4.0
1NSchAb
1NSchAb
- No tags were found...
You also want an ePaper? Increase the reach of your titles
YUMPU automatically turns print PDFs into web optimized ePapers that Google loves.
129<br />
Web Application Penetration Testing<br />
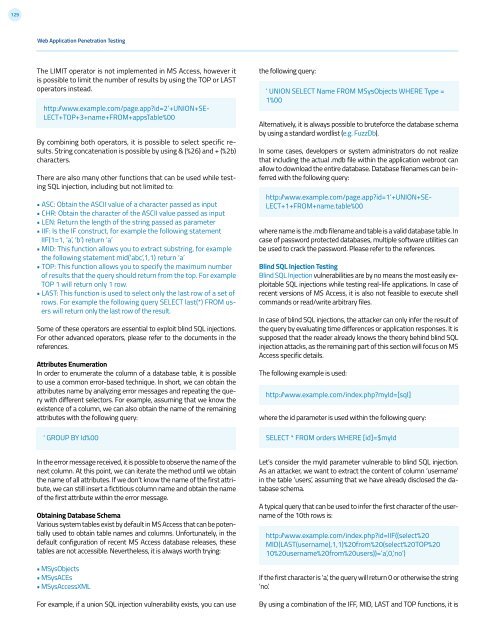
The LIMIT operator is not implemented in MS Access, however it<br />
is possible to limit the number of results by using the TOP or LAST<br />
operators instead.<br />
http: /www.example.com/page.app?id=2’+UNION+SE-<br />
LECT+TOP+3+name+FROM+appsTable%00<br />
By combining both operators, it is possible to select specific results.<br />
String concatenation is possible by using & (%26) and + (%2b)<br />
characters.<br />
There are also many other functions that can be used while testing<br />
SQL injection, including but not limited to:<br />
• ASC: Obtain the ASCII value of a character passed as input<br />
• CHR: Obtain the character of the ASCII value passed as input<br />
• LEN: Return the length of the string passed as parameter<br />
• IIF: Is the IF construct, for example the following statement<br />
IIF(1=1, ‘a’, ‘b’) return ‘a’<br />
• MID: This function allows you to extract substring, for example<br />
the following statement mid(‘abc’,1,1) return ‘a’<br />
• TOP: This function allows you to specify the maximum number<br />
of results that the query should return from the top. For example<br />
TOP 1 will return only 1 row.<br />
• LAST: This function is used to select only the last row of a set of<br />
rows. For example the following query SELECT last(*) FROM users<br />
will return only the last row of the result.<br />
Some of these operators are essential to exploit blind SQL injections.<br />
For other advanced operators, please refer to the documents in the<br />
references.<br />
Attributes Enumeration<br />
In order to enumerate the column of a database table, it is possible<br />
to use a common error-based technique. In short, we can obtain the<br />
attributes name by analyzing error messages and repeating the query<br />
with different selectors. For example, assuming that we know the<br />
existence of a column, we can also obtain the name of the remaining<br />
attributes with the following query:<br />
‘ GROUP BY Id%00<br />
the following query:<br />
‘ UNION SELECT Name FROM MSysObjects WHERE Type =<br />
1%00<br />
Alternatively, it is always possible to bruteforce the database schema<br />
by using a standard wordlist (e.g. FuzzDb).<br />
In some cases, developers or system administrators do not realize<br />
that including the actual .mdb file within the application webroot can<br />
allow to download the entire database. Database filenames can be inferred<br />
with the following query:<br />
http: /www.example.com/page.app?id=1’+UNION+SE-<br />
LECT+1+FROM+name.table%00<br />
where name is the .mdb filename and table is a valid database table. In<br />
case of password protected databases, multiple software utilities can<br />
be used to crack the password. Please refer to the references.<br />
Blind SQL Injection Testing<br />
Blind SQL Injection vulnerabilities are by no means the most easily exploitable<br />
SQL injections while testing real-life applications. In case of<br />
recent versions of MS Access, it is also not feasible to execute shell<br />
commands or read/write arbitrary files.<br />
In case of blind SQL injections, the attacker can only infer the result of<br />
the query by evaluating time differences or application responses. It is<br />
supposed that the reader already knows the theory behind blind SQL<br />
injection attacks, as the remaining part of this section will focus on MS<br />
Access specific details.<br />
The following example is used:<br />
http: /www.example.com/index.php?myId=[sql]<br />
where the id parameter is used within the following query:<br />
SELECT * FROM orders WHERE [id]=$myId<br />
In the error message received, it is possible to observe the name of the<br />
next column. At this point, we can iterate the method until we obtain<br />
the name of all attributes. If we don’t know the name of the first attribute,<br />
we can still insert a fictitious column name and obtain the name<br />
of the first attribute within the error message.<br />
Obtaining Database Schema<br />
Various system tables exist by default in MS Access that can be potentially<br />
used to obtain table names and columns. Unfortunately, in the<br />
default configuration of recent MS Access database releases, these<br />
tables are not accessible. Nevertheless, it is always worth trying:<br />
• MSysObjects<br />
• MSysACEs<br />
• MSysAccessXML<br />
For example, if a union SQL injection vulnerability exists, you can use<br />
Let’s consider the myId parameter vulnerable to blind SQL injection.<br />
As an attacker, we want to extract the content of column ‘username’<br />
in the table ‘users’, assuming that we have already disclosed the database<br />
schema.<br />
A typical query that can be used to infer the first character of the username<br />
of the 10th rows is:<br />
http: /www.example.com/index.php?id=IIF((select%20<br />
MID(LAST(username),1,1)%20from%20(select%20TOP%20<br />
10%20username%20from%20users))=’a’,0,’no’)<br />
If the first character is ‘a’, the query will return 0 or otherwise the string<br />
‘no’.<br />
By using a combination of the IFF, MID, LAST and TOP functions, it is