ID created in sequential order:<br />
CN000100<br />
CN000101<br />
….<br />
Sometimes the usernames are created with a REALM alias and<br />
then a sequential numbers:<br />
R1001 – user 001 for REALM1<br />
R2001 – user 001 for REALM2<br />
In the above sample we can create simple shell scripts that compose<br />
user IDs and submit a request with tool like wget to automate<br />
a web query to discern valid user IDs. To create a script we<br />
can also use Perl and CURL.<br />
Other possibilities are: - user IDs associated with credit card<br />
numbers, or in general numbers with a pattern. - user IDs associated<br />
with real names, e.g. if Freddie Mercury has a user ID of<br />
“fmercury”, then you might guess Roger Taylor to have the user<br />
ID of “rtaylor”.<br />
Again, we can guess a username from the information received<br />
from an LDAP query or from Google information gathering, for<br />
example, from a specific domain. Google can help to find domain<br />
users through specific queries or through a simple shell script or<br />
tool.<br />
Attention: by enumerating user accounts, you risk locking out<br />
accounts after a predefined number of failed probes (based<br />
on application policy). Also, sometimes, your IP address can be<br />
banned by dynamic rules on the application firewall or Intrusion<br />
Prevention System.<br />
Gray Box testing<br />
Testing for Authentication error messages<br />
Verify that the application answers in the same manner for ev-