4.0
1NSchAb
1NSchAb
- No tags were found...
Create successful ePaper yourself
Turn your PDF publications into a flip-book with our unique Google optimized e-Paper software.
209<br />
same code can be applied to sessionStorage<br />
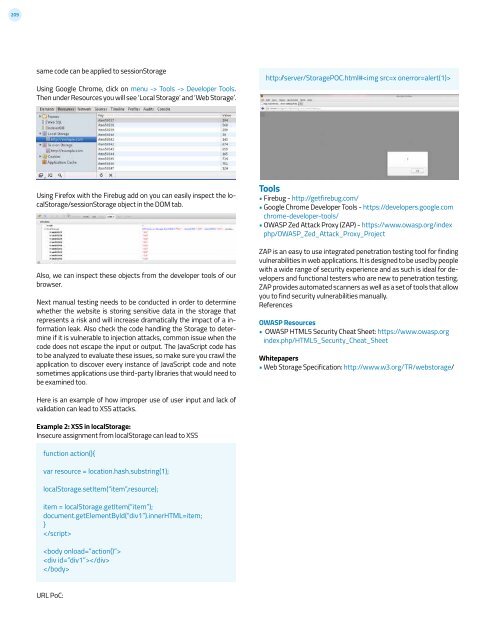
Using Google Chrome, click on menu -> Tools -> Developer Tools.<br />
Then under Resources you will see ‘Local Storage’ and ‘Web Storage’.<br />
http: /server/StoragePOC.html#<br />
Using Firefox with the Firebug add on you can easily inspect the localStorage/sessionStorage<br />
object in the DOM tab.<br />
Also, we can inspect these objects from the developer tools of our<br />
browser.<br />
Next manual testing needs to be conducted in order to determine<br />
whether the website is storing sensitive data in the storage that<br />
represents a risk and will increase dramatically the impact of a information<br />
leak. Also check the code handling the Storage to determine<br />
if it is vulnerable to injection attacks, common issue when the<br />
code does not escape the input or output. The JavaScript code has<br />
to be analyzed to evaluate these issues, so make sure you crawl the<br />
application to discover every instance of JavaScript code and note<br />
sometimes applications use third-party libraries that would need to<br />
be examined too.<br />
Tools<br />
• Firebug - http://getfirebug.com/<br />
• Google Chrome Developer Tools - https://developers.google.com<br />
chrome-developer-tools/<br />
• OWASP Zed Attack Proxy (ZAP) - https://www.owasp.org/index<br />
php/OWASP_Zed_Attack_Proxy_Project<br />
ZAP is an easy to use integrated penetration testing tool for finding<br />
vulnerabilities in web applications. It is designed to be used by people<br />
with a wide range of security experience and as such is ideal for developers<br />
and functional testers who are new to penetration testing.<br />
ZAP provides automated scanners as well as a set of tools that allow<br />
you to find security vulnerabilities manually.<br />
References<br />
OWASP Resources<br />
• OWASP HTML5 Security Cheat Sheet: https://www.owasp.org<br />
index.php/HTML5_Security_Cheat_Sheet<br />
Whitepapers<br />
• Web Storage Specification: http://www.w3.org/TR/webstorage/<br />
Here is an example of how improper use of user input and lack of<br />
validation can lead to XSS attacks.<br />
Example 2: XSS in localStorage:<br />
Insecure assignment from localStorage can lead to XSS<br />
function action(){<br />
var resource = location.hash.substring(1);<br />
localStorage.setItem(“item”,resource);<br />
item = localStorage.getItem(“item”);<br />
document.getElementById(“div1”).innerHTML=item;<br />
}<br />
<br />
<br />
<br />
<br />
URL PoC: