4.0
1NSchAb
1NSchAb
- No tags were found...
You also want an ePaper? Increase the reach of your titles
YUMPU automatically turns print PDFs into web optimized ePapers that Google loves.
125<br />
Web Application Penetration Testing<br />
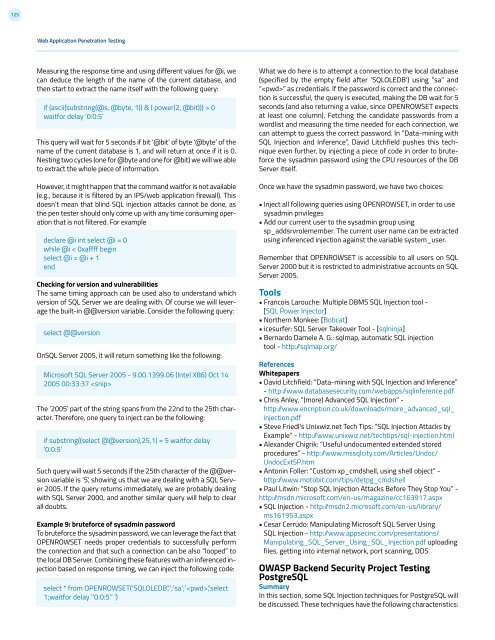
Measuring the response time and using different values for @i, we<br />
can deduce the length of the name of the current database, and<br />
then start to extract the name itself with the following query:<br />
if (ascii(substring(@s, @byte, 1)) & ( power(2, @bit))) > 0<br />
waitfor delay ‘0:0:5’<br />
This query will wait for 5 seconds if bit ‘@bit’ of byte ‘@byte’ of the<br />
name of the current database is 1, and will return at once if it is 0.<br />
Nesting two cycles (one for @byte and one for @bit) we will we able<br />
to extract the whole piece of information.<br />
However, it might happen that the command waitfor is not available<br />
(e.g., because it is filtered by an IPS/web application firewall). This<br />
doesn’t mean that blind SQL injection attacks cannot be done, as<br />
the pen tester should only come up with any time consuming operation<br />
that is not filtered. For example<br />
declare @i int select @i = 0<br />
while @i < 0xaffff begin<br />
select @i = @i + 1<br />
end<br />
Checking for version and vulnerabilities<br />
The same timing approach can be used also to understand which<br />
version of SQL Server we are dealing with. Of course we will leverage<br />
the built-in @@version variable. Consider the following query:<br />
select @@version<br />
OnSQL Server 2005, it will return something like the following:<br />
Microsoft SQL Server 2005 - 9.00.1399.06 (Intel X86) Oct 14<br />
2005 00:33:37 <br />
The ‘2005’ part of the string spans from the 22nd to the 25th character.<br />
Therefore, one query to inject can be the following:<br />
if substring((select @@version),25,1) = 5 waitfor delay<br />
‘0:0:5’<br />
Such query will wait 5 seconds if the 25th character of the @@version<br />
variable is ‘5’, showing us that we are dealing with a SQL Server<br />
2005. If the query returns immediately, we are probably dealing<br />
with SQL Server 2000, and another similar query will help to clear<br />
all doubts.<br />
Example 9: bruteforce of sysadmin password<br />
To bruteforce the sysadmin password, we can leverage the fact that<br />
OPENROWSET needs proper credentials to successfully perform<br />
the connection and that such a connection can be also “looped” to<br />
the local DB Server. Combining these features with an inferenced injection<br />
based on response timing, we can inject the following code:<br />
select * from OPENROWSET(‘SQLOLEDB’,’’;’sa’;’’,’select<br />
1;waitfor delay ‘’0:0:5’’ ‘)<br />
What we do here is to attempt a connection to the local database<br />
(specified by the empty field after ‘SQLOLEDB’) using “sa” and<br />
“” as credentials. If the password is correct and the connection<br />
is successful, the query is executed, making the DB wait for 5<br />
seconds (and also returning a value, since OPENROWSET expects<br />
at least one column). Fetching the candidate passwords from a<br />
wordlist and measuring the time needed for each connection, we<br />
can attempt to guess the correct password. In “Data-mining with<br />
SQL Injection and Inference”, David Litchfield pushes this technique<br />
even further, by injecting a piece of code in order to bruteforce<br />
the sysadmin password using the CPU resources of the DB<br />
Server itself.<br />
Once we have the sysadmin password, we have two choices:<br />
• Inject all following queries using OPENROWSET, in order to use<br />
sysadmin privileges<br />
• Add our current user to the sysadmin group using<br />
sp_addsrvrolemember. The current user name can be extracted<br />
using inferenced injection against the variable system_user.<br />
Remember that OPENROWSET is accessible to all users on SQL<br />
Server 2000 but it is restricted to administrative accounts on SQL<br />
Server 2005.<br />
Tools<br />
• Francois Larouche: Multiple DBMS SQL Injection tool -<br />
[SQL Power Injector]<br />
• Northern Monkee: [Bobcat]<br />
• icesurfer: SQL Server Takeover Tool - [sqlninja]<br />
• Bernardo Damele A. G.: sqlmap, automatic SQL injection<br />
tool - http: /sqlmap.org/<br />
References<br />
Whitepapers<br />
• David Litchfield: “Data-mining with SQL Injection and Inference”<br />
- http: /www.databasesecurity.com/webapps/sqlinference.pdf<br />
• Chris Anley, “(more) Advanced SQL Injection” -<br />
http: /www.encription.co.uk/downloads/more_advanced_sql_<br />
injection.pdf<br />
• Steve Friedl’s Unixwiz.net Tech Tips: “SQL Injection Attacks by<br />
Example” - http: /www.unixwiz.net/techtips/sql-injection.html<br />
• Alexander Chigrik: “Useful undocumented extended stored<br />
procedures” - http: /www.mssqlcity.com/Articles/Undoc/<br />
UndocExtSP.htm<br />
• Antonin Foller: “Custom xp_cmdshell, using shell object” -<br />
http: /www.motobit.com/tips/detpg_cmdshell<br />
• Paul Litwin: “Stop SQL Injection Attacks Before They Stop You” -<br />
http: /msdn.microsoft.com/en-us/magazine/cc163917.aspx<br />
• SQL Injection - http: /msdn2.microsoft.com/en-us/library/<br />
ms161953.aspx<br />
• Cesar Cerrudo: Manipulating Microsoft SQL Server Using<br />
SQL Injection - http: /www.appsecinc.com/presentations/<br />
Manipulating_SQL_Server_Using_SQL_Injection.pdf uploading<br />
files, getting into internal network, port scanning, DOS<br />
OWASP Backend Security Project Testing<br />
PostgreSQL<br />
Summary<br />
In this section, some SQL Injection techniques for PostgreSQL will<br />
be discussed. These techniques have the following characteristics: